Exploitalert - database of exploits
Exploitalert

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.198898
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 64
Links
ratio 13.449065242274
SSL Details
SSL Issuer:
Issuer: Cloudflare Inc ECC CA-3
Valid From: 2022-06-11 00:00:00
Expiration Date: 2023-06-11 23:59:59
SSL Organization:
Signature b65e6eb2d82edf551a3678e28620ab1a285bdbca
Algorithm: ecdsa-with-SHA256
Found 76 Top Alternative to Exploitalert.com

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.
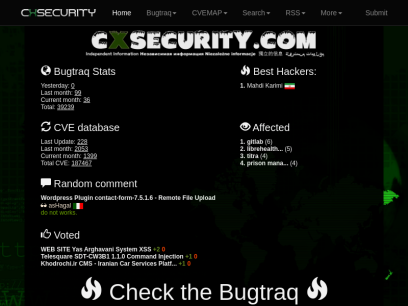
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.
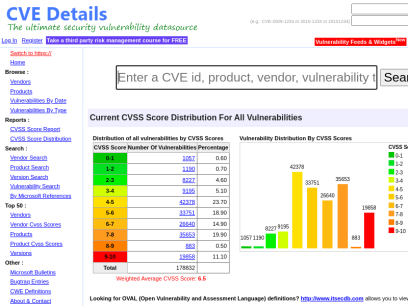
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Vulmon.com
Vulmon.com
Vulmon - Vulnerability Intelligence Search Engine
Vulmon is a vulnerability and exploit search engine with vulnerability intelligence features.

 Phpsecure.info
Phpsecure.info
* phpSecure.info - Welcome .. script, faille, hack, news, developpement, securité, open source php security related articles and vulnerabilities, vulnérabilités, by tobozo , frogman and calimero
PhpSecure.info :: Digging and spreading the latest php applications advisories and vulnerabilities since 2003, also maintaining a selection of articles and tutorials about PHP Security.
 0day.today
0day.today
0day.today Agreement - 0day.today Exploit Database : vulnerability : 0day : new exploits : buy and sell private exploit : shellcode by 0day Today Team
0day Today is the ultimate database of exploits and vulnerabilities and a great resource for vulnerability researchers and security professionals. Our aim is to collect exploits from submittals and various mailing lists and concentrate them in one, easy-to-navigate database. This was written solely for educational purposes. Use it...

 Ripstech.com
Ripstech.com
Clean Code | Developer First | Sonar
Sonar’s industry leading solution enables developers and development teams to write clean code and remediate existing code organically, so they can focus on the work they love and maximize the value they generate for businesses.

 Security-database.com
Security-database.com
Security Database
Security-Database help your corporation foresee and avoid any security risks that may impact your IT infrastructure and business applications.

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers

 Exploitbox.io
Exploitbox.io
ExploitBox.io - A playground & labs For Hackers, 0day Bug Hunters, Pentesters, Security Researchers
A playground & labs For Hackers, 0day Bug Hunters, Pentesters, Vulnerability Researchers & other security folks. Learn, share, pwn.

 Legalhackers.com
Legalhackers.com
Legal/ethical hacking. Information security.
Information Security. Legal / ethical hacking. Independent security research and security advisories.

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.


 Secpod.com
Secpod.com
SecPod: We Prevent Cyberattacks
SecPod is a cyber security technology company. We do everything to prevent attacks on the computing environment. Our products help implement cyber hygiene measures, so attackers have a tough time piercing through.

 Bugsearch.net
Bugsearch.net
Security Alert System - BugSearch.net
BugSearch is an information portal focused on applications security, web oriented and not. We offer our services to disclose our registered users on security alerts found on the net, in order to warn them as soon as possible on bugs, system flaws, exploits and threats afflicting applications and possible patches.

 1337pwn.com
1337pwn.com
1337pwn ⋆
1337pwn provides tutorials on ethical hacking, digital forensics, Kali Linux, Metasploit, WiFi hacking, and FTK Imager.

 Secproject.com
Secproject.com
Soroush Dalili (@irsdl) – سروش دلیلی | Web AppSec ninja, a semicolon enthusiast!
Table of Contents: Introduction 1. Execute command using web.config in the root or an application directory 1.1. Executing web.config as an ASPX page 1.2. Running command using AspNetCoreModule 1.3. Using Machine Key 1.4. Using JSON_AppService.axd 2. Execute command using web.config in a subfolder/virtual directory 2.1. Abusing the compilerOptions attribute 2.1.1....

 Circl.lu
Circl.lu
CIRCL » CIRCL -- Computer Incident Response Center Luxembourg -- CSIRT -- CERT
The Computer Incident Response Center Luxembourg (CIRCL) is a government-driven initiative designed to gather, review, report and respond to computer security threats and incidents. CIRCL is the CERT (Computer Emergency Response Team/Computer Security Incident Response Team) for the private sector, communes and non-governmental entities in Luxembourg.

 Webarxsecurity.com
Webarxsecurity.com
Identify Plugin Vulnerabilities In Your WordPress Sites - Patchstack
Protect websites from plugin vulnerabilities with Patchstack. Be first to receive protection from new security vulnerabilities.
 Extralicense.com
Extralicense.com
Extralicense - Buy, sell trade your licenses.
Extralicense - Buy, sell trade your licenses.



 Zero-day.cz
Zero-day.cz
Free zero-day vulnerability tracking service - zero-day.cz
Free zero-day (0day) vulnerability tracking project.

