CYBERPUNK | The Best Tutorials & CyberSecurity Tool Reviews
CyberPunk: The Best Tutorials & CyberSecurity Tool Reviews. Get informed about the latest ethical hacking and cybersecurity tool releases. Read Cyberpunk's ethical hacking tutorials/articles and watch usage videos...

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en-US
Response Time: 0.686558
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 208
Links
ratio 9.1317630390507
SSL Details
SSL Issuer:
Issuer: R3
Valid From: 2022-05-22 08:13:20
Expiration Date: 2022-08-20 08:13:19
SSL Organization:
Signature 60a53bcff9d70c7a151e33ae8e280b614999ae06
Algorithm: RSA-SHA256
Found 74 Top Alternative to Cyberpunk.rs
 Kalilinuxtutorials.com
Kalilinuxtutorials.com
Kali Linux Tutorials - A Single Stop for Kali Linux Tools
Kali Linux tutorials is an independent platform that covers step by tutorials, advanced penetration testing, Ethical Hacking and network security tools.

 Pentesttools.net
Pentesttools.net
PentestTools - Penetration Testing Tools.
Latest Penetration Testing Tools. Cyber Security and Technology News. High Quality Penetration Testing Videos.
 Kali.tools
Kali.tools
Инструменты Kali Linux - Список инструментов для тестирования на проникновение и их описание
Сбор информации acccheck ace-voip Amap AQUATONE arp-scan Automater badKarma bing-ip2hosts braa Bro Bypass firewalls by abusing DNS history CaseFile CATPHISH CDPSnarf cisco-torch CloudFail Cookie Cadger copy-router-config DMitry dnmap dnsenum dnsmap DNSRecon dnstracer dnstwist dnswalk DotDotPwn Dublin Traceroute enum4linux enumIAX exploitdb EyeWitness Faraday FinalRecon Fierce Firewalk flashlight fragroute fragrouter Ghost Phisher...

 Bettercap.org
Bettercap.org
:: bettercap
Core events.stream ticker caplets update api.rest ui c2 Bluetooth LE WiFi HID on 2.4Ghz IPv4 / IPv6 net.recon net.probe net.sniff - net.fuzz syn.scan wake on lan Spoofers arp.spoof dns.spoof dhcp6.spoof ndp.spoof (IPv6) Proxies any.proxy packet.proxy tcp.proxy http.proxy https.proxy Servers http.server https.server mdns.server mysql.server (rogue) Utils mac.changer gps
 Prodefence.org
Prodefence.org
Prodefence - Cyber Security Services | Malware & Pentesting
Cyber security services - Malware analysis - Penetration testing - Data protection
 Kitploit.com
Kitploit.com
KitPloit - PenTest & Hacking Tools
Leading source of security tools, hacking tools, cybersecurity and network security. Learn about new tools and updates in one place.
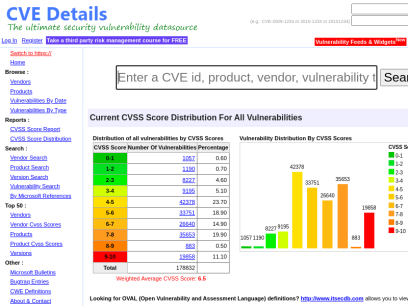
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Miloserdov.org
Miloserdov.org
Ethical hacking and penetration testing - InfoSec, IT, Kali Linux, BlackArch
The complete guide to Wine: from installation to advanced usage Table of contents 1. Why Wine 2. Features and limitations of Wine 3. 64-bit or 32-bit Wine? 4. How to install Wine 4.1 Installing Wine on Debian, Kali Linux, Linux Mint, Ubuntu, and their derivatives 4.2 Installing Wine on Arch Linux 5. How...

 Securityonline.info
Securityonline.info
Penetration Testing • Information Security
Securityonline is a huge security community. It is committed to the sharing of high-quality technical articles and safety reports, focusing on high-quality security and security incidents in the industry.

 Securitynewspaper.com
Securitynewspaper.com
Information Security News|Cyber Security|Hacking Tutorial
Information Security Newspaper covers cyber security news, data breaches, malware, hacking, vulnerabilities, mobile security & ethical hacking tutorials
 Myfrugalbusiness.com
Myfrugalbusiness.com
Bootstrap Business
Bootstrap Business Blog: Bootstrapping business ideas, blogger outreach, SEO and digital marketing for bootstrapped startups and frugal entrepreneurs.
 Rootsh3ll.com
Rootsh3ll.com
welcome to rootsh3ll
Learn Penetration Testing by practice... A massive brute-force attack hit our application server in mid-2018, with around 500,000 login attempts at peak in just one day. That's massive, and we wouldn't have survived if we didn't have the necessary security implementations in the system beforehand. Simply put, we hacked our...
 Sectechno.com
Sectechno.com
Работа сайта временно приостановлена
Работа сайта временно приостановлена Хостинг сайта временно приостановлен Если вы владелец данного ресурса, то для возобновления работы сайта вам необходимо продлить действие услуги хостинга. Продлить В случае, если приостановка работы сайта вызвана нарушением условий Договора на абонентское обслуживание, то для возобновления работы вам необходимо обратиться в Службу поддержки. Мы будем рады вам помочь!

