Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

Stats
Alexa Rank: 24284
Popular in Country: United States
Country Alexa Rank: 15760
language: en
Response Time: 1.107804
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 1642
Links
ratio 26.282911563807
SSL Details
SSL Issuer:
Issuer: Amazon
Valid From: 2022-03-31 00:00:00
Expiration Date: 2023-04-29 23:59:59
SSL Organization:
Signature d0c5bbbd5a4b8ad8673d00a603e5912a10c614df
Algorithm: RSA-SHA256
Found 75 Top Alternative to Rapid7.com
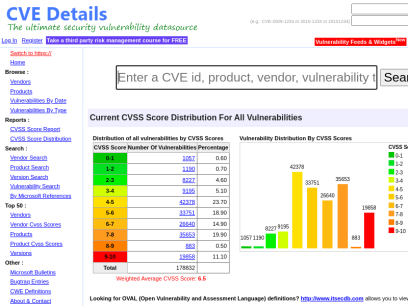
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.
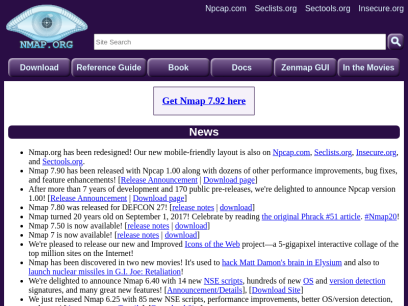
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.


 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.


 Kali.org
Kali.org
Kali Linux | Penetration Testing and Ethical Hacking Linux Distribution
Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking and network security assessments.

 Sans.org
Sans.org
Cyber Security Training | SANS Courses, Certifications & Research
SANS Institute is the most trusted resource for cybersecurity training, certifications and research. Offering more than 60 courses across all practice areas, SANS trains over 40,000 cybersecurity professionals annually.
 Metasploit.com
Metasploit.com
Metasploit | Penetration Testing Software, Pen Testing Security | Metasploit
Find security issues, verify vulnerability mitigations & manage security assessments with Metasploit. Get the world's best penetration testing software now.
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.

 Netsparker.com
Netsparker.com
Invicti | Web Application Security For Enterprise
Get accurate, automated application security testing that scales like no other solution. Secure 1000s of web assets with less manual effort. Reduce your risk with the only…

 Qualys.com
Qualys.com
Information Security and Compliance | Qualys
Qualys, Inc. helps your business automate the full spectrum of auditing, compliance and protection of your IT systems and web applications.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers

 Threatpost.com
Threatpost.com
Threatpost | The first stop for security news
Threatpost, is an independent news site which is a leading source of information about IT and business security for hundreds of thousands of professionals worldwide.
 Csoonline.com
Csoonline.com
CSO - CSO Online – IT-Security-News für Profis
News und Insights zur Cybersicherheit im Unternehmen. Alles was CSOs wissen müssen.

 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.
 Hackertarget.com
Hackertarget.com
28 Online Vulnerability Scanners & Network Tools | HackerTarget.com
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.
 Nist.gov
Nist.gov
National Institute of Standards and Technology | NIST
NIST promotes U.S. innovation and industrial competitiveness by advancing measurement science, standards, and technology in ways that enhance economic security and improve our quality of life.
 Imperva.com
Imperva.com
Cyber Security Leader | Imperva, Inc.
Imperva provides complete cyber security by protecting what really matters most—your data and applications—whether on-premises or in the cloud.

 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.
 Wonderhowto.com
Wonderhowto.com
Wonder How To » Fresh Hacks For a Changing World
Wonder How To is your guide to free how to videos on the Web. Search, Browse and Discover the best how to videos across the web using the largest how to video index on the web. Watch the best online video instructions, tutorials, & How-Tos for free. Have your own how to videos? Submit them to share with the world.

 Veracode.com
Veracode.com
Confidently secure apps you build and manage with Veracode
This simple and scalable solution enables you to create more secure software so that you can boost your business and reduce risk without hindering innovation.

