Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.
Stats
Alexa Rank: 22786
Popular in Country: United States
Country Alexa Rank: 14170
language: en
Response Time: 0.204952
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 2066
Links
ratio 23.351501549642
SSL Details
SSL Issuer:
Issuer: Amazon
Valid From: 2022-03-10 00:00:00
Expiration Date: 2023-04-08 23:59:59
SSL Organization:
Signature 24ee168589666ae092dbaeab239da7f03ab7978a
Algorithm: RSA-SHA256
Found 76 Top Alternative to Tenable.com
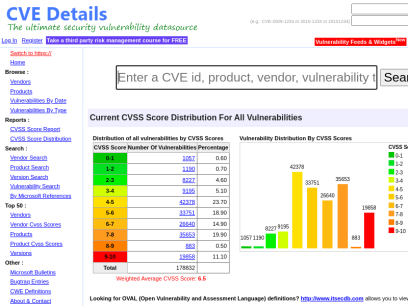
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.


 Qualys.com
Qualys.com
Information Security and Compliance | Qualys
Qualys, Inc. helps your business automate the full spectrum of auditing, compliance and protection of your IT systems and web applications.

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.

 Sans.org
Sans.org
Cyber Security Training | SANS Courses, Certifications & Research
SANS Institute is the most trusted resource for cybersecurity training, certifications and research. Offering more than 60 courses across all practice areas, SANS trains over 40,000 cybersecurity professionals annually.

 Cisecurity.org
Cisecurity.org
CIS Center for Internet Security
CIS is a forward-thinking nonprofit that harnesses the power of a global IT community to safeguard public and private organizations against cyber threats.

 Threatpost.com
Threatpost.com
Threatpost | The first stop for security news
Threatpost, is an independent news site which is a leading source of information about IT and business security for hundreds of thousands of professionals worldwide.

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.

 Netsparker.com
Netsparker.com
Invicti | Web Application Security For Enterprise
Get accurate, automated application security testing that scales like no other solution. Secure 1000s of web assets with less manual effort. Reduce your risk with the only…
 Hackertarget.com
Hackertarget.com
28 Online Vulnerability Scanners & Network Tools | HackerTarget.com
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.
 Darkreading.com
Darkreading.com
Dark Reading | Security | Protect The Business
Cyber security's comprehensive news site is now an online community for security professionals, outlining cyber threats and the technologies for defending against them.

 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!

 Splunk.com
Splunk.com
Splunk | The Data Platform for the Hybrid World
Splunk is the data platform that powers enterprise observability, unified security and limitless custom applications in hybrid environments.
 Cybrary.it
Cybrary.it
Free Cybersecurity Training and Career Development | Cybrary
Cybersecurity training from Cybrary will take your career to the next level. We have the cybersecurity courses that can help get you there!

 Seclists.org
Seclists.org
SecLists.Org Security Mailing List Archive
Security mailing list archive for the Nmap lists, Bugtraq, Full Disclosure, Security Basics, Pen-test, and dozens more. Search capabilities and RSS feeds with smart excerpts are available
 Fortinet.com
Fortinet.com
Global Leader of Cyber Security Solutions and Services | Fortinet
Fortinet delivers award-winning cyber security solutions across the entire digital attack surface, securing devices, data, and applications from the data center to the cloud to the home office.

 Paloaltonetworks.com
Paloaltonetworks.com
Global Cybersecurity Leader - Palo Alto Networks
Palo Alto Networks enables your team to prevent successful cyberattacks with an automated approach that delivers consistent security across cloud, network and mobile.

 Us-cert.gov
Us-cert.gov
Homepage | CISA
As part of its mission, CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.
 Nist.gov
Nist.gov
National Institute of Standards and Technology | NIST
NIST promotes U.S. innovation and industrial competitiveness by advancing measurement science, standards, and technology in ways that enhance economic security and improve our quality of life.
 Solarwinds.com
Solarwinds.com
IT Management Software and Observability Platform | SolarWinds
Get simple, powerful, and secure IT management software to help your organization accelerate in today’s hybrid IT environments. Start a free trial today.

 Manageengine.com
Manageengine.com
ManageEngine - IT Operations and Service Management Software
ManageEngine offers enterprise IT management software for your service management, operations management, Active Directory and security needs. Download free trial now.

