Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time:
SSL: Disable
Status: up
Code To Txt Ratio
Word Count
Links
ratio
Found 75 Top Alternative to Hacktricks.xyz


 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.

 Pentesterlab.com
Pentesterlab.com
PentesterLab: Learn Web Penetration Testing: The Right Way
WHAT OUR PRO MEMBERS SAY: 10010101 10110110 1010 “I consider PentesterLab to be a great resource for learning about web application security and ways how it can be subverted. Even though the exercises usually don’t take much time to complete they can teach a lot. I can’t but recommend it,...

 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.

 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.
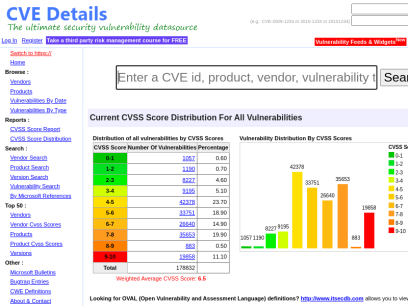
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers
 Aldeid.com
Aldeid.com
aldeid
Pentesting   •    Web Exploitation   •    Cryptography   •    Forensics   •    Reversing   •    Binary Exploitation   •    CTF   •    Threat Hunting TryHackMe > Unbaked Pie Sun, 6 Jun 2021 11:34:00 +0000 Enumerate a Django application, find a vulnerability, exploit a pickle session cookie, evade a docker environment, find a way to forward ports, brute force an SSH account, this challenge...

 Netsparker.com
Netsparker.com
Invicti | Web Application Security For Enterprise
Get accurate, automated application security testing that scales like no other solution. Secure 1000s of web assets with less manual effort. Reduce your risk with the only…

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.

 Intigriti.com
Intigriti.com
Intigriti - Bug Bounty & Agile Pentesting Platform
Intigriti offers bug bounty and agile penetration testing solutions powered by Europe's #1 leading network of ethical hackers.

 Securityonline.info
Securityonline.info
Penetration Testing • Information Security
Securityonline is a huge security community. It is committed to the sharing of high-quality technical articles and safety reports, focusing on high-quality security and security incidents in the industry.

 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Tryhackme.com
Tryhackme.com
TryHackMe | Cyber Security Training
TryHackMe is a free online platform for learning cyber security, using hands-on exercises and labs, all through your browser!
 Kitploit.com
Kitploit.com
KitPloit - PenTest & Hacking Tools
Leading source of security tools, hacking tools, cybersecurity and network security. Learn about new tools and updates in one place.

 Pentestmonkey.net
Pentestmonkey.net
pentestmonkey | Taking the monkey work out of pentesting
mimikatz: Tool To Recover Cleartext Passwords From Lsass December 20, 2011, pentestmonkey I meant to blog about this a while ago, but never got round to it. Here’s a brief post about very cool feature of a tool called mimikatz. I’m very grateful to the tool’s author for bringing it...

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...

 Vulnhub.com
Vulnhub.com
Vulnerable By Design ~ VulnHub
VulnHub provides materials allowing anyone to gain practical hands-on experience with digital security, computer applications and network administration tasks.
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Blackhat.com
Blackhat.com
Black Hat | Home
Black Hat Webinars Security Research in Real Time June 30, 2022 - Managing Cybersecurity as a Business Risk July 14, 2022 - InfoSec Lessons from the War in Ukraine Sponsor a Webinars View all of our recent Webinars Black Hat Archives Watch Past Presentations View all of our archived videos...
 Crackstation.net
Crackstation.net
CrackStation - Online Password Hash Cracking - MD5, SHA1, Linux, Rainbow Tables, etc.
Crackstation is the most effective hash cracking service. We crack: MD5, SHA1, SHA2, WPA, and much more...
 Hackertarget.com
Hackertarget.com
28 Online Vulnerability Scanners & Network Tools | HackerTarget.com
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.

 Sans.org
Sans.org
Cyber Security Training | SANS Courses, Certifications & Research
SANS Institute is the most trusted resource for cybersecurity training, certifications and research. Offering more than 60 courses across all practice areas, SANS trains over 40,000 cybersecurity professionals annually.

 Ired.team
Ired.team
What is ired.team? - Red Teaming Experiments
My notes about all things red teaming experiments and more.
 Neuralegion.com
Neuralegion.com
Bright Security: Developer-Friendly DAST - CI/CD Security Testing - Bright Security
Bright Security is the next generation AI-powered DAST. Discover OWASP Top 10 and zero days with no false positives.

