Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.333362
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 284
Links
ratio 17.751479289941
SSL Details
SSL Issuer:
Issuer: R3
Valid From: 2022-04-27 15:20:53
Expiration Date: 2022-07-26 15:20:52
SSL Organization:
Signature d6d7eecd6a803b098cb7dfb0ae95320f141c85bb
Algorithm: RSA-SHA256
Found 76 Top Alternative to Cybersecurity-help.cz
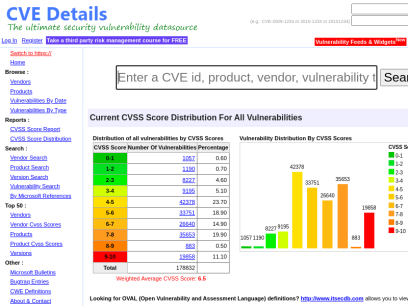
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time


 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers
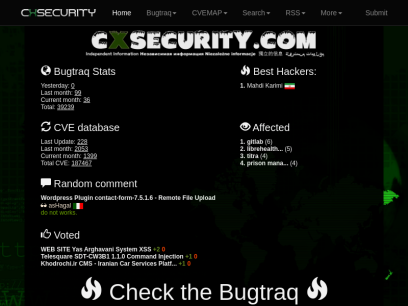
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.


 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Netsparker.com
Netsparker.com
Invicti | Web Application Security For Enterprise
Get accurate, automated application security testing that scales like no other solution. Secure 1000s of web assets with less manual effort. Reduce your risk with the only…

 Censys.io
Censys.io
Censys | Industry-Leading Cloud and Internet Asset Discovery Solutions
Attack Surface Management and Data Solutions to help your organization discover potential threats, understand cloud-based assets, and help you move fearlessly forward.
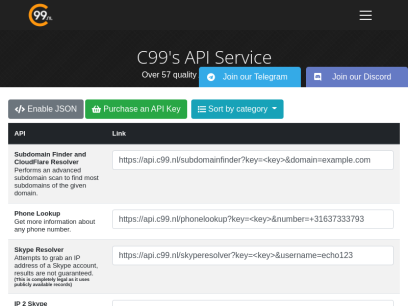
 C99.nl
C99.nl
C99 Free API's - C99's API Service
We provide Skype Resolver API, Weather API, Cheap API, Email2Skype, IP2Skype, Skype2Email, Skype bot source and much more...

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.

 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.

 Hacker101.com
Hacker101.com
Home | Hacker101
Hacker101 is a free class for web security. Whether you’re a programmer with an interest in bug bounties or a seasoned security professional, Hacker101 has something to teach you.

 Vulmon.com
Vulmon.com
Vulmon - Vulnerability Intelligence Search Engine
Vulmon is a vulnerability and exploit search engine with vulnerability intelligence features.

 Dnsdumpster.com
Dnsdumpster.com
DNSdumpster.com - dns recon and research, find and lookup dns records
Find dns records in order to identify the Internet footprint of an organization. Recon that enables deeper security assessments and discovery of the attack surface.
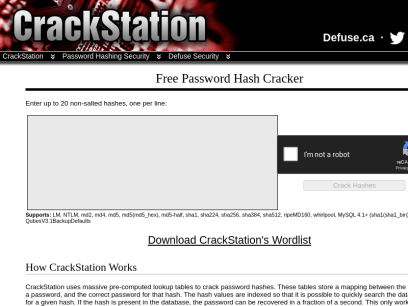
 Crackstation.net
Crackstation.net
CrackStation - Online Password Hash Cracking - MD5, SHA1, Linux, Rainbow Tables, etc.
Crackstation is the most effective hash cracking service. We crack: MD5, SHA1, SHA2, WPA, and much more...
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.
 Hackertarget.com
Hackertarget.com
28 Online Vulnerability Scanners & Network Tools | HackerTarget.com
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.
 Snyk.io
Snyk.io
Snyk | Developer security | Develop fast. Stay secure.
Snyk helps software-driven businesses develop fast and stay secure. Continuously find and fix vulnerabilities for npm, Maven, NuGet, RubyGems, PyPI and more.