 Cyberark.com
Cyberark.com
Identity Security and Access Management Leader | CyberArk
Get the most complete Identity Security and Access Management Solutions that enable secure access across any device, anywhere, at just the right time.

 Blackhat.com
Blackhat.com
Black Hat | Home
Black Hat Webinars Security Research in Real Time June 30, 2022 - Managing Cybersecurity as a Business Risk July 14, 2022 - InfoSec Lessons from the War in Ukraine Sponsor a Webinars View all of our recent Webinars Black Hat Archives Watch Past Presentations View all of our archived videos...

 Beyondtrust.com
Beyondtrust.com
Privileged Access Management, Cyber Security, and Remote Access (formerly Bomgar) | BeyondTrust
Unwanted remote access, stolen credentials, and misused privileges threaten every organization. BeyondTrust offers the industry’s broadest set of privileged access management capabilities to defend against cyber attacks. Our Privileged Access Management platform provides visibility and control over all privileged accounts, users, and access. Trusted by more than 20,000 companies and counting.

 Vulnhub.com
Vulnhub.com
Vulnerable By Design ~ VulnHub
VulnHub provides materials allowing anyone to gain practical hands-on experience with digital security, computer applications and network administration tasks.

 Cyberaces.org
Cyberaces.org
Cyber Aces | SANS Institute
SANS Cyber Aces Online is an online course that teaches the core concepts needed to assess, and protect information security systems.


 Crowdstrike.com
Crowdstrike.com
CrowdStrike: Stop breaches. Drive business.
CrowdStrike is a global cybersecurity leader with an advanced cloud-native platform for protecting endpoints, cloud workloads, identities and data.
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.

 Kali.org
Kali.org
Kali Linux | Penetration Testing and Ethical Hacking Linux Distribution
Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking and network security assessments.

 Tryhackme.com
Tryhackme.com
TryHackMe | Cyber Security Training
TryHackMe is a free online platform for learning cyber security, using hands-on exercises and labs, all through your browser!

 Duo.com
Duo.com
Two-Factor Authentication & Data Protection | Duo Security
Protect your workforce and user data from cybersecurity risks with Duo’s Multifactor Authentication app (Mfa), 2fa, remote access, and zero-trust solutions. Demo today.

 F5.com
F5.com
F5 | Multi-Cloud Security and Application Delivery
F5 application services ensure that applications are always secure and perform the way they should—in any environment and on any device.

 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.
 Microfocus.com
Microfocus.com
Digital Transformation and Enterprise Software Modernization | Micro Focus
Run & Transform with Micro Focus. Accelerate application delivery, simplify IT transformation, strengthen cyber resilience, and analyze in time to act.
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.
 Csoonline.com
Csoonline.com
CSO - CSO Online – IT-Security-News für Profis
News und Insights zur Cybersicherheit im Unternehmen. Alles was CSOs wissen müssen.
 Isaca.org
Isaca.org
Advancing IT, Audit, Governance, Risk, Privacy & Cybersecurity | ISACA
ISACA is a global association that provides IT professionals with knowledge, credentials, training and community in audit, governance, risk, privacy and cybersecurity.
 Eccouncil.org
Eccouncil.org
Certified Ethical Hacker | InfoSec Cyber Security Certification | EC-Council
EC-Council is a global leader in InfoSec Cyber Security certification programs like Certified Ethical Hacker and Computer Hacking Forensic Investigator.

 Veracode.com
Veracode.com
Confidently secure apps you build and manage with Veracode
This simple and scalable solution enables you to create more secure software so that you can boost your business and reduce risk without hindering innovation.

 Vulmon.com
Vulmon.com
Vulmon - Vulnerability Intelligence Search Engine
Vulmon is a vulnerability and exploit search engine with vulnerability intelligence features.

 Securityonline.info
Securityonline.info
Penetration Testing • Information Security
Securityonline is a huge security community. It is committed to the sharing of high-quality technical articles and safety reports, focusing on high-quality security and security incidents in the industry.
 Ctftime.org
Ctftime.org
CTFtime.org / All about CTF (Capture The Flag)
Capture The Flag, CTF teams, CTF ratings, CTF archive, CTF writeups

 Jamf.com
Jamf.com
Jamf Apple Device Management | Mac iPad iPhone TV Apple MDM
We help organizations succeed with Apple providing ability to manage Apple devices, connect users to resources and protect your business from cyber threats.

