Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time:
SSL: Enable
Status: up
Code To Txt Ratio
Word Count
Links
ratio
SSL Details
SSL Issuer:
Issuer: Starfield Secure Certificate Authority - G2
Valid From: 2021-11-12 08:48:22
Expiration Date: 2022-12-11 19:45:12
SSL Organization:
Signature 8e6c3608ba8eb9b4eaca53571986ff73cb36e00a
Algorithm: RSA-SHA256
Found 74 Top Alternative to Brutelogic.com.br
 Excess-xss.com
Excess-xss.com
Excess XSS: A comprehensive tutorial on cross-site scripting
A comprehensive tutorial on cross-site scripting.

 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.
 Neuralegion.com
Neuralegion.com
Bright Security: Developer-Friendly DAST - CI/CD Security Testing - Bright Security
Bright Security is the next generation AI-powered DAST. Discover OWASP Top 10 and zero days with no false positives.

 Aptive.co.uk
Aptive.co.uk
Aptive Cyber Security
Aptive are a UK based cyber security consultancy, specialising in infrastructure & web application security testing. We are passionate about Cyber Security and helping our clients improve the security of their environments.
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.
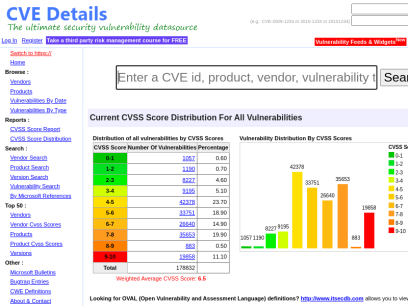
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time
 Appspot.com
Appspot.com
Google Cloud Platform
Email or phone Forgot email? Not your computer? Use a private browsing window to sign in. Learn more Next Create account

 Enciphers.com
Enciphers.com
Penetration Testing | Vulnerability Assessment | Security Training
Advance Penetration Testing, Vulnerability Assessment, Security Training

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.
 Securitum.com
Securitum.com
research.securitum.com - securitum.com vulnerabilities researches and cyber security education publications
securitum.com vulnerabilities researches and cyber security education publications

 Chefsecure.com
Chefsecure.com
Learn Cybersecurity for Hackers, Students & – Chef Secure
Learn how hacking attacks and defenses work through fun, hands-on training with code on ethical hacking and software engineering best practices.

 Perspectiverisk.com
Perspectiverisk.com
Cyber Security and Penetration Testing Services - Perspective Risk
At Perspective Risk, a Content+Cloud company, our security professionals are obsessed by cyber security. We are the leading Pen Test company in the UK.

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.
 Xsshunter.com
Xsshunter.com
XSS Hunter
...you may be missing the most critical vulnerabilities! XSS Hunter is a better way to do Cross-site Scripting. Learn more about how XSS Hunter can help you find even blind XSS...

 Intigriti.com
Intigriti.com
Intigriti - Bug Bounty & Agile Pentesting Platform
Intigriti offers bug bounty and agile penetration testing solutions powered by Europe's #1 leading network of ethical hackers.

 Cobalt.io
Cobalt.io
Pentest as a Service | Cobalt
Cobalt is modernizing traditional pentesting. We leverage global talent and a SaaS platform to deliver a better pentest via Pentest as a Service (PtaaS).

 Secjuice.com
Secjuice.com
Secjuice | Non-Profit Cyber Goodness
The only non-profit, independent & volunteer based publication in the information security industry. Cybersecurity articles written by hackers.

 Pentester.land
Pentester.land
Pentester Land · Offensive Infosec
The newsletter is dead, long live the newsletter! 12 Jul 2020 • newsletter This is a long due post. Since The 5 Hacking Newsletter has stopped on this blog, I’ve been getting many questions about it. So, even though most readers already know by now, here’s a summary of what...
 Securityidiots.com
Securityidiots.com
Welcome to Security Idiots!!
Security Idiots is a place where some insane idiots try thier hands on with Security.