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.

 F4l13n5n0w.github.io
F4l13n5n0w.github.io
Info Security & Pen Testing learning notes | F4l13n5n0w
This is a description
 Hackingprofessional.github.io
Hackingprofessional.github.io
Aprende Hacking desde 0
Home Blog Principal Aprende Hacking Con Hack The Box Sobre mi
 Flamesec.com
Flamesec.com
flamesec.com is for sale | HugeDomains
Great domain names provide SEO, branding, and a memorable experience for your users. Get a premium domain today.

 Threatpress.com
Threatpress.com
Identify Plugin Vulnerabilities In Your WordPress Sites - Patchstack
Protect websites from plugin vulnerabilities with Patchstack. Be first to receive protection from new security vulnerabilities.

 Hackerhubb.blogspot.com
Hackerhubb.blogspot.com
Hacker Blog - Hackerhub
Stay tuned to our site address for the most up-to-date and new topics about Top Quality Hacker Programs and Hacking Subtopic Areas!

 Geekwire.eu
Geekwire.eu
GeekWire – Information, Cyber, Network Security News
The 5 best security cameras of 2022 25 June 2022 What is the best security camera? ZDNet’s … Tags IT, News SynLapse: Orca Security Publishes Details for Critical Azure Synapse Vulnerability 25 June 2022 In a recent article, Orca Security describes the technical details of SynLapse, a critical Synapse Analytics...
Technologies Used by exploitalert.com
Dns Records of exploitalert.com
A Record: 104.21.44.114 172.67.199.69AAAA Record: 2606:4700:3031::6815:2c72 2606:4700:3037::ac43:c745
CNAME Record:
NS Record: maya.ns.cloudflare.com andy.ns.cloudflare.com
SOA Record: dns.cloudflare.com
MX Record: box.topcodersonline.com
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of exploitalert.com
Domain Name: exploitalert.comRegistry Domain ID: 2041294320_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.godaddy.com
Registrar URL: https://www.godaddy.com
Updated Date: 2021-07-10T11:27:18Z
Creation Date: 2016-07-09T13:07:31Z
Registrar Registration Expiration Date: 2022-07-09T13:07:31Z
Registrar: GoDaddy.com, LLC
Registrar IANA ID: 146
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.4806242505
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: clientUpdateProhibited https://icann.org/epp#clientUpdateProhibited
Domain Status: clientRenewProhibited https://icann.org/epp#clientRenewProhibited
Domain Status: clientDeleteProhibited https://icann.org/epp#clientDeleteProhibited
Registry Registrant ID: Not Available From Registry
Registrant Name: Registration Private
Registrant Organization: Domains By Proxy, LLC
Registrant Street: DomainsByProxy.com
Registrant Street: 2155 E Warner Rd
Registrant City: Tempe
Registrant State/Province: Arizona
Registrant Postal Code: 85284
Registrant Country: US
Registrant Phone: +1.4806242599
Registrant Phone Ext:
Registrant Fax: +1.4806242598
Registrant Fax Ext:
Registrant Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=exploitalert.com
Registry Admin ID: Not Available From Registry
Admin Name: Registration Private
Admin Organization: Domains By Proxy, LLC
Admin Street: DomainsByProxy.com
Admin Street: 2155 E Warner Rd
Admin City: Tempe
Admin State/Province: Arizona
Admin Postal Code: 85284
Admin Country: US
Admin Phone: +1.4806242599
Admin Phone Ext:
Admin Fax: +1.4806242598
Admin Fax Ext:
Admin Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=exploitalert.com
Registry Tech ID: Not Available From Registry
Tech Name: Registration Private
Tech Organization: Domains By Proxy, LLC
Tech Street: DomainsByProxy.com
Tech Street: 2155 E Warner Rd
Tech City: Tempe
Tech State/Province: Arizona
Tech Postal Code: 85284
Tech Country: US
Tech Phone: +1.4806242599
Tech Phone Ext:
Tech Fax: +1.4806242598
Tech Fax Ext:
Tech Email: Select Contact Domain Holder link at https://www.godaddy.com/whois/results.aspx?domain=exploitalert.com
Name Server: ANDY.NS.CLOUDFLARE.COM
Name Server: MAYA.NS.CLOUDFLARE.COM
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-06-21T15:53:06Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
TERMS OF USE: The data contained in this registrar's Whois database, while believed by the
registrar to be reliable, is provided "as is" with no guarantee or warranties regarding its
accuracy. This information is provided for the sole purpose of assisting you in obtaining
information about domain name registration records. Any use of this data for any other purpose
is expressly forbidden without the prior written permission of this registrar. By submitting
an inquiry, you agree to these terms and limitations of warranty. In particular, you agree not
to use this data to allow, enable, or otherwise support the dissemination or collection of this
data, in part or in its entirety, for any purpose, such as transmission by e-mail, telephone,
postal mail, facsimile or other means of mass unsolicited, commercial advertising or solicitations
of any kind, including spam. You further agree not to use this data to enable high volume, automated
or robotic electronic processes designed to collect or compile this data for any purpose, including
mining this data for your own personal or commercial purposes. Failure to comply with these terms
may result in termination of access to the Whois database. These terms may be subject to modification
at any time without notice.
 51.159.77.238
51.159.77.238
 United States
United States
 Valid SSL
Valid SSL