 Tryhackme.com
Tryhackme.com
TryHackMe | Cyber Security Training
TryHackMe is a free online platform for learning cyber security, using hands-on exercises and labs, all through your browser!

 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies

 Blackhat.com
Blackhat.com
Black Hat | Home
Black Hat Webinars Security Research in Real Time June 30, 2022 - Managing Cybersecurity as a Business Risk July 14, 2022 - InfoSec Lessons from the War in Ukraine Sponsor a Webinars View all of our recent Webinars Black Hat Archives Watch Past Presentations View all of our archived videos...
 Digitalguardian.com
Digitalguardian.com
Enterprise IP & DLP Software | Digital Guardian
The Industry’s Only SaaS Solution for Enterprise DLP powered by Our unique approach to DLP allows for quick deployment and on-demand scalability, while providing full data visibility and no-compromise protection SCHEDULE A DEMO Compatible with No-Compromise Data Protection That Stops Data Loss Cloud-Delivered Powered by AWS, Digital Guardian delivers simplified...

 Us-cert.gov
Us-cert.gov
Homepage | CISA
As part of its mission, CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.

 Paloaltonetworks.com
Paloaltonetworks.com
Global Cybersecurity Leader - Palo Alto Networks
Palo Alto Networks enables your team to prevent successful cyberattacks with an automated approach that delivers consistent security across cloud, network and mobile.
 Eccouncil.org
Eccouncil.org
Certified Ethical Hacker | InfoSec Cyber Security Certification | EC-Council
EC-Council is a global leader in InfoSec Cyber Security certification programs like Certified Ethical Hacker and Computer Hacking Forensic Investigator.

 Netwrix.com
Netwrix.com
Netwrix | Powerful Data Security Made Easy.
Easily identify sensitive, regulated and mission-critical information in your data stores and focus on the information that truly requires protection.

 Varonis.com
Varonis.com
Varonis: We Protect Data
Varonis is a pioneer in data security and analytics, fighting a different battle than conventional cybersecurity companies.

 Esecurityplanet.com
Esecurityplanet.com
eSecurity Planet: Latest Cybersecurity News for IT Professionals
eSecurity Planet provides the latest cybersecurity news, trends, and software reviews for IT leaders. Browse our buyer's guides and analysis now.

 Checkpoint.com
Checkpoint.com
Leader in Cyber Security Solutions | Check Point Software
Check Point Infinity architecture delivers consolidated Gen V cyber security across networks, cloud, and mobile environments.

 Trendmicro.com
Trendmicro.com
#1 bei Cloud-Sicherheit & Endpunkt-Cybersicherheit | Trend Micro (DE)
Trend Micro ist der weltweit führende Anbieter von Plattformlösungen für Cloud-Sicherheit, XDR und Cybersicherheit – für Unternehmen, Rechenzentren, Cloud-Umgebungen, Netzwerke und Endpunkte.

 Splunk.com
Splunk.com
Splunk | The Data Platform for the Hybrid World
Splunk is the data platform that powers enterprise observability, unified security and limitless custom applications in hybrid environments.

 Giac.org
Giac.org
Cyber Security Certifications | GIAC Certifications
GIAC Certifications develops and administers premier, professional information security certifications. More than 30 certifications align with SANS training and ensure mastery in critical, specialized InfoSec domains. GIAC certifications provide the highest and most rigorous assurance of cyber security knowledge and skill available to industry, government, and military clients across the world.

 Upguard.com
Upguard.com
Third-Party Risk and Attack Surface Management Software | UpGuard
Third-party risk and attack surface management software. UpGuard is the best platform for securing your organization’s sensitive data. Our security ratings engine monitors millions of companies and billions of data points every day.

 Vulnhub.com
Vulnhub.com
Vulnerable By Design ~ VulnHub
VulnHub provides materials allowing anyone to gain practical hands-on experience with digital security, computer applications and network administration tasks.
 Kalilinuxtutorials.com
Kalilinuxtutorials.com
Kali Linux Tutorials - A Single Stop for Kali Linux Tools
Kali Linux tutorials is an independent platform that covers step by tutorials, advanced penetration testing, Ethical Hacking and network security tools.