 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Security-database.com
Security-database.com
Security Database
Security-Database help your corporation foresee and avoid any security risks that may impact your IT infrastructure and business applications.

 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.

 Webarxsecurity.com
Webarxsecurity.com
Identify Plugin Vulnerabilities In Your WordPress Sites - Patchstack
Protect websites from plugin vulnerabilities with Patchstack. Be first to receive protection from new security vulnerabilities.

 Md5decrypt.net
Md5decrypt.net
Md5 Decryption & Encryption Gratuite - Plus de 15.000.000.000 hashs
Decryption Md5 : Le Md5 (Message Digest 5) est une fonction cryptographique qui permet de "hasher" (encrypter) une séquence numérique en un hash md5 de 128 bits, soit 32 caractères, et ce peu importe la longueur de la séquence originale. Ce système cryptographique est irréversible, il n'est pas possible d'obtenir...
 Viewdns.info
Viewdns.info
ViewDNS.info - Your one source for DNS related tools!
Reverse IP Lookup Find all sites hosted on a given server. Domain / IP Reverse Whois Lookup Find domain names owned by an individual or company. Registrant Name or Email Address IP History Show historical IP addresses for a domain. Domain (e.g. domain.com) DNS Report Provides a complete report on...

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.

 Fortiguard.com
Fortiguard.com
FortiGuard
View by Product Network Intrusion Protection Anti-Recon and Anti-Exploit Secure DNS IP Reputation/Anti-Botnet Indicators of Compromise IP Geolocation Service Cloud Workload Security Service Content and Endpoint Endpoint Detection & Response Anti-Virus Endpoint Vulnerability Device Detection ANN and NDR Sandbox Behavior Engine Application Web Filtering Anti-Spam Application Control Industrial Security Services...

 Kali.org
Kali.org
Kali Linux | Penetration Testing and Ethical Hacking Linux Distribution
Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking and network security assessments.
 Md5online.org
Md5online.org
MD5 Online | Free and fast MD5 encryption
MD5Online offers a free and fast tool to generate an MD5 hash from a word of your choice


 Nintechnet.com
Nintechnet.com
NinTechNet: The Ninja Technologies Network
Your Website's Security is Our Priority. We offer a range of security products and services to help you protect your website and keep it up and running.

 Threatpress.com
Threatpress.com
Identify Plugin Vulnerabilities In Your WordPress Sites - Patchstack
Protect websites from plugin vulnerabilities with Patchstack. Be first to receive protection from new security vulnerabilities.

 Cyware.com
Cyware.com
Threat Intelligence Solution Company | Cyber Security Products | Cyber Security Operations Center | Cyware
Cyber Security Products - Cyware offers innovative, real-time cyber fusion solutions for Strategic and Tactical Threat Intelligence Sharing, Threat Response and Security Automation. Get a Demo Now!

 Ripstech.com
Ripstech.com
Clean Code | Developer First | Sonar
Sonar’s industry leading solution enables developers and development teams to write clean code and remediate existing code organically, so they can focus on the work they love and maximize the value they generate for businesses.

 Wpdownloadfree.com
Wpdownloadfree.com
Download Wordpress Themes & Plugins Free【2022】✅
Wordpress Themes and Plugins: If you don't know what are best plugins and themes for your website, this is your place. We will publish all things you need for

 Securityweek.com
Securityweek.com
Cybersecurity News, Insights and Analysis | SecurityWeek
SecurityWeek provides cybersecurity news and information to global enterprises, with expert insights and analysis for IT security professionals.