 Secproject.com
Secproject.com
Soroush Dalili (@irsdl) – سروش دلیلی | Web AppSec ninja, a semicolon enthusiast!
Table of Contents: Introduction 1. Execute command using web.config in the root or an application directory 1.1. Executing web.config as an ASPX page 1.2. Running command using AspNetCoreModule 1.3. Using Machine Key 1.4. Using JSON_AppService.axd 2. Execute command using web.config in a subfolder/virtual directory 2.1. Abusing the compilerOptions attribute 2.1.1....

 Kuliukas.com
Kuliukas.com
Just another WordPress site – Just another WordPress site
Posts Posted on November 5, 2017 Hello world! Welcome to WordPress. This is your first post. Edit or delete it, then start writing! Search for: Search Recent Posts Hello world! Recent Comments A WordPress Commenter on Hello world! Archives November 2017 Categories Uncategorized Meta Log in Entries feed Comments feed...
 Ptsecurity.com
Ptsecurity.com
Positive Technologies - vulnerability assessment, compliance management and threat analysis solutions
Positive Technologies - vulnerability assessment, compliance management and threat analysis solutions

 Doyensec.com
Doyensec.com
Doyensec :: Build with Security
Doyensec is an independent security research and development company focused on vulnerability discovery and remediation.

 Codegrazer.com
Codegrazer.com
CodeGrazer: Penetration Testing Services
CodeGrazer is the newly formed pentest firm based in Leeds, UK, offering security services to protect private companies internal infrastructure and web services with quick turnaround and high quality standards.

 Gracefulsecurity.com
Gracefulsecurity.com
Akimbo Core
Your Vulnerability Management Sucks Published: 16 March 2022 On March 16th I had the pleasure of speaking at the Yorkshire Cyber Security Cluster about Vulnerability Management. I've included my slides from the presentation and some speaker notes on the content covered here. Continue Reading HTTP Security Headers: Cache-Control Published: 21...
Technologies Used by brutelogic.com.br
Dns Records of brutelogic.com.br
A Record: 192.124.249.5AAAA Record:
CNAME Record:
NS Record: 19.sucuridns.com 18.sucuridns.com 13.sucuridns.com 17.sucuridns.com
SOA Record: soc.sucuri.net
MX Record: alt2.aspmx.l.google.com alt1.aspmx.l.google.com aspmx.l.google.com alt4.aspmx.l.google.com alt3.aspmx.l.google.com
SRV Record:
TXT Record: google-site-verification=po1AKkyHM7HjlOIreej0fyK2z0yvH2BiejFlVjYlOE4 brave-ledger-verification=437b332450d43ff01d034f90c93210e720bdcb12c7d3665a0080459163be3fc5
DNSKEY Record:
CAA Record:
Whois Detail of brutelogic.com.br
% Copyright (c) Nic.br
% The use of the data below is only permitted as described in
% full by the Use and Privacy Policy at https://registro.br/upp ,
% being prohibited its distribution, commercialization or
% reproduction, in particular, to use it for advertising or
% any similar purpose.
% 2022-07-09T06:10:50-03:00 - IP: 85.190.254.214
domain: brutelogic.com.br
owner: Brute Logic
owner-c: ROAAS24
tech-c: ROAAS24
nserver: 13.sucuridns.com
nsstat: 20220707 AA
nslastaa: 20220707
nserver: 17.sucuridns.com
nsstat: 20220707 AA
nslastaa: 20220707
nserver: 18.sucuridns.com
nsstat: 20220707 AA
nslastaa: 20220707
nserver: 19.sucuridns.com
nsstat: 20220707 AA
nslastaa: 20220707
saci: yes
created: 20150824 #14588812
changed: 20151125
expires: 20250824
status: published
nic-hdl-br: ROAAS24
person: Rodolfo Amorim de Assis
created: 20150824
changed: 20150824
% Security and mail abuse issues should also be addressed to
% cert.br, http://www.cert.br/ , respectivelly to [email protected]
% and [email protected]
%
% whois.registro.br accepts only direct match queries. Types
% of queries are: domain (.br), registrant (tax ID), ticket,
% provider, CIDR block, IP and ASN.
 172.104.133.158
172.104.133.158
 United States
United States
 Valid SSL
Valid SSL