 Securityonline.info
Securityonline.info
Penetration Testing • Information Security
Securityonline is a huge security community. It is committed to the sharing of high-quality technical articles and safety reports, focusing on high-quality security and security incidents in the industry.

 Asciinema.org
Asciinema.org
asciinema - Record and share your terminal sessions, the simple way
core/ca-certificates-utils 20210603-1 [instal.. │ Last Modified : Mon, 08 Ju core/coreutils 8.32-1 [installed] │ Out Of Date : No core/cracklib 2.9.7-2 [installed] │ core/crda 4.14-4 │ core/cronie 1.5.7-2 │ core/cryptsetup 2.4.0-1 [installed] │ core/curl 7.78.0-1 [installed] │ core/dash 0.5.11.4-1 │ core/db 5.3.28-5 [installed] │ core/dbus 1.12.20-1 [installed] │ core/dbus-docs 1.12.20-1...

 Detectify.com
Detectify.com
Attack Surface Management Tool Powered By Ethical Hackers | Detectify
Detectify's external attack surface management tool - assess, prioritize, remediate continuously growing external attack surfaces.
 Cybrary.it
Cybrary.it
Free Cybersecurity Training and Career Development | Cybrary
Cybersecurity training from Cybrary will take your career to the next level. We have the cybersecurity courses that can help get you there!
 Alienvault.com
Alienvault.com
AlienVault is now AT&T Cybersecurity
At AT&T Cybersecurity our mission is to provide phenomenal threat intelligence, collaborative defense & effective security for organizations of all sizes.
 Darkreading.com
Darkreading.com
Dark Reading | Security | Protect The Business
Cyber security's comprehensive news site is now an online community for security professionals, outlining cyber threats and the technologies for defending against them.
 Snyk.io
Snyk.io
Snyk | Developer security | Develop fast. Stay secure.
Snyk helps software-driven businesses develop fast and stay secure. Continuously find and fix vulnerabilities for npm, Maven, NuGet, RubyGems, PyPI and more.

 Logentries.com
Logentries.com
Log Management & Analysis Software Made Easy | Logentries
Log management and analytics by Logentries for development, IT operations and Security teams. 100% free service trusted by thousands of customers worldwide.
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.
 Aldeid.com
Aldeid.com
aldeid
Pentesting   •    Web Exploitation   •    Cryptography   •    Forensics   •    Reversing   •    Binary Exploitation   •    CTF   •    Threat Hunting TryHackMe > Unbaked Pie Sun, 6 Jun 2021 11:34:00 +0000 Enumerate a Django application, find a vulnerability, exploit a pickle session cookie, evade a docker environment, find a way to forward ports, brute force an SSH account, this challenge...
 Hak5.org
Hak5.org
Hacking Tools & Media | Hak5 Official Site
Hak5 — industry leading hacker tools & award winning hacking shows for red teams, pentesters, cyber security students and IT professionals. Creators of the WiFi Pineapple, USB Rubber Ducky & more. Home to an inclusive information security community. Established in 2005.

 Infosecurity-magazine.com
Infosecurity-magazine.com
Infosecurity Magazine - Information Security & IT Security News and Resources
Infosecurity Magazine is the award winning online magazine dedicated to the strategy, insight and technology of information security

 Pentestmonkey.net
Pentestmonkey.net
pentestmonkey | Taking the monkey work out of pentesting
mimikatz: Tool To Recover Cleartext Passwords From Lsass December 20, 2011, pentestmonkey I meant to blog about this a while ago, but never got round to it. Here’s a brief post about very cool feature of a tool called mimikatz. I’m very grateful to the tool’s author for bringing it...
 Blackmoreops.com
Blackmoreops.com
Linux, InfoSec, Hacking - blackMORE Ops
blackMORE Ops is the leading source for Kali Linux, InfoSec, Hacking, Network and Cyber Security, How to, Guides and Tutorials with technical details.

