PentesterLab: Learn Web Penetration Testing: The Right Way
WHAT OUR PRO MEMBERS SAY: 10010101 10110110 1010 “I consider PentesterLab to be a great resource for learning about web application security and ways how it can be subverted. Even though the exercises usually don’t take much time to complete they can teach a lot. I can’t but recommend it,...

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time: 0.636926
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 664
Links
ratio 36.769921967368
SSL Details
SSL Issuer:
Issuer: Gandi Standard SSL CA 2
Valid From: 2022-01-03 00:00:00
Expiration Date: 2023-02-03 23:59:59
SSL Organization:
Signature 868c4fd401ca11efefca4628a997176a8126955e
Algorithm: RSA-SHA256
Found 71 Top Alternative to Pentesterlab.com


 Hacker101.com
Hacker101.com
Home | Hacker101
Hacker101 is a free class for web security. Whether you’re a programmer with an interest in bug bounties or a seasoned security professional, Hacker101 has something to teach you.


 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!

 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.
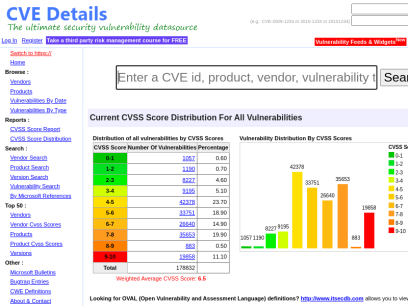
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Elearnsecurity.com
Elearnsecurity.com
Cyber Security Certifications - eLearnSecurity - eLearnSecurity
Trusted by HR departments around the world, our certifications are scenario-based exams that prove your cyber security skills in the job market. Infosec careers are heating up and candidates are doing everything they can to stand out. Passing an eLearnSecurity certification shows potential employers that you have proven red, blue and purple team capabilities.

 Vulnhub.com
Vulnhub.com
Vulnerable By Design ~ VulnHub
VulnHub provides materials allowing anyone to gain practical hands-on experience with digital security, computer applications and network administration tasks.

 Pentestbox.org
Pentestbox.org
Pentest Box
PentestBox is an Opensource PreConfigured Portable Penetration Testing Environment for the Windows Operating System.

 F4l13n5n0w.github.io
F4l13n5n0w.github.io
Info Security & Pen Testing learning notes | F4l13n5n0w
This is a description

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.

 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Amanhardikar.com
Amanhardikar.com
Profile
Skills Cloud Security Architecture and Engineering Technology and Application Security Architecture Secure DevOps (DevSecOps) Containers (Docker) and Microservices Automation of Security Controls / Analysis Agile, Git, CI/CD Pipelines and IaC Serverless Development and Architecture Threat Modelling and Risk Management Development: C++/QT5, NodeJS, AWS Lambda Security Assessments, Malware Analysis...

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.
 Cybrary.it
Cybrary.it
Free Cybersecurity Training and Career Development | Cybrary
Cybersecurity training from Cybrary will take your career to the next level. We have the cybersecurity courses that can help get you there!

 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies

 Cobalt.io
Cobalt.io
Pentest as a Service | Cobalt
Cobalt is modernizing traditional pentesting. We leverage global talent and a SaaS platform to deliver a better pentest via Pentest as a Service (PtaaS).
 Securityidiots.com
Securityidiots.com
Welcome to Security Idiots!!
Security Idiots is a place where some insane idiots try thier hands on with Security.

 Pentestgeek.com
Pentestgeek.com
Learn Web Application Penetration Testing - Pentest Geek
HACK LIKE A PRO. SECURE LIKE A BOSS. Are you an Ethical Hacker? Do you want to be one? This course will teach you everything you need to know to get started now! I'M READY TO LEARN Hackers and Penetration Testers have one thing in common. They know how to...

 Pentester.land
Pentester.land
Pentester Land · Offensive Infosec
The newsletter is dead, long live the newsletter! 12 Jul 2020 • newsletter This is a long due post. Since The 5 Hacking Newsletter has stopped on this blog, I’ve been getting many questions about it. So, even though most readers already know by now, here’s a summary of what...
 Outpost24.com
Outpost24.com
Cyber Security Risk Management Solutions | Outpost 24
Outpost24's intelligent cyber risk management solution provide continuous visibility on the vulnerabilities and cyber threats affecting your organization to accelerate remediation - before attackers exploit them

 Pentestmonkey.net
Pentestmonkey.net
pentestmonkey | Taking the monkey work out of pentesting
mimikatz: Tool To Recover Cleartext Passwords From Lsass December 20, 2011, pentestmonkey I meant to blog about this a while ago, but never got round to it. Here’s a brief post about very cool feature of a tool called mimikatz. I’m very grateful to the tool’s author for bringing it...

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.

 Redteamsecure.com
Redteamsecure.com
Offensive Security by RedTeam Security
RedTeam Security uncovers and identifies offensive security risks. We find malicious attacks before they find you. Call our security experts 952-836-2770

 Rhinosecuritylabs.com
Rhinosecuritylabs.com
Penetration Testing Company, Network & Web Application Pen Test
Rhino Security Labs is a top penetration testing company specializing in cloud (AWS, GCP, Azure), network pentesting, and webapp pentesting in Seattle.