 Md5decrypt.net
Md5decrypt.net
Md5 Decryption & Encryption Gratuite - Plus de 15.000.000.000 hashs
Decryption Md5 : Le Md5 (Message Digest 5) est une fonction cryptographique qui permet de "hasher" (encrypter) une séquence numérique en un hash md5 de 128 bits, soit 32 caractères, et ce peu importe la longueur de la séquence originale. Ce système cryptographique est irréversible, il n'est pas possible d'obtenir...
 Securityidiots.com
Securityidiots.com
Welcome to Security Idiots!!
Security Idiots is a place where some insane idiots try thier hands on with Security.
 Kalilinuxtutorials.com
Kalilinuxtutorials.com
Kali Linux Tutorials - A Single Stop for Kali Linux Tools
Kali Linux tutorials is an independent platform that covers step by tutorials, advanced penetration testing, Ethical Hacking and network security tools.

 Enciphers.com
Enciphers.com
Penetration Testing | Vulnerability Assessment | Security Training
Advance Penetration Testing, Vulnerability Assessment, Security Training

 Frida.re
Frida.re
Frida • A world-class dynamic instrumentation framework | Inject JavaScript to explore native apps on Windows, macOS, GNU/Linux, iOS, Android, and QNX
Inject JavaScript to explore native apps on Windows, macOS, GNU/Linux, iOS, Android, and QNX

 Pentesttools.net
Pentesttools.net
PentestTools - Penetration Testing Tools.
Latest Penetration Testing Tools. Cyber Security and Technology News. High Quality Penetration Testing Videos.
 Kali.tools
Kali.tools
Инструменты Kali Linux - Список инструментов для тестирования на проникновение и их описание
Сбор информации acccheck ace-voip Amap AQUATONE arp-scan Automater badKarma bing-ip2hosts braa Bro Bypass firewalls by abusing DNS history CaseFile CATPHISH CDPSnarf cisco-torch CloudFail Cookie Cadger copy-router-config DMitry dnmap dnsenum dnsmap DNSRecon dnstracer dnstwist dnswalk DotDotPwn Dublin Traceroute enum4linux enumIAX exploitdb EyeWitness Faraday FinalRecon Fierce Firewalk flashlight fragroute fragrouter Ghost Phisher...
 Prodefence.org
Prodefence.org
Prodefence - Cyber Security Services | Malware & Pentesting
Cyber security services - Malware analysis - Penetration testing - Data protection

 Secproject.com
Secproject.com
Soroush Dalili (@irsdl) – سروش دلیلی | Web AppSec ninja, a semicolon enthusiast!
Table of Contents: Introduction 1. Execute command using web.config in the root or an application directory 1.1. Executing web.config as an ASPX page 1.2. Running command using AspNetCoreModule 1.3. Using Machine Key 1.4. Using JSON_AppService.axd 2. Execute command using web.config in a subfolder/virtual directory 2.1. Abusing the compilerOptions attribute 2.1.1....

 Trustedsec.com
Trustedsec.com
TrustedSec | Cybersecurity
Cybersecurity consultants with expertise in penetration testing, social engineering and enterprise risk management - Learn how TrustedSec can help protect your company.
 Outpost24.com
Outpost24.com
Cyber Security Risk Management Solutions | Outpost 24
Outpost24's intelligent cyber risk management solution provide continuous visibility on the vulnerabilities and cyber threats affecting your organization to accelerate remediation - before attackers exploit them

 1337pwn.com
1337pwn.com
1337pwn ⋆
1337pwn provides tutorials on ethical hacking, digital forensics, Kali Linux, Metasploit, WiFi hacking, and FTK Imager.

 Notsosecure.com
Notsosecure.com
NotSoSecure | Part of Claranet Cyber Security
NotSoSecure is one of the largest training providers at Black Hat conferences and trains hundreds of individuals throughout the year. Our trainers are also pen testers and we use a research led approach to ensure our training and testing is always of the highest quality.

 Pentester.land
Pentester.land
Pentester Land · Offensive Infosec
The newsletter is dead, long live the newsletter! 12 Jul 2020 • newsletter This is a long due post. Since The 5 Hacking Newsletter has stopped on this blog, I’ve been getting many questions about it. So, even though most readers already know by now, here’s a summary of what...


 Aptive.co.uk
Aptive.co.uk
Aptive Cyber Security
Aptive are a UK based cyber security consultancy, specialising in infrastructure & web application security testing. We are passionate about Cyber Security and helping our clients improve the security of their environments.

