:: bettercap
Core events.stream ticker caplets update api.rest ui c2 Bluetooth LE WiFi HID on 2.4Ghz IPv4 / IPv6 net.recon net.probe net.sniff - net.fuzz syn.scan wake on lan Spoofers arp.spoof dns.spoof dhcp6.spoof ndp.spoof (IPv6) Proxies any.proxy packet.proxy tcp.proxy http.proxy https.proxy Servers http.server https.server mdns.server mysql.server (rogue) Utils mac.changer gps

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.139913
SSL: Disable
Status: up
Code To Txt Ratio
Word Count 137
Links
ratio 8.6671292499842
Found 84 Top Alternative to Bettercap.org

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.

 Evilsocket.net
Evilsocket.net
evilsocket
Hi, my name is Simone (a male name in my country) and on the internet I'm known as evilsocket. I like computers, music, dogs, [books](https://www.goodreads.com/evilsocket), physics, [photography and t
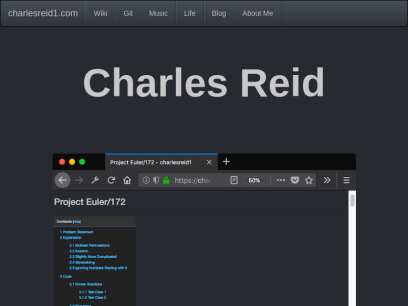
 Charlesreid1.com
Charlesreid1.com
charlesreid1
wiki: charlesreid1.com/wiki the wiki is a compilation of reading material, notes, scripts, logs, guides, lecture notes, and scattered thoughts. gitea: git.charlesreid1.com git.charlesreid1.com is where all of my code projects are hosted. gitea is a self-hosted github clone written in go. github: @charlesreid1 follow my coding work on github....

 Cyberpunk.rs
Cyberpunk.rs
CYBERPUNK | The Best Tutorials & CyberSecurity Tool Reviews
CyberPunk: The Best Tutorials & CyberSecurity Tool Reviews. Get informed about the latest ethical hacking and cybersecurity tool releases. Read Cyberpunk's ethical hacking tutorials/articles and watch usage videos...

 Kalitutorials.net
Kalitutorials.net
Kali Linux Hacking Tutorials
Thursday, December 6, 2018 Bypassing website blocking/censorship with Secure DNS and Encrypted SNI (cloudflare only) By Shashwat December 06, 2018 blocking, bypassing, censorship, cloudflare, esni, firefox, nightly, tls, tls1.3 Disclaimer - TLDR; some stuff here can be used to carry out illegal activity, our intention is, however, to educate I...
 Kalitut.com
Kalitut.com
KaliTut Linux and pentesting blog - KaliTut
Windows PowerShell tutorial for beginners Detailed PowerShell tutorial for beginners! ✓ Create and run PowerShell script, practice-oriented knowledge about PowerShell. Learn to Hack Steps from Beginner to Hacker Learn to hack , Beginner's Guide - with some many Tutorials on how to Hack Computers with Kali Install Linux PowerShell Tutorial...
 Kalitut.com
Kalitut.com
KaliTut Linux and pentesting blog - KaliTut
Windows PowerShell tutorial for beginners Detailed PowerShell tutorial for beginners! ✓ Create and run PowerShell script, practice-oriented knowledge about PowerShell. Learn to Hack Steps from Beginner to Hacker Learn to hack , Beginner's Guide - with some many Tutorials on how to Hack Computers with Kali Install Linux PowerShell Tutorial...
 Kali.tools
Kali.tools
Инструменты Kali Linux - Список инструментов для тестирования на проникновение и их описание
Сбор информации acccheck ace-voip Amap AQUATONE arp-scan Automater badKarma bing-ip2hosts braa Bro Bypass firewalls by abusing DNS history CaseFile CATPHISH CDPSnarf cisco-torch CloudFail Cookie Cadger copy-router-config DMitry dnmap dnsenum dnsmap DNSRecon dnstracer dnstwist dnswalk DotDotPwn Dublin Traceroute enum4linux enumIAX exploitdb EyeWitness Faraday FinalRecon Fierce Firewalk flashlight fragroute fragrouter Ghost Phisher...
 Kali.tools
Kali.tools
Инструменты Kali Linux - Список инструментов для тестирования на проникновение и их описание
Сбор информации acccheck ace-voip Amap AQUATONE arp-scan Automater badKarma bing-ip2hosts braa Bro Bypass firewalls by abusing DNS history CaseFile CATPHISH CDPSnarf cisco-torch CloudFail Cookie Cadger copy-router-config DMitry dnmap dnsenum dnsmap DNSRecon dnstracer dnstwist dnswalk DotDotPwn Dublin Traceroute enum4linux enumIAX exploitdb EyeWitness Faraday FinalRecon Fierce Firewalk flashlight fragroute fragrouter Ghost Phisher...

 Miloserdov.org
Miloserdov.org
Ethical hacking and penetration testing - InfoSec, IT, Kali Linux, BlackArch
The complete guide to Wine: from installation to advanced usage Table of contents 1. Why Wine 2. Features and limitations of Wine 3. 64-bit or 32-bit Wine? 4. How to install Wine 4.1 Installing Wine on Debian, Kali Linux, Linux Mint, Ubuntu, and their derivatives 4.2 Installing Wine on Arch Linux 5. How...

 Miloserdov.org
Miloserdov.org
Ethical hacking and penetration testing - InfoSec, IT, Kali Linux, BlackArch
The complete guide to Wine: from installation to advanced usage Table of contents 1. Why Wine 2. Features and limitations of Wine 3. 64-bit or 32-bit Wine? 4. How to install Wine 4.1 Installing Wine on Debian, Kali Linux, Linux Mint, Ubuntu, and their derivatives 4.2 Installing Wine on Arch Linux 5. How...



