Security Tutorials - Keeping Cyber Security Simple
Keeping Cyber Security Simple
Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en-gb
Response Time: 0.914969
SSL: Disable
Status: up
Code To Txt Ratio
Word Count 509
Links
ratio 1.6743274270139
Found 65 Top Alternative to Hempstutorials.co.uk

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.

 Erikdubois.be
Erikdubois.be
ERiK DuBoiS | Place to be
Creation of ArcoLinux-Candy-Beauty-Arc – combination of Arc folders with Beautyline icons What if you like the folder icons from Horst3180 and want them to combine with the BeautiLine icons from Sajjad. We are going to combine these two. In the meantime we have changed many things since their release and...
 Ndronic.us
Ndronic.us
Andronicus | Security Projects, Research, and Linux
A guide to public/private keys, ciphers, and other things you can do to harden your ssh server.

 Hackinglikeapro.blogspot.com
Hackinglikeapro.blogspot.com
HACKING LIKE A PRO
Friday, 28 April 2017 Tricks New How to control your Pc/Laptop from anywhere Rahul UK 17:12 20 Comments Want to impress your friend? Want to spy on your PC/Laptop? Want to use your PC/Laptop from anywhere in the world. Then you are ... Read More Read more 20 comments: By...
 Securitytraning.com
Securitytraning.com
securitytraning.com is for sale | HugeDomains
Get this domain name before someone else does. Quick and painless shopping. Affordable payment options available.

 Xeushack.com
Xeushack.com
Hacking Tutorials by Xeus
The most up to date ethical hacking tutorials and cyber security news.
 Virtualboxes.org
Virtualboxes.org
VirtualBoxes - Free VirtualBox® Images | Ready-to-use virtual machines for open-source operating systems
Welcome! This project provides virtual machines for Oracle VM VirtualBox® for several free and/or open-source operating systems, such as GNU/Linux or Free/Net/OpenBSD for testing, security and/or entertainment purposes. In most cases, we've done a minimal setup, to let you alter the images to your own needs and learn how to use the operating systems. We…

 Hackercool.com
Hackercool.com
Hackercool Magazine - Ethical Hacking Magazine for hackers
Hacking Magazine with a difference. That's what Hackercool Magazine is. Learn Blackhat hacking. is a cyber security monthly magazine that

 Hakin9.org
Hakin9.org
Home - Hakin9 - IT Security Magazine
Our tutorials, case studies and online courses will prepare you for the upcoming, potential threats in the cyber security world.

 Automatetheplanet.com
Automatetheplanet.com
Homepage - Automate The Planet
Taking Software Quality to New Heights Taking Software Quality to New Heights Are you tired of "Hello World" examples? Learn how to write automated tests through working real-world examples. We Know What Works ... Over the past seven years we have tried and done it all when it comes to...

 Concise-courses.com
Concise-courses.com
Resource For Hacker Tools & Growth / SEO Hacking Tools
Site Dedicated To Intrepid SEO Explorers
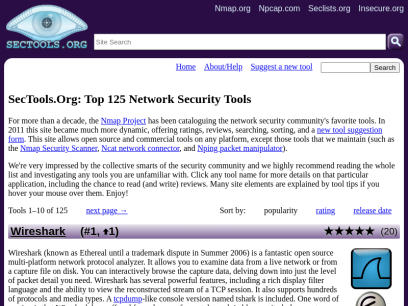
 Sectools.org
Sectools.org
SecTools.Org Top Network Security Tools
Rankings and reviews of computer and network security software, programs, and tools.

 Mintguide.org
Mintguide.org
MintGuide.Org • The kindest blog about Linux Mint
Linux Mint Guide is your reliable assistant for travelling into Linux Mint world. In our blog you can find a lot of news, articles, how to's, advices, tips'n'tricks which very helpful for beginners.

 Vulnhub.com
Vulnhub.com
Vulnerable By Design ~ VulnHub
VulnHub provides materials allowing anyone to gain practical hands-on experience with digital security, computer applications and network administration tasks.
 Adeptus-mechanicus.com
Adeptus-mechanicus.com
Main
"Turning and turning in the widening gyre The falcon cannot hear the falconer; Things fall apart; the centre cannot hold; Mere anarchy is loosed upon the world, The blood-dimmed tide is loosed, and everywhere The ceremony of innocence is drowned; The best lack all conviction, while the worst Are full...

 Tipstrickshack.blogspot.com
Tipstrickshack.blogspot.com
Hacking & Tricks
Sunday, February 9, 2014 How to install and use Veil-Catapult in backtrack? Posted by nirav desai at 1:34 AM 1:34 AM Labels: bypass AV, Veil-Catapult 5 comments Today we are gonna talk about Veil-Catapult.Veil-Catapult is payload delivery for when metasploit’s psexec getting caught by AV.It utilizes Veil-Evasion to generate AV-evading...
Technologies Used by hempstutorials.co.uk
Dns Records of hempstutorials.co.uk
A Record: 37.122.211.160AAAA Record:
CNAME Record:
NS Record: ns30.domaincontrol.com ns29.domaincontrol.com
SOA Record: dns.jomax.net
MX Record: mx0.123-reg.co.uk mx1.123-reg.co.uk
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of hempstutorials.co.uk
Domain name:
hempstutorials.co.uk
Data validation:
Nominet was able to match the registrant's name and address against a 3rd party data source on 01-Oct-2017
Registrar:
123-Reg Limited t/a 123-reg [Tag = 123-REG]
URL: https://www.123-reg.co.uk
Relevant dates:
Registered on: 07-Sep-2015
Expiry date: 07-Sep-2022
Last updated: 20-May-2022
Registration status:
Registered until expiry date.
Name servers:
ns29.domaincontrol.com
ns30.domaincontrol.com
WHOIS lookup made at 22:51:18 26-Jun-2022
--
This WHOIS information is provided for free by Nominet UK the central registry
for .uk domain names. This information and the .uk WHOIS are:
Copyright Nominet UK 1996 - 2022.
You may not access the .uk WHOIS or use any data from it except as permitted
by the terms of use available in full at https://www.nominet.uk/whoisterms,
which includes restrictions on: (A) use of the data for advertising, or its
repackaging, recompilation, redistribution or reuse (B) obscuring, removing
or hiding any or all of this notice and (C) exceeding query rate or volume
limits. The data is provided on an 'as-is' basis and may lag behind the
register. Access may be withdrawn or restricted at any time.
 192.0.78.9
192.0.78.9
 United States
United States
 Valid SSL
Valid SSL