TekDefense - News
IT Security News, Tips, and Services

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.629937
SSL: Disable
Status: up
Code To Txt Ratio
Word Count 4622
Links
ratio 42.199830172658
Found 73 Top Alternative to Tekdefense.com

 Contagiodump.blogspot.com
Contagiodump.blogspot.com
contagio
Monday, December 14, 2020 2020-12-13 SUNBURST SolarWinds Backdoor samples Reference I am sure you all saw the news. 2020-12-13 Fireeye Highly Evasive Attacker Leverages SolarWinds Supply Chain to Compromise Multiple Global Victims With SUNBURST Backdoor 2020-12-13 Microsoft Customer Guidance on Recent Nation-State Cyber Attacks Well, here are the Sunburst...

 Ikarussecurity.com
Ikarussecurity.com
Willkommen - IKARUS Security Software
IKARUS Security Software entwickelt und betreibt IT- und OT-Sicherheitslösungen von der eigenen Scan Engine über Cloud-Services bis hin zu SOC, SiEM und Log Management-Services.

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.
 Eicar.org
Eicar.org
Eicar – EUROPEAN EXPERT GROUP FOR IT-SECURITY
This page is still work in progress. Sorry for any inconvenience. WELCOME TO EICAR* Established in 1991 as the European Institute for Computer Anti-Virus Research (EICAR) we have a long track record in the fields of science, research, development, implementation and management. We represent different stakeholder groups such as Universities,...
 Wicar.org
Wicar.org
WICAR.org - Test Your Anti-Malware Solution! - Home
How it works When you visit a malicious website, a number of actions may occur: A search result in Google may mark the result with the message "This website may harm your computer" and prevent you from visiting the address. The web browser, such as Internet Explorer, Firefox and Chrome,...
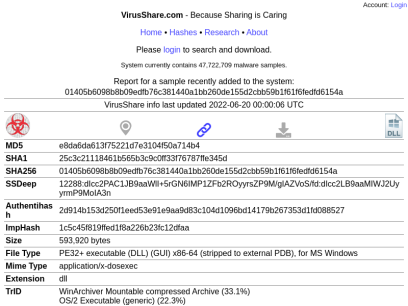
 Virusshare.com
Virusshare.com
VirusShare.com
b9c8e9ab6bea3e0097587638e5a6f8b9cb6966539c9cf97a4ce64303e69aad43 VirusShare info last updated 2022-06-21 00:00:04 UTC MD5 6075f011551403351197d89c931feced SHA1 ee4f4fed26fafc2b30e6d3feaaff97327923c0fa SHA256 b9c8e9ab6bea3e0097587638e5a6f8b9cb6966539c9cf97a4ce64303e69aad43 SSDeep 1536:OhKpb8rGYrMPe3q7Q0XV5xtezE8vG8UM+of+hDcnTLiQrRTZws8E/g:uKpb8rGYrMPe3q7Q0XV5xtezE8vG8UM2 Size 72,192 bytes File Type Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: Dream, Last Saved By: TYHRETH, Name of Creating Application: Microsoft Excel, Create Time/Date:...
 Cuckoosandbox.org
Cuckoosandbox.org
Cuckoo Sandbox - Automated Malware Analysis
What is Cuckoo? Cuckoo Sandbox is the leading open source automated malware analysis system. You can throw any suspicious file at it and in a matter of minutes Cuckoo will provide a detailed report outlining the behavior of the file when executed inside a realistic but isolated environment. Malware is...

 Amtso.org
Amtso.org
AMTSO - Anti-Malware Testing Standards Organization - AMTSO
News Interview with Alexander Vukcevic at NortonLifeLock: “RTTL Gives Tester Organizations Visibility Into Evolving Threats” 2022-06-02 Interview with Scott Jeffreys, AMTSO’s Standards PM: “Never underestimate the passion of dedicated Computer Science and Cybersecurity professionals who are looking to do the right thing” 2022-04-27 Interview with Samir Mody at K7 Computing:...

 Holisticinfosec.blogspot.com
Holisticinfosec.blogspot.com
HolisticInfoSec™
Monday, August 06, 2018 Moving blog to HolisticInfoSec.io toolsmith and HolisticInfoSec have moved. I've decided to consolidate all content on one platform, namely an R markdown blogdown site running with Hugo for static HTML creation. My frustration with Blogger/Blogspot met its limit when a completed draft of toolsmith #134 vanished...
 Automater.com
Automater.com
Automation of sales and shipping digital goods | Automater
Reliable system for instant delivery digital goods purchased on eBay or online store. Instant delivery of codes and files after purchase. Selling automation.

