SecRepo - Security Data Samples Repository
Other Digital Corpora - Disk images, network traffic, and malware, oh my! [License Info: This material is based upon work supported by the National Science Foundation under Grant No. 0919593] Verizon VERIS Database - Raw VERIS (filtered) data. [License Info: Creative Commons Attribution-ShareAlike 4.0 International Public License] The Swedish Defence...
Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.616346
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 2772
Links
ratio 52.194431335536
SSL Details
SSL Issuer:
Issuer: R3
Valid From: 2022-05-03 11:48:05
Expiration Date: 2022-08-01 11:48:04
SSL Organization:
Signature 8b1484d3427ef2874245b1bf1caa11a9d05de521
Algorithm: RSA-SHA256
Found 26 Top Alternative to Secrepo.com
 Vizsec.org
Vizsec.org
VizSec
The IEEE Symposium on Visualization for Cyber Security (VizSec) is a forum that brings together researchers and practitioners from academia, government, and industry to address the needs of the cyber security community through new and insightful visualization and analysis techniques.
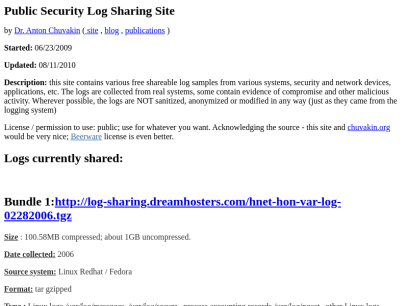
 Log-sharing.dreamhosters.com
Log-sharing.dreamhosters.com
Public Security Log Sharing
Size : 9.9MB compressed; about 100MB uncompressed. Date collected: June - August 2005 Source system: Linux Redhat / Fedora Format: tar bzip2'ed Type : Linux logs /var/log/messages, /var/log/secure , process accounting records /var/log/pacct , other Linux logs, Apache web server logs /var/log/httpd/access_log, /var/log/httpd/error-log, /var/log/httpd/referer-log and /var/log/httpd/audit_log , Sendmail /var/log/mailog, Squid...

 Weebly.com
Weebly.com
Free Website Builder: Build a Free Website or Online Store | Weebly
Weebly’s free website builder makes it easy to create a website, blog, or online store. Find customizable templates, domains, and easy-to-use tools for any type of business website.
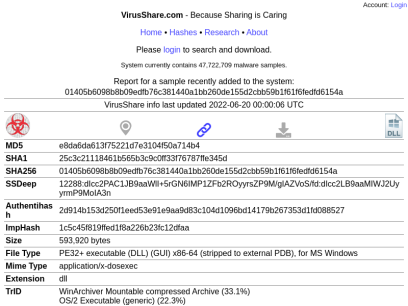
 Virusshare.com
Virusshare.com
VirusShare.com
b9c8e9ab6bea3e0097587638e5a6f8b9cb6966539c9cf97a4ce64303e69aad43 VirusShare info last updated 2022-06-21 00:00:04 UTC MD5 6075f011551403351197d89c931feced SHA1 ee4f4fed26fafc2b30e6d3feaaff97327923c0fa SHA256 b9c8e9ab6bea3e0097587638e5a6f8b9cb6966539c9cf97a4ce64303e69aad43 SSDeep 1536:OhKpb8rGYrMPe3q7Q0XV5xtezE8vG8UM+of+hDcnTLiQrRTZws8E/g:uKpb8rGYrMPe3q7Q0XV5xtezE8vG8UM2 Size 72,192 bytes File Type Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: Dream, Last Saved By: TYHRETH, Name of Creating Application: Microsoft Excel, Create Time/Date:...

 Executemalware.com
Executemalware.com
Error. Page cannot be displayed. Please contact your service provider for more details. (26)
 Datadrivensecurity.info
Datadrivensecurity.info
Data Driven Security
The Book Published in February, 2014 by Wiley Press, Data Driven Security: The Book is your gateway drug into Security Data Science. Learn how to use R and integrate core principles of data analysis into your security work. Learn more about the book! » The Blog Building on the foundations...


 Contagiodump.blogspot.com
Contagiodump.blogspot.com
contagio
Monday, December 14, 2020 2020-12-13 SUNBURST SolarWinds Backdoor samples Reference I am sure you all saw the news. 2020-12-13 Fireeye Highly Evasive Attacker Leverages SolarWinds Supply Chain to Compromise Multiple Global Victims With SUNBURST Backdoor 2020-12-13 Microsoft Customer Guidance on Recent Nation-State Cyber Attacks Well, here are the Sunburst...
 Hksecurity.net
Hksecurity.net
HCRL
Welcome to HCRL Hacking and Countermeasure Research Lab Hacking and Countermeasure Research Lab. (est. in 2010) Hacking and Countermeasure Research Lab (HCR Lab)’s main research area is data-driven security which is based on machine learning and data mining technology to extract and learn useful knowledge from massive data. Especially, HCR...

