Profile
Skills Cloud Security Architecture and Engineering Technology and Application Security Architecture Secure DevOps (DevSecOps) Containers (Docker) and Microservices Automation of Security Controls / Analysis Agile, Git, CI/CD Pipelines and IaC Serverless Development and Architecture Threat Modelling and Risk Management Development: C++/QT5, NodeJS, AWS Lambda Security Assessments, Malware Analysis...

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.68944
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 258
Links
ratio 36.108676599474
SSL Details
SSL Issuer:
Issuer: Sectigo RSA Domain Validation Secure Server CA
Valid From: 2022-01-07 00:00:00
Expiration Date: 2023-02-07 23:59:59
SSL Organization:
Signature 93e2fd26166ff8bdf8ef7920b050fc1ac8c91894
Algorithm: RSA-SHA256
Found 39 Top Alternative to Amanhardikar.com

 Dvwa.co.uk
Dvwa.co.uk
DVWA - Damn Vulnerable Web Application
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is damn vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, help web developers better understand the processes of securing web applications and aid teachers/students to teach/learn web application security in a class room environment.

 Pentesterlab.com
Pentesterlab.com
PentesterLab: Learn Web Penetration Testing: The Right Way
WHAT OUR PRO MEMBERS SAY: 10010101 10110110 1010 “I consider PentesterLab to be a great resource for learning about web application security and ways how it can be subverted. Even though the exercises usually don’t take much time to complete they can teach a lot. I can’t but recommend it,...

 Itsecgames.com
Itsecgames.com
bWAPP, a buggy web application!
Home bWAPP, or a buggy web application, is a free and open source deliberately insecure web application. It helps security enthusiasts, developers and students to discover and to prevent web vulnerabilities. bWAPP prepares one to conduct successful penetration testing and ethical hacking projects. What makes bWAPP so unique? Well, it...

 Vulnhub.com
Vulnhub.com
Vulnerable By Design ~ VulnHub
VulnHub provides materials allowing anyone to gain practical hands-on experience with digital security, computer applications and network administration tasks.
 Appspot.com
Appspot.com
Google Cloud Platform
Email or phone Forgot email? Not your computer? Use a private browsing window to sign in. Learn more Next Create account
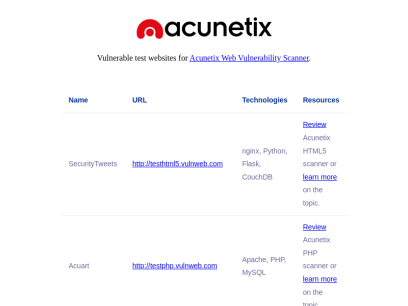
 Vulnweb.com
Vulnweb.com
Acunetix Web Vulnerability Scanner - Test websites
SecurityTweets http://testhtml5.vulnweb.com nginx, Python, Flask, CouchDB Review Acunetix HTML5 scanner or learn more on the topic. Acuart http://testphp.vulnweb.com Apache, PHP, MySQL Review Acunetix PHP scanner or learn more on the topic. Acuforum http://testasp.vulnweb.com IIS, ASP, Microsoft SQL Server Review Acunetix SQL scanner or learn more on the topic. Acublog http://testaspnet.vulnweb.com...

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.

 W4rri0r.com
W4rri0r.com
w4rri0r - Hacking Is Not A Crime - It's an art of Awareness
Cloud Security Mobile Security Wireless Security Network Security Tab 1 Cloud Security Cloud Security is the set of security protocols, methodologies and technologies that protect the availability of cloud resources and the integrity of data stored in a cloud computing environment. Cloud security differs from traditional computer security in that...
 Offensivesec.blogspot.com
Offensivesec.blogspot.com
Offensive Sec Blog
Wednesday, February 9, 2022 ECDX - Exploit Development Student OffensiveSec 4:28:00 PM Elearn Security No comments ECDX - Exploit Development Student from the popular eLearnSecurity Institute and INE is an Exploit Development training at the beginner level. Prerequisites for this course Completion of the eJPT courseIs. The eCXD...

 Dst.com.ng
Dst.com.ng
DST - Development Standards Technologies
DST is registered in Nigeria and we produce and market software products, develop and host websites, and provide a wide range of consulting services.
Technologies Used by amanhardikar.com
Dns Records of amanhardikar.com
A Record: 199.188.206.58AAAA Record:
CNAME Record:
NS Record: dns1.namecheaphosting.com dns2.namecheaphosting.com
SOA Record: cpanel.tech.namecheap.com
MX Record: mx1-hosting.jellyfish.systems mx2-hosting.jellyfish.systems mx3-hosting.jellyfish.systems
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of amanhardikar.com
Domain Name: amanhardikar.comRegistry Domain ID: 1653300911_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.registrar.amazon.com
Registrar URL: https://registrar.amazon.com
Updated Date: 2022-03-24T22:22:54.954Z
Creation Date: 2011-04-28T08:55:24Z
Registrar Registration Expiration Date: 2023-04-28T08:55:24Z
Registrar: Amazon Registrar, Inc.
Registrar IANA ID: 468
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.2067406200
Reseller:
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: renewPeriod https://icann.org/epp#renewPeriod
Registry Registrant ID:
Registrant Name: On behalf of amanhardikar.com owner
Registrant Organization: Whois Privacy Service
Registrant Street: P.O. Box 81226
Registrant City: Seattle
Registrant State/Province: WA
Registrant Postal Code: 98108-1226
Registrant Country: US
Registrant Phone: +1.2065771368
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: On behalf of amanhardikar.com administrative contact
Admin Organization: Whois Privacy Service
Admin Street: P.O. Box 81226
Admin City: Seattle
Admin State/Province: WA
Admin Postal Code: 98108-1226
Admin Country: US
Admin Phone: +1.2065771368
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID:
Tech Name: On behalf of amanhardikar.com technical contact
Tech Organization: Whois Privacy Service
Tech Street: P.O. Box 81226
Tech City: Seattle
Tech State/Province: WA
Tech Postal Code: 98108-1226
Tech Country: US
Tech Phone: +1.2065771368
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email: [email protected]
Name Server: dns1.namecheaphosting.com
Name Server: dns2.namecheaphosting.com
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-03-24T22:22:55.714Z <<<
For more information on Whois status codes, please visit https://www.icann.org/resources/pages/epp
By submitting a query to the Amazon Registrar, Inc. WHOIS database, you agree to abide by the following terms. The data in Amazon Registrar, Inc.'s WHOIS database is provided by Amazon Registrar, Inc. for the sole purpose of assisting you in obtaining information about domain name accuracy. You agree to use this data only for lawful purposes and further agree not to use this data for any unlawful purpose or to: (1) enable, allow, or otherwise support the transmission by email, telephone, or facsimile of commercial advertising or unsolicited bulk email, or (2) enable high volume, automated, electronic processes to collect or compile this data for any purpose, including mining this data for your own personal or commercial purposes. Amazon Registrar, Inc. reserves the right to restrict or terminate your access to the data if you fail to abide by these terms of use. Amazon Registrar, Inc. reserves the right to modify these terms at any time.
Visit Amazon Registrar, Inc. at https://registrar.amazon.com
Contact information available here: https://docs.aws.amazon.com/Route53/latest/DeveloperGuide/domain-contact-support.html
© 2022, Amazon.com, Inc., or its affiliates
 185.199.108.153
185.199.108.153
 United States
United States
 Valid SSL
Valid SSL