 Fortiguard.com
Fortiguard.com
FortiGuard
View by Product Network Intrusion Protection Anti-Recon and Anti-Exploit Secure DNS IP Reputation/Anti-Botnet Indicators of Compromise IP Geolocation Service Cloud Workload Security Service Content and Endpoint Endpoint Detection & Response Anti-Virus Endpoint Vulnerability Device Detection ANN and NDR Sandbox Behavior Engine Application Web Filtering Anti-Spam Application Control Industrial Security Services...

 Proofpoint.com
Proofpoint.com
Enterprise Cybersecurity Solutions, Services & Training | Proofpoint US
Find out how Proofpoint helps protect people, data and brands against the latest cyber attacks. Offering cybersecurity and compliance solutions for email, web, cloud, and social media.

 Watchguard.com
Watchguard.com
WatchGuard Technologies | Network Security, Secure Wi-Fi, MFA, and Endpoint Security Solutions
Award-winning solutions that are easy to deploy and manage, making enterprise-grade security accessible to any organization regardless of size or expertise.
 Broadcom.com
Broadcom.com
Broadcom Inc. | Connecting Everything
Broadcom Inc. is a global technology leader that designs, develops and supplies semiconductor and infrastructure software solutions.

 Isc2.org
Isc2.org
Cybersecurity and IT Security Certifications and Training | (ISC)²
Prove you’re a leader in your field with our globally recognized cybersecurity certifications. Help make the cyber world a safer place for all.

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.
 Crackstation.net
Crackstation.net
CrackStation - Online Password Hash Cracking - MD5, SHA1, Linux, Rainbow Tables, etc.
Crackstation is the most effective hash cracking service. We crack: MD5, SHA1, SHA2, WPA, and much more...
 Cleverbridge.com
Cleverbridge.com
cleverbridge - Your eCommerce & Renewal Automation Partner
eCommerce solution; B2B and B2C software and SaaS organizations achieve global growth with increased customer retention, improving improved lifetime value.
 Windows-commandline.com
Windows-commandline.com
Windows Command Line — Windows Commands, Batch files, Command prompt and PowerShell
Learn about Windows CMD Commands, command prompt, Run command, Batch scripts, Dos and PowerShell commands, configuring user accounts, services, network and file system from command prompt

 Varonis.com
Varonis.com
Varonis: We Protect Data
Varonis is a pioneer in data security and analytics, fighting a different battle than conventional cybersecurity companies.

 Darknet.org.uk
Darknet.org.uk
Darknet - Hacking Tools, Hacker News & Cyber Security
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.

 Censys.io
Censys.io
Censys | Industry-Leading Cloud and Internet Asset Discovery Solutions
Attack Surface Management and Data Solutions to help your organization discover potential threats, understand cloud-based assets, and help you move fearlessly forward.
 Alienvault.com
Alienvault.com
AlienVault is now AT&T Cybersecurity
At AT&T Cybersecurity our mission is to provide phenomenal threat intelligence, collaborative defense & effective security for organizations of all sizes.