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.

 Linuxsecurity.expert
Linuxsecurity.expert
Where experts are trained - Linux Security Expert
The community where Linux security experts are being trained. Learn everything there it to know about system security, tools, and implementation.
 Hacking.land
Hacking.land
Hacking Land - Hack, Crack and Pentest
¿Recuerdan cuándo todo se hackeaba con Telnet y una IP? Pues bueno, hoy no...

 Enciphers.com
Enciphers.com
Penetration Testing | Vulnerability Assessment | Security Training
Advance Penetration Testing, Vulnerability Assessment, Security Training
 Kalitut.com
Kalitut.com
KaliTut Linux and pentesting blog - KaliTut
Windows PowerShell tutorial for beginners Detailed PowerShell tutorial for beginners! ✓ Create and run PowerShell script, practice-oriented knowledge about PowerShell. Learn to Hack Steps from Beginner to Hacker Learn to hack , Beginner's Guide - with some many Tutorials on how to Hack Computers with Kali Install Linux PowerShell Tutorial...
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.

 Vpnetic.com
Vpnetic.com
Vpnetic: Best VPN Data and Statistics 2022 🎖️
These VPN services were ranked by their privacy policies, data logging, company history, government cooperation and more. ⭐

 Privacycritic.com
Privacycritic.com
How to stay safe online: a Privacy and Security Guide | Privacycritic.com
What is online safety, and how to stay safe online? It is keeping yourself and what you do on the internet safe and anonymous.

 Digitogy.com
Digitogy.com
Digitogy.com | Digitogy.com
Tech advice you can count on - It's time for an honest Tech review site Unbiased, in-depth Tech Reviews & Latest Industry News smartDOT Review :

 Hackmod.de
Hackmod.de
HackmoD - IT-Security & Pentest Tools
Hackmod IT-Security: IT-Security, RFID-Security, Pentest Tools, Pentesting, IoT Security, Hak5. Datensicherheit für Ihr Netzwerk.
 Hacking.reviews
Hacking.reviews
Hacking Reviews
Leading source of Hacking News, Information Security, Cyber Security, and Network Security.

 Briskinfosec.com
Briskinfosec.com
Cyber Security Company in India | Cloud, IOT, Web Application Testing and Information Security Consulting Services Provider - Briskinfosec | Briskinfosec
Briskinfosec is a global cyber security company, our expert security consultants delivering innovative security assessment services and IT compliance solutions such as HIPAA ISO 27001 PCIDSS GDPR CCPA SSAE.

 Hackingtools.in
Hackingtools.in
Hacking Trainer - Ethical Hacking Training in Hyderabad
Hacking Trainer is a unit of BERRY9 IT SERVICES Pvt. Ltd and EC-Council ATC. We offer Ethical Hacking Training and InfoSec Certifications.
 Charlesreid1.com
Charlesreid1.com
charlesreid1
wiki: charlesreid1.com/wiki the wiki is a compilation of reading material, notes, scripts, logs, guides, lecture notes, and scattered thoughts. gitea: git.charlesreid1.com git.charlesreid1.com is where all of my code projects are hosted. gitea is a self-hosted github clone written in go. github: @charlesreid1 follow my coding work on github....

 Stuartkerrs.com
Stuartkerrs.com
Digital Marketing Consultant London | Stuart Kerrs
Stuart Kerrs is a Digital Marketing Consultant in London providing affordable services from our digital marketing consultancy in London.
 Hydrasky.com
Hydrasky.com
All things in moderation – We are local security
+ UAC BYPASS VIA DOTNET PROFILER ON WINDOWS 10 Vulnerabilities and Exploits In the previous post, we know how to use Registry Hijacking to bypass UAC on Windows 10. Today, we continue to do that with different technique with … By Stephen Stinson May 20, 2020 + + UAC Bypass Via...

 Blackarch.org
Blackarch.org
BlackArch Linux - Penetration Testing Distribution
BlackArch Linux is a lightweight expansion to Arch Linux for penetration testers.