 Edgewave.com
Edgewave.com
What We Do - GoSecure
GoSecure Acquires Covail to Augment Managed Security Services Acquisition enhances Artificial Intelligence and automation of GoSecure Titan® Platform Read Press Release MarketScape U.S. Managed Detection and Response Services 2021 Vendor Assessment GoSecure Named a Major Player Download IDC MarketScape [Recorded Webinar] Answers to Your Top 5 MDR Questions Watch Now...

 Zeltser.com
Zeltser.com
Lenny Zeltser | Information Security in Business
Advances information security. Grows tech businesses. Fights malware.

 Chousensha.github.io
Chousensha.github.io
Core dump overflow
Notes, tutorials and walkthroughs from my path of information security enlightenment
Technologies Used by tekdefense.com
Dns Records of tekdefense.com
A Record: 65.39.205.54AAAA Record:
CNAME Record:
NS Record: ns68.domaincontrol.com ns67.domaincontrol.com
SOA Record: dns.jomax.net
MX Record: alt2.aspmx.l.google.com alt1.aspmx.l.google.com aspmx3.googlemail.com aspmx2.googlemail.com aspmx.l.google.com
SRV Record:
TXT Record: google-site-verification=OGrYJlbdViwn21rECVynRwXqZE3VYUNNS5EEvG6nru0 google-site-verification=GgwW6xGL658scKdEhqb_jqUyNXSb9X1LIotjCXHLKfs
DNSKEY Record:
CAA Record:
Whois Detail of tekdefense.com
Domain Name: TEKDEFENSE.COMRegistry Domain ID: 1641479463_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.godaddy.com
Registrar URL: https://www.godaddy.com
Updated Date: 2022-02-22T13:25:32Z
Creation Date: 2011-02-21T22:48:36Z
Registrar Registration Expiration Date: 2023-02-21T22:48:36Z
Registrar: GoDaddy.com, LLC
Registrar IANA ID: 146
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.4806242505
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: clientUpdateProhibited https://icann.org/epp#clientUpdateProhibited
Domain Status: clientRenewProhibited https://icann.org/epp#clientRenewProhibited
Domain Status: clientDeleteProhibited https://icann.org/epp#clientDeleteProhibited
Registry Registrant ID: Not Available From Registry
Registrant Name: Registration Private
Registrant Organization: Domains By Proxy, LLC
Registrant Street: DomainsByProxy.com
Registrant Street: 2155 E Warner Rd
Registrant City: Tempe
Registrant State/Province: Arizona
Registrant Postal Code: 85284
Registrant Country: US
Registrant Phone: +1.4806242599
Registrant Phone Ext:
Registrant Fax: +1.4806242598
Registrant Fax Ext:
Registrant Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=TEKDEFENSE.COM
Registry Admin ID: Not Available From Registry
Admin Name: Registration Private
Admin Organization: Domains By Proxy, LLC
Admin Street: DomainsByProxy.com
Admin Street: 2155 E Warner Rd
Admin City: Tempe
Admin State/Province: Arizona
Admin Postal Code: 85284
Admin Country: US
Admin Phone: +1.4806242599
Admin Phone Ext:
Admin Fax: +1.4806242598
Admin Fax Ext:
Admin Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=TEKDEFENSE.COM
Registry Tech ID: Not Available From Registry
Tech Name: Registration Private
Tech Organization: Domains By Proxy, LLC
Tech Street: DomainsByProxy.com
Tech Street: 2155 E Warner Rd
Tech City: Tempe
Tech State/Province: Arizona
Tech Postal Code: 85284
Tech Country: US
Tech Phone: +1.4806242599
Tech Phone Ext:
Tech Fax: +1.4806242598
Tech Fax Ext:
Tech Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=TEKDEFENSE.COM
Name Server: NS67.DOMAINCONTROL.COM
Name Server: NS68.DOMAINCONTROL.COM
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-08-10T09:12:37Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
TERMS OF USE: The data contained in this registrar's Whois database, while believed by the
registrar to be reliable, is provided "as is" with no guarantee or warranties regarding its
accuracy. This information is provided for the sole purpose of assisting you in obtaining
information about domain name registration records. Any use of this data for any other purpose
is expressly forbidden without the prior written permission of this registrar. By submitting
an inquiry, you agree to these terms and limitations of warranty. In particular, you agree not
to use this data to allow, enable, or otherwise support the dissemination or collection of this
data, in part or in its entirety, for any purpose, such as transmission by e-mail, telephone,
postal mail, facsimile or other means of mass unsolicited, commercial advertising or solicitations
of any kind, including spam. You further agree not to use this data to enable high volume, automated
or robotic electronic processes designed to collect or compile this data for any purpose, including
mining this data for your own personal or commercial purposes. Failure to comply with these terms
may result in termination of access to the Whois database. These terms may be subject to modification
at any time without notice.
 142.250.186.161
142.250.186.161
 United States
United States
 Valid SSL
Valid SSL