 Stratosphereips.org
Stratosphereips.org
Stratosphere IPS
Stratosphere Research Laboratory We are the cybersecurity group of the Artificial Intelligence Centre, Faculty of Electrical Engineering at the Czech Technical University in Prague. Our group works at the intersection of cybersecurity, machine learning, and helping others. Learn More Machine Learning, Cybersecurity and Helping Others We used the latest...

 Merit.edu
Merit.edu
Merit – Connecting Organizations, Building Communities
Menu About History Membership Become a Member Member Engagement Testimonials Services News Our Team Careers Internship Program Governance Merit Advisory Council Resources Initiatives Moonshot Education & Resources Policy & Funding Data & Mapping Data Collection Services Testimonials Michigan Moonshot Educational Series Where to Go from Here Michigan Moonshot Community Access...

 Netresec.com
Netresec.com
NETRESEC - Network Forensics and Network Security Monitoring
Network forensics, packet sniffers and IT security products. Download NetworkMiner and other free software for network security analysis.

 Crawdad.org
Crawdad.org
CRAWDAD
New CRAWADAD Data Set - - May 27, 2022 A new data set has been added to CRAWDAD: ucmerced/modes/2022-05-20 Time-series occupancy datafor thermal and vibration sensing systems Contributed by Hamid Rajabi, University of California Merced You can use DOI 10.15783/08kw‑7n74 to cite, https://doi.org/10.15783/08kw‑7n74 New CRAWDAD Data Set - - May...

 Botconf.eu
Botconf.eu
Botconf 2021-2022 | The Botnet Fighting Conference 9th edition
The Botnet Fighting Conference 9th edition

 Hackinginsider.com
Hackinginsider.com
hackinginsider.com is almost here!
The owner of this domain has not yet uploaded their website.
 Msticpy.readthedocs.io
Msticpy.readthedocs.io
MSTIC Jupyter and Python Security Tools — msticpy 2.0.0-pre3 documentation
Getting Started Introduction Use Cases and Environments Installing Python 3.8 or Later Creating a virtual environment Installation Selective Installation - using “extras” Quick Start Overview of MSTICPy Installing Importing MSTICPy Searching for a MSTICPy module Initializing MSTICPy Setup msticpyconfig.yaml Running a data query Visualizing Data Enriching data with Context and...
Technologies Used by secrepo.com
Dns Records of secrepo.com
A Record: 66.33.221.139AAAA Record:
CNAME Record:
NS Record: ns1.dreamhost.com ns2.dreamhost.com ns3.dreamhost.com
SOA Record: hostmaster.dreamhost.com
MX Record:
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of secrepo.com
Domain Name: SECREPO.COMRegistry Domain ID: 1876741429_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.namecheap.com
Registrar URL: http://www.namecheap.com
Updated Date: 2021-08-22T07:33:25Z
Creation Date: 2014-09-21T02:33:18Z
Registry Expiry Date: 2022-09-21T02:33:18Z
Registrar: NameCheap, Inc.
Registrar IANA ID: 1068
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.6613102107
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Name Server: NS1.DREAMHOST.COM
Name Server: NS2.DREAMHOST.COM
DNSSEC: unsigned
URL of the ICANN Whois Inaccuracy Complaint Form: https://www.icann.org/wicf/
>>> Last update of whois database: 2022-06-15T15:17:38Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
NOTICE: The expiration date displayed in this record is the date the
registrar's sponsorship of the domain name registration in the registry is
currently set to expire. This date does not necessarily reflect the expiration
date of the domain name registrant's agreement with the sponsoring
registrar. Users may consult the sponsoring registrar's Whois database to
view the registrar's reported date of expiration for this registration.
TERMS OF USE: You are not authorized to access or query our Whois
database through the use of electronic processes that are high-volume and
automated except as reasonably necessary to register domain names or
modify existing registrations; the Data in VeriSign Global Registry
Services' ("VeriSign") Whois database is provided by VeriSign for
information purposes only, and to assist persons in obtaining information
about or related to a domain name registration record. VeriSign does not
guarantee its accuracy. By submitting a Whois query, you agree to abide
by the following terms of use: You agree that you may use this Data only
for lawful purposes and that under no circumstances will you use this Data
to: (1) allow, enable, or otherwise support the transmission of mass
unsolicited, commercial advertising or solicitations via e-mail, telephone,
or facsimile; or (2) enable high volume, automated, electronic processes
that apply to VeriSign (or its computer systems). The compilation,
repackaging, dissemination or other use of this Data is expressly
prohibited without the prior written consent of VeriSign. You agree not to
use electronic processes that are automated and high-volume to access or
query the Whois database except as reasonably necessary to register
domain names or modify existing registrations. VeriSign reserves the right
to restrict your access to the Whois database in its sole discretion to ensure
operational stability. VeriSign may restrict or terminate your access to the
Whois database for failure to abide by these terms of use. VeriSign
reserves the right to modify these terms at any time.
The Registry database contains ONLY .COM, .NET, .EDU domains and
Registrars.
 185.199.108.153
185.199.108.153
 United States
United States
 Valid SSL
Valid SSL