 Evilsocket.net
Evilsocket.net
evilsocket
Hi, my name is Simone (a male name in my country) and on the internet I'm known as evilsocket. I like computers, music, dogs, [books](https://www.goodreads.com/evilsocket), physics, [photography and t

 Hakin9.org
Hakin9.org
Home - Hakin9 - IT Security Magazine
Our tutorials, case studies and online courses will prepare you for the upcoming, potential threats in the cyber security world.
 Hackingloops.com
Hackingloops.com
Learn Ethical Hacking and Penetration Testing Online | Learn ethical hacking, penetration testing, cyber security, best security and web penetration testing techniques from best ethical hackers in security field.
Learn ethical hacking, penetration testing, cyber security, best security and web penetration testing techniques from best ethical hackers in security field.

 Latesthackingnews.com
Latesthackingnews.com
Latest Hacking News - We offer the latest hacking news and cyber security courses for ethical hackers, penetration testers, IT security experts and essentially anyone with hacker interests.
We offer the latest hacking news and cyber security courses for ethical hackers, penetration testers, IT security experts and essentially anyone with hacker interests.

 Aircrack-ng.org
Aircrack-ng.org
Aircrack-ng
Fresh news Aircrack-ng 1.7 10 May 22 After more than 2 years, we are making a release with a decently large amount of fixes, improvements, and additions. We also broke the 4000 commits barrier, and this release has more than 400 commits. Read more in our detailed blog post. PackageCloud.io...

 Zsecurity.org
Zsecurity.org
zSecurity – Ethical Hacking Courses, Tutorials, News, Products and more!
Hacking Masterclass by Zaid > Zaid’s NEWEST course. > Exclusive to zSecurity. > Enrol now and get 30% off. More information 745200 Students 1013150 Followers 219 Countries Latest Posts In Hacking & Security Capstone Challenge | Linux Privilege Escalation Linux Privilege Escalation: NFS || Episode 9 DNS Spoofing Basics with...

 Darknet.org.uk
Darknet.org.uk
Darknet - Hacking Tools, Hacker News & Cyber Security
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.

 Kalilinux.in
Kalilinux.in
Best Kali Linux Tutorials
Best Place for Kali Linux Tutorials. Large number of articles on Kali Linux in easy steps from basic to advanced. Command by command with screenshots.

 Hackingvision.com
Hackingvision.com
HackingVision – Ethical Hacking Tutorials, Tips & Tricks, Kali Linux, Beginners Hacking
Top Colleges for Cybersecurity Degree Programs 1st June 2022 by Carl Hill Cybersecurity has a great job market with many job vacancies and attractive salaries. When you have a cybersecurity degree, you can easily find job opportunities such as security engineers. Therefore, training begins at the college level when you...

 Techgenez.com
Techgenez.com
TechGenez - Connecting You to Technology
TechGenez is on a mission of "Connecting You to Technology" . Bringing you all the top tech contents around the world. Click the link #TechGenez

 Frida.re
Frida.re
Frida • A world-class dynamic instrumentation framework | Inject JavaScript to explore native apps on Windows, macOS, GNU/Linux, iOS, Android, and QNX
Inject JavaScript to explore native apps on Windows, macOS, GNU/Linux, iOS, Android, and QNX

 N0where.net
N0where.net
CyberPunk Network
Welcome to CyberPunk PLTG Trix. No ELSUR. No ELINT. No censorship. No Ads. No data mining. No tracking. No Spyware.

 8bitsumo.com
8bitsumo.com
Welcome! Protect Your Crypto and Online Privacy with 8bit Sumo. » 8bit Sumo
Crypto and online privacy are two of the most pressing issues in today's world. I help people get knowledge about these topics so they can make informed
Technologies Used by cyberpunk.rs
Dns Records of cyberpunk.rs
A Record: 142.44.164.63AAAA Record:
CNAME Record:
NS Record: coby.ns.cloudflare.com amanda.ns.cloudflare.com
SOA Record: dns.cloudflare.com
MX Record: cyberpunk.rs
SRV Record:
TXT Record: v=spf1mx-all
DNSKEY Record:
CAA Record:
Whois Detail of cyberpunk.rs
% The data in the Whois database are provided by RNIDS
% for information purposes only and to assist persons in obtaining
% information about or related to a domain name registration record.
% Data in the database are created by registrants and we do not guarantee
% their accuracy. We reserve the right to remove access
% for entities abusing the data, without notice.
% All timestamps are given in Serbian local time.
%
Domain name: cyberpunk.rs
Domain status: Active https://www.rnids.rs/en/domain-name-status-codes#Active
Registration date: 20.02.2018 16:20:24
Modification date: 13.02.2022 16:05:13
Expiration date: 20.02.2023 16:20:24
Confirmed: 03.03.2018 17:39:02
Registrar: Loopia d.o.o.
Whois privacy has been activated for domain.
DNS: coby.ns.cloudflare.com -
DNS: amanda.ns.cloudflare.com - 173.245.58.63
DNSSEC signed: no
Whois Timestamp: 20.06.2022 20:25:58
 198.187.29.23
198.187.29.23
 United States
United States
 Valid SSL
Valid SSL