Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time: 0.369262
SSL: Enable
Status: up
Code To Txt Ratio
Word Count
Links 0
ratio 9.5652173913043
SSL Details
SSL Issuer:
Issuer: R3
Valid From: 2022-05-11 07:44:36
Expiration Date: 2022-08-09 07:44:35
SSL Organization:
Signature 7f7b9bffedb6a7b831c79b12b24eff9c1db92332
Algorithm: RSA-SHA256
Found 49 Top Alternative to Securiteam.com

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers
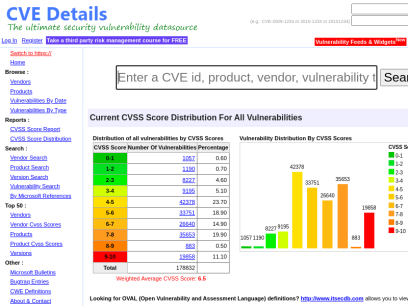
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time
 0day.today
0day.today
0day.today Agreement - 0day.today Exploit Database : vulnerability : 0day : new exploits : buy and sell private exploit : shellcode by 0day Today Team
0day Today is the ultimate database of exploits and vulnerabilities and a great resource for vulnerability researchers and security professionals. Our aim is to collect exploits from submittals and various mailing lists and concentrate them in one, easy-to-navigate database. This was written solely for educational purposes. Use it...

 Vulmon.com
Vulmon.com
Vulmon - Vulnerability Intelligence Search Engine
Vulmon is a vulnerability and exploit search engine with vulnerability intelligence features.
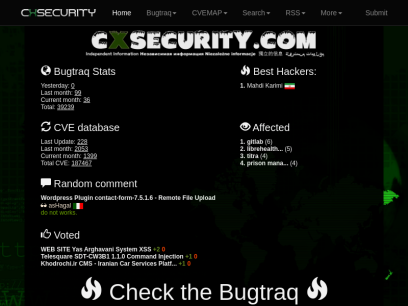
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.



 Fortiguard.com
Fortiguard.com
FortiGuard
View by Product Network Intrusion Protection Anti-Recon and Anti-Exploit Secure DNS IP Reputation/Anti-Botnet Indicators of Compromise IP Geolocation Service Cloud Workload Security Service Content and Endpoint Endpoint Detection & Response Anti-Virus Endpoint Vulnerability Device Detection ANN and NDR Sandbox Behavior Engine Application Web Filtering Anti-Spam Application Control Industrial Security Services...

 Security-database.com
Security-database.com
Security Database
Security-Database help your corporation foresee and avoid any security risks that may impact your IT infrastructure and business applications.

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.

 Circl.lu
Circl.lu
CIRCL » CIRCL -- Computer Incident Response Center Luxembourg -- CSIRT -- CERT
The Computer Incident Response Center Luxembourg (CIRCL) is a government-driven initiative designed to gather, review, report and respond to computer security threats and incidents. CIRCL is the CERT (Computer Emergency Response Team/Computer Security Incident Response Team) for the private sector, communes and non-governmental entities in Luxembourg.

 Seclists.org
Seclists.org
SecLists.Org Security Mailing List Archive
Security mailing list archive for the Nmap lists, Bugtraq, Full Disclosure, Security Basics, Pen-test, and dozens more. Search capabilities and RSS feeds with smart excerpts are available

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.
 Securityidiots.com
Securityidiots.com
Welcome to Security Idiots!!
Security Idiots is a place where some insane idiots try thier hands on with Security.

 Ripstech.com
Ripstech.com
Clean Code | Developer First | Sonar
Sonar’s industry leading solution enables developers and development teams to write clean code and remediate existing code organically, so they can focus on the work they love and maximize the value they generate for businesses.

 Webappsec.org
Webappsec.org
Home - Web Application Security Consortium
Interested in application security and want to help? For starters consider subscribing to The Web Security Mailing List the most popular application security related mailing list on the web. You can also help us by contributing to one of the projects below. Simply go to the project you wish to...

 Pentestmonkey.net
Pentestmonkey.net
pentestmonkey | Taking the monkey work out of pentesting
mimikatz: Tool To Recover Cleartext Passwords From Lsass December 20, 2011, pentestmonkey I meant to blog about this a while ago, but never got round to it. Here’s a brief post about very cool feature of a tool called mimikatz. I’m very grateful to the tool’s author for bringing it...

 Packetstormsecurity.net
Packetstormsecurity.net
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers

 Ixiacom.com
Ixiacom.com
Network Visibility and Network Test Products | Keysight
Use Ixia (Keysight) market-leading network test, visibility, performance monitoring, and security solutions to build and manage more secure, and reliable networks.
 Sectools.org
Sectools.org
SecTools.Org Top Network Security Tools
Rankings and reviews of computer and network security software, programs, and tools.