 Appsecco.com
Appsecco.com
Appsecco - Secure Your Apps and Cloud | appsecco.com
No-Nonsense Cloud and Application Penetration Testing. Protect your business with expert security testing and actionable recommendations. Start today!

 Bulletproof.co.uk
Bulletproof.co.uk
Your Best Defence Against Cyber Threats – Bulletproof.co.uk
Our cyber security & compliance services help you stay ahead of the hackers, take control of your infrastructure and protect your business-critical data.

 Enciphers.com
Enciphers.com
Penetration Testing | Vulnerability Assessment | Security Training
Advance Penetration Testing, Vulnerability Assessment, Security Training
 Alpinesecurity.com
Alpinesecurity.com
We Help You Stop Cyberattacks with Cybersecurity Consulting & Training
Medical device and heathcare cybersecurity assessment and testing, penetration testing, cybersecurity certification training, CISO as a Service (CaaS).

 Intigriti.com
Intigriti.com
Intigriti - Bug Bounty & Agile Pentesting Platform
Intigriti offers bug bounty and agile penetration testing solutions powered by Europe's #1 leading network of ethical hackers.

 Sqlinjection.net
Sqlinjection.net
SQL Injection - Understand and Prevent SQL Injection Attacks
A complete reference about SQL injection. Introduction, tutorial, advanced attack techniques, how to avoid it, resources and much more!

 Gracefulsecurity.com
Gracefulsecurity.com
Akimbo Core
Your Vulnerability Management Sucks Published: 16 March 2022 On March 16th I had the pleasure of speaking at the Yorkshire Cyber Security Cluster about Vulnerability Management. I've included my slides from the presentation and some speaker notes on the content covered here. Continue Reading HTTP Security Headers: Cache-Control Published: 21...
Technologies Used by pentesterlab.com
Dns Records of pentesterlab.com
A Record: 54.87.134.91AAAA Record:
CNAME Record:
NS Record: ns-206-c.gandi.net ns-27-a.gandi.net ns-195-b.gandi.net
SOA Record: hostmaster.gandi.net
MX Record: aspmx4.googlemail.com aspmx2.googlemail.com aspmx3.googlemail.com alt1.aspmx.l.google.com aspmx5.googlemail.com alt2.aspmx.l.google.com aspmx.l.google.com
SRV Record:
TXT Record: v=spf1 include:_spf.google.com include:amazonses.com ~all
DNSKEY Record:
CAA Record:
Whois Detail of pentesterlab.com
Domain Name: PENTESTERLAB.COMRegistry Domain ID: 1671658410_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.gandi.net
Registrar URL: http://www.gandi.net
Updated Date: 2022-05-25T09:01:16Z
Creation Date: 2011-08-12T07:45:49Z
Registry Expiry Date: 2023-08-12T07:45:49Z
Registrar: Gandi SAS
Registrar IANA ID: 81
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +33.170377661
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Name Server: NS-195-B.GANDI.NET
Name Server: NS-206-C.GANDI.NET
Name Server: NS-27-A.GANDI.NET
DNSSEC: unsigned
URL of the ICANN Whois Inaccuracy Complaint Form: https://www.icann.org/wicf/
>>> Last update of whois database: 2022-07-03T13:19:42Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
NOTICE: The expiration date displayed in this record is the date the
registrar's sponsorship of the domain name registration in the registry is
currently set to expire. This date does not necessarily reflect the expiration
date of the domain name registrant's agreement with the sponsoring
registrar. Users may consult the sponsoring registrar's Whois database to
view the registrar's reported date of expiration for this registration.
TERMS OF USE: You are not authorized to access or query our Whois
database through the use of electronic processes that are high-volume and
automated except as reasonably necessary to register domain names or
modify existing registrations; the Data in VeriSign Global Registry
Services' ("VeriSign") Whois database is provided by VeriSign for
information purposes only, and to assist persons in obtaining information
about or related to a domain name registration record. VeriSign does not
guarantee its accuracy. By submitting a Whois query, you agree to abide
by the following terms of use: You agree that you may use this Data only
for lawful purposes and that under no circumstances will you use this Data
to: (1) allow, enable, or otherwise support the transmission of mass
unsolicited, commercial advertising or solicitations via e-mail, telephone,
or facsimile; or (2) enable high volume, automated, electronic processes
that apply to VeriSign (or its computer systems). The compilation,
repackaging, dissemination or other use of this Data is expressly
prohibited without the prior written consent of VeriSign. You agree not to
use electronic processes that are automated and high-volume to access or
query the Whois database except as reasonably necessary to register
domain names or modify existing registrations. VeriSign reserves the right
to restrict your access to the Whois database in its sole discretion to ensure
operational stability. VeriSign may restrict or terminate your access to the
Whois database for failure to abide by these terms of use. VeriSign
reserves the right to modify these terms at any time.
The Registry database contains ONLY .COM, .NET, .EDU domains and
Registrars.
 132.226.44.1
132.226.44.1
 United States
United States
 InValid
SSL
InValid
SSL