 Fuzzysecurity.com
Fuzzysecurity.com
FuzzySecurity | Home
Welcome to FuzzySecurity 2.0 bringing you new content in responsive HTML5 and CSS3!! Introduction "Beware of fuzzy security-monsters!!". Hello and welcome everybody, it has been an interesting ride so far and there is much more to come. I would like to take a moment to say a few things and...

 Blackarch.org
Blackarch.org
BlackArch Linux - Penetration Testing Distribution
BlackArch Linux is a lightweight expansion to Arch Linux for penetration testers.

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.

 Gracefulsecurity.com
Gracefulsecurity.com
Akimbo Core
Your Vulnerability Management Sucks Published: 16 March 2022 On March 16th I had the pleasure of speaking at the Yorkshire Cyber Security Cluster about Vulnerability Management. I've included my slides from the presentation and some speaker notes on the content covered here. Continue Reading HTTP Security Headers: Cache-Control Published: 21...
Technologies Used by hacktricks.xyz
Dns Records of hacktricks.xyz
A Record:AAAA Record:
CNAME Record:
NS Record: ns06.domaincontrol.com ns05.domaincontrol.com
SOA Record: dns.jomax.net
MX Record:
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of hacktricks.xyz
Domain Name: hacktricks.xyzRegistry Domain ID: D106298271-CNIC
Registrar WHOIS Server: whois.godaddy.com
Registrar URL: https://www.godaddy.com
Updated Date: 2022-06-05T15:06:46Z
Creation Date: 2019-06-04T18:48:22Z
Registrar Registration Expiration Date: 2023-06-04T23:59:59Z
Registrar: GoDaddy.com, LLC
Registrar IANA ID: 146
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.4806242505
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: clientUpdateProhibited https://icann.org/epp#clientUpdateProhibited
Domain Status: clientRenewProhibited https://icann.org/epp#clientRenewProhibited
Domain Status: clientDeleteProhibited https://icann.org/epp#clientDeleteProhibited
Registry Registrant ID: CR374328274
Registrant Name: Registration Private
Registrant Organization: Domains By Proxy, LLC
Registrant Street: DomainsByProxy.com
Registrant Street: 2155 E Warner Rd
Registrant City: Tempe
Registrant State/Province: Arizona
Registrant Postal Code: 85284
Registrant Country: US
Registrant Phone: +1.4806242599
Registrant Phone Ext:
Registrant Fax: +1.4806242598
Registrant Fax Ext:
Registrant Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=hacktricks.xyz
Registry Admin ID: CR374328276
Admin Name: Registration Private
Admin Organization: Domains By Proxy, LLC
Admin Street: DomainsByProxy.com
Admin Street: 2155 E Warner Rd
Admin City: Tempe
Admin State/Province: Arizona
Admin Postal Code: 85284
Admin Country: US
Admin Phone: +1.4806242599
Admin Phone Ext:
Admin Fax: +1.4806242598
Admin Fax Ext:
Admin Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=hacktricks.xyz
Registry Tech ID: CR374328275
Tech Name: Registration Private
Tech Organization: Domains By Proxy, LLC
Tech Street: DomainsByProxy.com
Tech Street: 2155 E Warner Rd
Tech City: Tempe
Tech State/Province: Arizona
Tech Postal Code: 85284
Tech Country: US
Tech Phone: +1.4806242599
Tech Phone Ext:
Tech Fax: +1.4806242598
Tech Fax Ext:
Tech Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=hacktricks.xyz
Name Server: NS05.DOMAINCONTROL.COM
Name Server: NS06.DOMAINCONTROL.COM
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-07-03T13:25:23Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
TERMS OF USE: The data contained in this registrar's Whois database, while believed by the
registrar to be reliable, is provided "as is" with no guarantee or warranties regarding its
accuracy. This information is provided for the sole purpose of assisting you in obtaining
information about domain name registration records. Any use of this data for any other purpose
is expressly forbidden without the prior written permission of this registrar. By submitting
an inquiry, you agree to these terms and limitations of warranty. In particular, you agree not
to use this data to allow, enable, or otherwise support the dissemination or collection of this
data, in part or in its entirety, for any purpose, such as transmission by e-mail, telephone,
postal mail, facsimile or other means of mass unsolicited, commercial advertising or solicitations
of any kind, including spam. You further agree not to use this data to enable high volume, automated
or robotic electronic processes designed to collect or compile this data for any purpose, including
mining this data for your own personal or commercial purposes. Failure to comply with these terms
may result in termination of access to the Whois database. These terms may be subject to modification
at any time without notice.
 104.21.13.249
104.21.13.249
 United States
United States
 Valid SSL
Valid SSL