 Giac.org
Giac.org
Cyber Security Certifications | GIAC Certifications
GIAC Certifications develops and administers premier, professional information security certifications. More than 30 certifications align with SANS training and ensure mastery in critical, specialized InfoSec domains. GIAC certifications provide the highest and most rigorous assurance of cyber security knowledge and skill available to industry, government, and military clients across the world.

 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies

 Snort.org
Snort.org
Snort - Network Intrusion Detection & Prevention System
Snort is an open-source, free and lightweight network intrusion detection system (NIDS) software for Linux and Windows to detect emerging threats.

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Coresecurity.com
Coresecurity.com
Core Security | Cyber Threat Prevention & Identity Governance
Contact Us Support All HelpSystems Products FREE TRIALS Contact Us Support All HelpSystems Products FREE TRIALS Cyber Threat Toggle Dropdown Products Core Impact Penetration testing software Cobalt Strike Red team software Event Manager Security information and event management Network Insight Network Traffic Analysis Powertech Antivirus Server-level virus protection Security Auditor...

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Darknet.org.uk
Darknet.org.uk
Darknet - Hacking Tools, Hacker News & Cyber Security
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.

 Legalhackers.com
Legalhackers.com
Legal/ethical hacking. Information security.
Information Security. Legal / ethical hacking. Independent security research and security advisories.
Technologies Used by securiteam.com
Dns Records of securiteam.com
A Record: 52.25.189.91AAAA Record:
CNAME Record:
NS Record: ns-1334.awsdns-38.org ns-711.awsdns-24.net ns-329.awsdns-41.com ns-1821.awsdns-35.co.uk
SOA Record: awsdns-hostmaster.amazon.com
MX Record: securiteam.com
SRV Record:
TXT Record: v=spf1 ip4:81.218.22.242 ip4:212.150.194.226 a mx a:blogs.securiteam.com a:beyondsecurity.com mx:securiteam.com ?all
DNSKEY Record:
CAA Record:
Whois Detail of securiteam.com
Domain Name: securiteam.comRegistry Domain ID: 3139238_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.registrar.amazon.com
Registrar URL: https://registrar.amazon.com
Updated Date: 2022-05-29T21:29:33.828Z
Creation Date: 1998-07-03T04:00:00Z
Registrar Registration Expiration Date: 2023-07-02T04:00:00Z
Registrar: Amazon Registrar, Inc.
Registrar IANA ID: 468
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.2067406200
Reseller:
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: transferPeriod https://icann.org/epp#transferPeriod
Registry Registrant ID:
Registrant Name: On behalf of securiteam.com owner
Registrant Organization: Whois Privacy Service
Registrant Street: P.O. Box 81226
Registrant City: Seattle
Registrant State/Province: WA
Registrant Postal Code: 98108-1226
Registrant Country: US
Registrant Phone: +1.2065771368
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: On behalf of securiteam.com administrative contact
Admin Organization: Whois Privacy Service
Admin Street: P.O. Box 81226
Admin City: Seattle
Admin State/Province: WA
Admin Postal Code: 98108-1226
Admin Country: US
Admin Phone: +1.2065771368
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID:
Tech Name: On behalf of securiteam.com technical contact
Tech Organization: Whois Privacy Service
Tech Street: P.O. Box 81226
Tech City: Seattle
Tech State/Province: WA
Tech Postal Code: 98108-1226
Tech Country: US
Tech Phone: +1.2065771368
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email: [email protected]
Name Server: ns-1201.awsdns-22.org
Name Server: ns-1663.awsdns-15.co.uk
Name Server: ns-212.awsdns-26.com
Name Server: ns-805.awsdns-36.net
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-05-29T21:29:34.458Z <<<
For more information on Whois status codes, please visit https://www.icann.org/resources/pages/epp
By submitting a query to the Amazon Registrar, Inc. WHOIS database, you agree to abide by the following terms. The data in Amazon Registrar, Inc.'s WHOIS database is provided by Amazon Registrar, Inc. for the sole purpose of assisting you in obtaining information about domain name accuracy. You agree to use this data only for lawful purposes and further agree not to use this data for any unlawful purpose or to: (1) enable, allow, or otherwise support the transmission by email, telephone, or facsimile of commercial advertising or unsolicited bulk email, or (2) enable high volume, automated, electronic processes to collect or compile this data for any purpose, including mining this data for your own personal or commercial purposes. Amazon Registrar, Inc. reserves the right to restrict or terminate your access to the data if you fail to abide by these terms of use. Amazon Registrar, Inc. reserves the right to modify these terms at any time.
Visit Amazon Registrar, Inc. at https://registrar.amazon.com
Contact information available here: https://docs.aws.amazon.com/Route53/latest/DeveloperGuide/domain-contact-support.html
© 2022, Amazon.com, Inc., or its affiliates

 United States
United States
 InValid
SSL
InValid
SSL