Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time:
SSL: Disable
Status: up
Code To Txt Ratio
Word Count
Links
ratio
Found 21 Top Alternative to Heartbleed.com

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.

 Openssl.org
Openssl.org
/index.html
The OpenSSL Project develops and maintains the OpenSSL software - a robust, commercial-grade, full-featured toolkit for general-purpose cryptography and secure communication. The project's technical decision making is managed by the OpenSSL Technical Committee (OTC) and the project governance is managed by the OpenSSL Management Committee (OMC). The project operates under...

 Comodoca.com
Comodoca.com
Sectigo
comodoca.com is using a security service for protection against online attacks. The service requires full cookie support in order to view this website.

 Meltdownattack.com
Meltdownattack.com
Meltdown and Spectre
Questions & Answers Am I affected by the vulnerability? Most certainly, yes. Can I detect if someone has exploited Meltdown or Spectre against me? Probably not. The exploitation does not leave any traces in traditional log files. Can my antivirus detect or block this attack? While possible in theory, this...
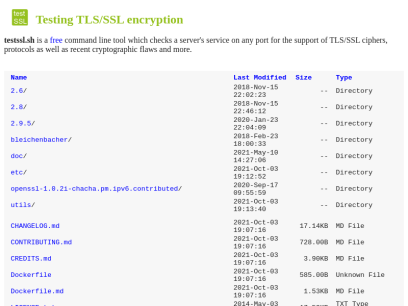
 Testssl.sh
Testssl.sh
/bin/bash based SSL/TLS tester: testssl.sh
TLS/SSL security testing with Open Source Software

 Hakin9.org
Hakin9.org
Home - Hakin9 - IT Security Magazine
Our tutorials, case studies and online courses will prepare you for the upcoming, potential threats in the cyber security world.
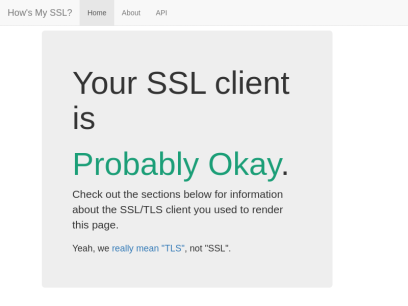
 Howsmyssl.com
Howsmyssl.com
How's My SSL?
Your SSL client is Probably Okay. Check out the sections below for information about the SSL/TLS client you used to render this page. Yeah, we really mean "TLS", not "SSL". Version Good Your client is using TLS 1.3, the most modern version of the encryption protocol. It gives you access...

 Filippo.io
Filippo.io
Filippo Valsorda
Filippo Valsorda I'm a cryptography engineer and open source maintainer. I've been in charge of cryptography and security on the Go team at Google until 2022, and was on the Cryptography team at Cloudflare until 2017. Read more about what I do and how we might know each other. I...

 Krackattacks.com
Krackattacks.com
KRACK Attacks: Breaking WPA2
This website presents the Key Reinstallation Attack (KRACK). It breaks the WPA2 protocol by forcing nonce reuse in encryption algorithms used by Wi-Fi.
 Feistyduck.com
Feistyduck.com
Feisty Duck | SSL/TLS and PKI training and books
Leading Companies Trust Us for TLS and PKI Education Practical TLS and PKI This practical training course will teach you how to deploy secure servers and encrypted web applications and understand both the theory and practice of Internet PKI. Bulletproof TLS and PKI This continuously updated book is the definitive...

 Gracefulsecurity.com
Gracefulsecurity.com
Akimbo Core
Your Vulnerability Management Sucks Published: 16 March 2022 On March 16th I had the pleasure of speaking at the Yorkshire Cyber Security Cluster about Vulnerability Management. I've included my slides from the presentation and some speaker notes on the content covered here. Continue Reading HTTP Security Headers: Cache-Control Published: 21...
Technologies Used by heartbleed.com
Dns Records of heartbleed.com
A Record: 13.227.219.113 13.227.219.70 13.227.219.40 13.227.219.13AAAA Record:
CNAME Record:
NS Record: ns-1757.awsdns-27.co.uk ns-1395.awsdns-46.org ns-112.awsdns-14.com ns-837.awsdns-40.net
SOA Record: awsdns-hostmaster.amazon.com
MX Record:
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of heartbleed.com
Domain Name: HEARTBLEED.COMRegistry Domain ID: 1853534635_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.godaddy.com
Registrar URL: http://www.godaddy.com
Updated Date: 2018-06-20T11:16:04Z
Creation Date: 2014-04-05T20:13:33Z
Registry Expiry Date: 2027-04-05T20:13:33Z
Registrar: GoDaddy.com, LLC
Registrar IANA ID: 146
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: 480-624-2505
Domain Status: clientDeleteProhibited https://icann.org/epp#clientDeleteProhibited
Domain Status: clientRenewProhibited https://icann.org/epp#clientRenewProhibited
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: clientUpdateProhibited https://icann.org/epp#clientUpdateProhibited
Name Server: NS-112.AWSDNS-14.COM
Name Server: NS-1395.AWSDNS-46.ORG
Name Server: NS-1757.AWSDNS-27.CO.UK
Name Server: NS-837.AWSDNS-40.NET
DNSSEC: unsigned
URL of the ICANN Whois Inaccuracy Complaint Form: https://www.icann.org/wicf/
>>> Last update of whois database: 2022-08-27T15:34:44Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
NOTICE: The expiration date displayed in this record is the date the
registrar's sponsorship of the domain name registration in the registry is
currently set to expire. This date does not necessarily reflect the expiration
date of the domain name registrant's agreement with the sponsoring
registrar. Users may consult the sponsoring registrar's Whois database to
view the registrar's reported date of expiration for this registration.
TERMS OF USE: You are not authorized to access or query our Whois
database through the use of electronic processes that are high-volume and
automated except as reasonably necessary to register domain names or
modify existing registrations; the Data in VeriSign Global Registry
Services' ("VeriSign") Whois database is provided by VeriSign for
information purposes only, and to assist persons in obtaining information
about or related to a domain name registration record. VeriSign does not
guarantee its accuracy. By submitting a Whois query, you agree to abide
by the following terms of use: You agree that you may use this Data only
for lawful purposes and that under no circumstances will you use this Data
to: (1) allow, enable, or otherwise support the transmission of mass
unsolicited, commercial advertising or solicitations via e-mail, telephone,
or facsimile; or (2) enable high volume, automated, electronic processes
that apply to VeriSign (or its computer systems). The compilation,
repackaging, dissemination or other use of this Data is expressly
prohibited without the prior written consent of VeriSign. You agree not to
use electronic processes that are automated and high-volume to access or
query the Whois database except as reasonably necessary to register
domain names or modify existing registrations. VeriSign reserves the right
to restrict your access to the Whois database in its sole discretion to ensure
operational stability. VeriSign may restrict or terminate your access to the
Whois database for failure to abide by these terms of use. VeriSign
reserves the right to modify these terms at any time.
The Registry database contains ONLY .COM, .NET, .EDU domains and
Registrars.
 149.56.142.28
149.56.142.28
 Canada
Canada
 InValid
SSL
InValid
SSL