 F5.com
F5.com
F5 | Multi-Cloud Security and Application Delivery
F5 application services ensure that applications are always secure and perform the way they should—in any environment and on any device.

 Darknet.org.uk
Darknet.org.uk
Darknet - Hacking Tools, Hacker News & Cyber Security
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.
 Forcepoint.com
Forcepoint.com
Forcepoint | Security Simplified
Forcepoint ONE is security simplified. Get consistent security across any app, device or location and control it from one platform.

 Zsecurity.org
Zsecurity.org
zSecurity – Ethical Hacking Courses, Tutorials, News, Products and more!
Hacking Masterclass by Zaid > Zaid’s NEWEST course. > Exclusive to zSecurity. > Enrol now and get 30% off. More information 745200 Students 1013150 Followers 219 Countries Latest Posts In Hacking & Security Capstone Challenge | Linux Privilege Escalation Linux Privilege Escalation: NFS || Episode 9 DNS Spoofing Basics with...

 Censys.io
Censys.io
Censys | Industry-Leading Cloud and Internet Asset Discovery Solutions
Attack Surface Management and Data Solutions to help your organization discover potential threats, understand cloud-based assets, and help you move fearlessly forward.

 Alertlogic.com
Alertlogic.com
Managed Detection and Response (MDR) Company | Alert Logic
Alert Logic’s Managed Detection and Response platform provides 24/7 protection against constantly evolving cyber attacks. Protect your company now!
Technologies Used by rapid7.com
Dns Records of rapid7.com
A Record: 13.225.214.80 13.225.214.55 13.225.214.100 13.225.214.102AAAA Record:
CNAME Record:
NS Record: ns-439.awsdns-54.com ns-1653.awsdns-14.co.uk ns-1390.awsdns-45.org ns-739.awsdns-28.net
SOA Record: awsdns-hostmaster.amazon.com
MX Record: alt3.aspmx.l.google.com aspmx.l.google.com alt4.aspmx.l.google.com alt1.aspmx.l.google.com alt2.aspmx.l.google.com
SRV Record:
TXT Record: v=spf1 include:rapid7.com._nspf.vali.email include:%{i}._ip.%{h}._ehlo.%{d}._spf.vali.email ~all apple-domain-verification=z0kzoM5HWYKjecj8 MS=ms93061892 amazonses:4oCOQKrYktyI5taxSQqDs8vDW6xIoOAa0QPtofTGSiQ= amazonses:I1RflsrIOXZmVliw6b9cpe6ULmwp07L4w89RB+VpMRI= drift-domain-verification=cbf5da5ed3a2c2c8fbbb7d18daad8055793f8540af697521085ea2c52715003f docker-verification=5d52296d-a09f-4c2f-b8cf-e2334419ff3e drift-domain-verification=9c7f0cdbb7a9b6ebbf802921c978851da16f5826c73f558e990f8fa27cabe1df google-site-verification=7Hz3zw87LNxfKT-hh9IdhIt0s9YTCl00uB0WAf1dF3Y onetrust-domain-verification=29f6404b87c8474b84c7857f6709c560 lf4nplrh94qttd6offtt2seoau atlassian-domain-verification=+Mx+hFjC77glTvA7K9Tp/5x7LvbyawRYOeZpkXhE/Xys/xciI66aaIgyQQAD88E7 lCPZZaaMyCgNvRoUMYSgB/19JKY+JNfGPhaEvDOBAjs= Ha0t0ULKa+E7VLp3KRbhs9smPuzCthPpirN0eMsFBUwGhzSnKIEgNc7sqF5WT9LDZQgaf/4xgX5pFTKNETxbew== miro-verification=9a513c427ef2282157c7f16109d17a5e9eec1fea docusign=65784123-bb76-4570-8d51-94362ff4c391 smartsheet-site-validation.rapid7.com TXT wfJFw8OnJ0WwBCBDP7NuqHHZfZhanWVlikqsWO4VvHOr9QZ0RVR4YnP8dEJ8RoagWSUcN+C5tFWNRq0vvwYUMw== citrix-verification-code=3d0b3642-a1b3-4cf3-8616-c9fb8cd0c2da ZOOM_verify_RZhAVSLBQvCBSQHV-fTGyw amazonses:DnUaWFf5+Slhj2P88CuTkguXyoekjo3Tvof0lhlJxk8= traction-guest=6cc41968-82e9-498d-8bfe-fd5508033f9f abd2ie8ce6rckbs2ssbp9u4742 6qPEVqYoYKApJucUSIQOCzYYTfjkKYG5awZPNAslUIKDQwpzLTczEZUhjrt6pJEfOSFtNgtA7M/YMf4HH7it1g==
DNSKEY Record:
CAA Record: digicert.com digicert.com amazon.com godaddy.com godaddy.com amazon.com letsencrypt.org