 Alertlogic.com
Alertlogic.com
Managed Detection and Response (MDR) Company | Alert Logic
Alert Logic’s Managed Detection and Response platform provides 24/7 protection against constantly evolving cyber attacks. Protect your company now!
Technologies Used by tenable.com
Dns Records of tenable.com
A Record: 54.159.189.155AAAA Record:
CNAME Record:
NS Record: ns2.tenablesecurity.com ns3.tenablesecurity.com ns1.tenablesecurity.com
SOA Record: hostmaster.tenable.com
MX Record: us-smtp-inbound-2.mimecast.com us-smtp-inbound-1.mimecast.com
SRV Record:
TXT Record: adobe-idp-site-verification=dd57aac6628a70f8726e76946e94476a706a89bb5b527d7748641745d7680b08 docusign=01896691-46f6-42a7-89da-42203b74c164 vmware-cloud-verification-106effbe-74cc-4aaa-a87b-418fa8a1311a google-site-verification=r0TQaECa04je1WAQC5Vr8J6haS_diT7XfJAP7b11JGc apple-domain-verification=clcd7AntcH2Z4VX1 google-site-verification=NQ51A02Hvzw45aMVkt8I_WWalY74CryagW8FxtkgMU4 docker-verification=70eeb94b-709c-4f1e-b42b-22d8e1fbdeff 2295029 h1-domain-verification=gkC8dff3yPgSuCZRjPs4XJZGowM4HNsc2vGJLqGwuSWkzUKF v=spf1 redirect=1mz2szrz._spf._d.mim.ec loaderio=304cb40b43c10147ec18df636e5b1f14 docusign=039a7a49-7176-4b7b-bb58-d198685b7f4a atlassian-domain-verification=tfLnjYErcFyBHEAn5HHFsyHmRHOk8jKA8MsvuU5tmk4ksTNEFXoTF89d4jxWhYYN MS=ms17590469 postman-domain-verification=50380d45de6d54a2d098961909fc132a12c58d50e260586e8ba33438a6a8b286513a3d77ed0adae11d59bca4f2e9f60eb2f31f7f9756b3f51841f7354ebe8d30
DNSKEY Record:
CAA Record: digicert.com amazon.com amazon.com digicert.com letsencrypt.org
Whois Detail of tenable.com
Domain Name: tenable.comRegistry Domain ID: 207976_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.registrar.amazon.com
Registrar URL: https://registrar.amazon.com
Updated Date: 2021-07-21T15:11:48.502Z
Creation Date: 1997-04-10T04:00:00Z
Registrar Registration Expiration Date: 2028-04-11T04:00:00Z
Registrar: Amazon Registrar, Inc.
Registrar IANA ID: 468
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.2067406200
Reseller:
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: transferPeriod https://icann.org/epp#transferPeriod
Domain Status: ok https://icann.org/epp#ok
Registry Registrant ID:
Registrant Name: On behalf of tenable.com owner
Registrant Organization: Whois Privacy Service
Registrant Street: P.O. Box 81226
Registrant City: Seattle
Registrant State/Province: WA
Registrant Postal Code: 98108-1226
Registrant Country: US
Registrant Phone: +1.2065771368
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: On behalf of tenable.com administrative contact
Admin Organization: Whois Privacy Service
Admin Street: P.O. Box 81226
Admin City: Seattle
Admin State/Province: WA
Admin Postal Code: 98108-1226
Admin Country: US
Admin Phone: +1.2065771368
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID:
Tech Name: On behalf of tenable.com technical contact
Tech Organization: Whois Privacy Service
Tech Street: P.O. Box 81226
Tech City: Seattle
Tech State/Province: WA
Tech Postal Code: 98108-1226
Tech Country: US
Tech Phone: +1.2065771368
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email: [email protected]
Name Server: ns1.tenablesecurity.com
Name Server: ns2.tenablesecurity.com
Name Server: ns3.tenablesecurity.com
DNSSEC: signedDelegation
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2021-07-21T15:11:48.678Z <<<
For more information on Whois status codes, please visit https://www.icann.org/resources/pages/epp
By submitting a query to the Amazon Registrar, Inc. WHOIS database, you agree to abide by the following terms. The data in Amazon Registrar, Inc.'s WHOIS database is provided by Amazon Registrar, Inc. for the sole purpose of assisting you in obtaining information about domain name accuracy. You agree to use this data only for lawful purposes and further agree not to use this data for any unlawful purpose or to: (1) enable, allow, or otherwise support the transmission by email, telephone, or facsimile of commercial advertising or unsolicited bulk email, or (2) enable high volume, automated, electronic processes to collect or compile this data for any purpose, including mining this data for your own personal or commercial purposes. Amazon Registrar, Inc. reserves the right to restrict or terminate your access to the data if you fail to abide by these terms of use. Amazon Registrar, Inc. reserves the right to modify these terms at any time.
Visit Amazon Registrar, Inc. at https://registrar.amazon.com
Contact information available here: https://docs.aws.amazon.com/Route53/latest/DeveloperGuide/domain-contact-support.html
© 2022, Amazon.com, Inc., or its affiliates
 104.18.23.245
104.18.23.245
 United States
United States
 Valid SSL
Valid SSL