 Cybervie.com
Cybervie.com
Best Cyber Security Training and Certified Courses | Cybervie
Cybervie is an Indian company, started in 2017 located in Hyderabad & provides all forms of cybersecurity training to make your career.

 Cybervie.com
Cybervie.com
Best Cyber Security Training and Certified Courses | Cybervie
Cybervie is an Indian company, started in 2017 located in Hyderabad & provides all forms of cybersecurity training to make your career.

 Hackingvision.com
Hackingvision.com
HackingVision – Ethical Hacking Tutorials, Tips & Tricks, Kali Linux, Beginners Hacking
Top Colleges for Cybersecurity Degree Programs 1st June 2022 by Carl Hill Cybersecurity has a great job market with many job vacancies and attractive salaries. When you have a cybersecurity degree, you can easily find job opportunities such as security engineers. Therefore, training begins at the college level when you...

 Hackingvision.com
Hackingvision.com
HackingVision – Ethical Hacking Tutorials, Tips & Tricks, Kali Linux, Beginners Hacking
Top Colleges for Cybersecurity Degree Programs 1st June 2022 by Carl Hill Cybersecurity has a great job market with many job vacancies and attractive salaries. When you have a cybersecurity degree, you can easily find job opportunities such as security engineers. Therefore, training begins at the college level when you...
 Prodefence.org
Prodefence.org
Prodefence - Cyber Security Services | Malware & Pentesting
Cyber security services - Malware analysis - Penetration testing - Data protection
 Prodefence.org
Prodefence.org
Prodefence - Cyber Security Services | Malware & Pentesting
Cyber security services - Malware analysis - Penetration testing - Data protection
 Pentestmag.com
Pentestmag.com
Home - Pentestmag
Pentest Magazine, Penetration Testing, Pentest Training, Penetration Testing Online Course, CERTIFIED ETHICAL HACKER CEH, METASPLOIT
 Pentestmag.com
Pentestmag.com
Home - Pentestmag
Pentest Magazine, Penetration Testing, Pentest Training, Penetration Testing Online Course, CERTIFIED ETHICAL HACKER CEH, METASPLOIT
 Clan.su
Clan.su
Бесплатный конструктор сайтов. Создайте свой сайт самостоятельно!
Как создать свой сайт? Самостоятельно! В конструкторе сайтов uCoz это легко и практически бесплатно.
Technologies Used by bettercap.org
Dns Records of bettercap.org
A Record: 104.21.90.57 172.67.153.136AAAA Record: 2606:4700:3036::6815:5a39 2606:4700:3032::ac43:9988
CNAME Record:
NS Record: sue.ns.cloudflare.com ben.ns.cloudflare.com
SOA Record: dns.cloudflare.com
MX Record: fb.mail.gandi.net spool.mail.gandi.net
SRV Record:
TXT Record: google-site-verification=lmyFlDlKmVNvnjt6WNW3u-JDKY5cpU0z-c7-K7Z6frs
DNSKEY Record:
CAA Record:
Whois Detail of bettercap.org
Domain Name: bettercap.orgRegistry Domain ID: D176946489-LROR
Registrar WHOIS Server: whois.gandi.net
Registrar URL: http://www.gandi.net
Updated Date: 2022-06-04T05:04:24Z
Creation Date: 2015-07-25T14:48:27Z
Registrar Registration Expiration Date: 2025-07-25T16:48:27Z
Registrar: GANDI SAS
Registrar IANA ID: 81
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +33.170377661
Reseller:
Domain Status: clientTransferProhibited http://www.icann.org/epp#clientTransferProhibited
Domain Status:
Domain Status:
Domain Status:
Domain Status:
Registry Registrant ID: REDACTED FOR PRIVACY
Registrant Name: REDACTED FOR PRIVACY
Registrant Organization:
Registrant Street: 63-65 boulevard Massena
Registrant City: Paris
Registrant State/Province: Paris
Registrant Postal Code: 75013
Registrant Country: FR
Registrant Phone: +33.170377666
Registrant Phone Ext:
Registrant Fax: +33.143730576
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID: REDACTED FOR PRIVACY
Admin Name: REDACTED FOR PRIVACY
Admin Organization:
Admin Street: 63-65 boulevard Massena
Admin City: Paris
Admin State/Province: Paris
Admin Postal Code: 75013
Admin Country: FR
Admin Phone: +33.170377666
Admin Phone Ext:
Admin Fax: +33.143730576
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID: REDACTED FOR PRIVACY
Tech Name: REDACTED FOR PRIVACY
Tech Organization:
Tech Street: 63-65 boulevard Massena
Tech City: Paris
Tech State/Province: Paris
Tech Postal Code: 75013
Tech Country: FR
Tech Phone: +33.170377666
Tech Phone Ext:
Tech Fax: +33.143730576
Tech Fax Ext:
Tech Email: [email protected]
Name Server: BEN.NS.CLOUDFLARE.COM
Name Server: SUE.NS.CLOUDFLARE.COM
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
DNSSEC: Unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-08-13T18:29:28Z <<<
For more information on Whois status codes, please visit
https://www.icann.org/epp
Reseller Email:
Reseller URL:
Personal data access and use are governed by French law, any use for the purpose of unsolicited mass commercial advertising as well as any mass or automated inquiries (for any intent other than the registration or modification of a domain name) are strictly forbidden. Copy of whole or part of our database without Gandi's endorsement is strictly forbidden.
A dispute over the ownership of a domain name may be subject to the alternate procedure established by the Registry in question or brought before the courts.
For additional information, please contact us via the following form:
https://www.gandi.net/support/contacter/mail/
 192.0.78.9
192.0.78.9
 United States
United States
 Valid SSL
Valid SSL