Whois Detail of rapid7.com
Domain Name: rapid7.comRegistry Domain ID: 27824595_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.markmonitor.com
Registrar URL: http://www.markmonitor.com
Updated Date: 2021-04-23T09:36:35+0000
Creation Date: 2000-05-25T19:00:54+0000
Registrar Registration Expiration Date: 2023-05-25T07:00:00+0000
Registrar: MarkMonitor, Inc.
Registrar IANA ID: 292
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.2086851750
Domain Status: clientUpdateProhibited (https://www.icann.org/epp#clientUpdateProhibited)
Domain Status: clientTransferProhibited (https://www.icann.org/epp#clientTransferProhibited)
Domain Status: clientDeleteProhibited (https://www.icann.org/epp#clientDeleteProhibited)
Registrant Organization: Rapid7
Registrant State/Province: MA
Registrant Country: US
Registrant Email: Select Request Email Form at https://domains.markmonitor.com/whois/rapid7.com
Admin Organization: Rapid7
Admin State/Province: MA
Admin Country: US
Admin Email: Select Request Email Form at https://domains.markmonitor.com/whois/rapid7.com
Tech Organization: Rapid7
Tech State/Province: MA
Tech Country: US
Tech Email: Select Request Email Form at https://domains.markmonitor.com/whois/rapid7.com
Name Server: ns-739.awsdns-28.net
Name Server: ns-1653.awsdns-14.co.uk
Name Server: ns-439.awsdns-54.com
Name Server: ns-1390.awsdns-45.org
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-06-20T10:29:04+0000 <<<
For more information on WHOIS status codes, please visit:
https://www.icann.org/resources/pages/epp-status-codes
If you wish to contact this domain’s Registrant, Administrative, or Technical
contact, and such email address is not visible above, you may do so via our web
form, pursuant to ICANN’s Temporary Specification. To verify that you are not a
robot, please enter your email address to receive a link to a page that
facilitates email communication with the relevant contact(s).
Web-based WHOIS:
https://domains.markmonitor.com/whois
If you have a legitimate interest in viewing the non-public WHOIS details, send
your request and the reasons for your request to [email protected]
and specify the domain name in the subject line. We will review that request and
may ask for supporting documentation and explanation.
The data in MarkMonitor’s WHOIS database is provided for information purposes,
and to assist persons in obtaining information about or related to a domain
name’s registration record. While MarkMonitor believes the data to be accurate,
the data is provided "as is" with no guarantee or warranties regarding its
accuracy.
By submitting a WHOIS query, you agree that you will use this data only for
lawful purposes and that, under no circumstances will you use this data to:
(1) allow, enable, or otherwise support the transmission by email, telephone,
or facsimile of mass, unsolicited, commercial advertising, or spam; or
(2) enable high volume, automated, or electronic processes that send queries,
data, or email to MarkMonitor (or its systems) or the domain name contacts (or
its systems).
MarkMonitor reserves the right to modify these terms at any time.
By submitting this query, you agree to abide by this policy.
MarkMonitor Domain Management(TM)
Protecting companies and consumers in a digital world.
Visit MarkMonitor at https://www.markmonitor.com
Contact us at +1.8007459229
In Europe, at +44.02032062220

 192.124.249.5
192.124.249.5
 United States
United States
 Valid SSL
Valid SSL