 Latesthackingnews.com
Latesthackingnews.com
Latest Hacking News - We offer the latest hacking news and cyber security courses for ethical hackers, penetration testers, IT security experts and essentially anyone with hacker interests.
We offer the latest hacking news and cyber security courses for ethical hackers, penetration testers, IT security experts and essentially anyone with hacker interests.

 Securityaffairs.co
Securityaffairs.co
Security Affairs - Read, think, share … Security is everyone's responsibilitySecurity Affairs
Security Affairs - Every security issue is our affair. Read, think, share … Security is everyone's responsibility

 Circl.lu
Circl.lu
CIRCL » CIRCL -- Computer Incident Response Center Luxembourg -- CSIRT -- CERT
The Computer Incident Response Center Luxembourg (CIRCL) is a government-driven initiative designed to gather, review, report and respond to computer security threats and incidents. CIRCL is the CERT (Computer Emergency Response Team/Computer Security Incident Response Team) for the private sector, communes and non-governmental entities in Luxembourg.

 Alertlogic.com
Alertlogic.com
Managed Detection and Response (MDR) Company | Alert Logic
Alert Logic’s Managed Detection and Response platform provides 24/7 protection against constantly evolving cyber attacks. Protect your company now!

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.

 Cisecurity.org
Cisecurity.org
CIS Center for Internet Security
CIS is a forward-thinking nonprofit that harnesses the power of a global IT community to safeguard public and private organizations against cyber threats.
 0day.today
0day.today
0day.today Agreement - 0day.today Exploit Database : vulnerability : 0day : new exploits : buy and sell private exploit : shellcode by 0day Today Team
0day Today is the ultimate database of exploits and vulnerabilities and a great resource for vulnerability researchers and security professionals. Our aim is to collect exploits from submittals and various mailing lists and concentrate them in one, easy-to-navigate database. This was written solely for educational purposes. Use it...


 Cisa.gov
Cisa.gov
Homepage | CISA
CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.

 Hostpress.de
Hostpress.de
WordPress Hosting » Schnell & sicher mit » HostPress
Wir haben für jeden Anwendungsfall das passende WordPress Webhosting.Deine bestehende Webseite ziehen wir kostenlos zu uns um.
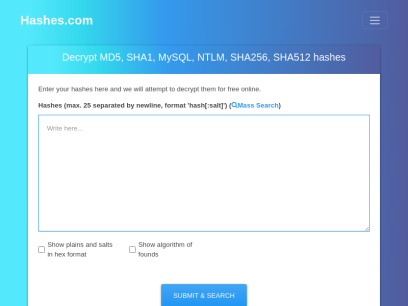
 Hashes.com
Hashes.com
Decrypt MD5, SHA1, MySQL, NTLM, SHA256, SHA512, Wordpress, Bcrypt hashes for free online
Decrypt and crack your MD5, SHA1, SHA256, MySQL, and NTLM hashes for free online. We also support Bcrypt, SHA512, Wordpress and many more.
Technologies Used by cybersecurity-help.cz
Dns Records of cybersecurity-help.cz
A Record: 51.159.77.238AAAA Record:
CNAME Record:
NS Record: pid1.srv53.net pid2.srv53.org
SOA Record: support.dnshosting.org
MX Record: cybersecurityhelp-cz03c.mail.protection.outlook.com
SRV Record:
TXT Record: MS=ms40682220 v=spf1 include:spf.protection.outlook.com +a -all google-site-verification=JbCmqDZTV3HIRwlsYzhfp0E4enSHKqLLGvwkEoQ-lxs
DNSKEY Record:
CAA Record:
Whois Detail of cybersecurity-help.cz
% (c) 2006-2021 CZ.NIC, z.s.p.o.%
% Intended use of supplied data and information
%
% Data contained in the domain name register, as well as information
% supplied through public information services of CZ.NIC association,
% are appointed only for purposes connected with Internet network
% administration and operation, or for the purpose of legal or other
% similar proceedings, in process as regards a matter connected
% particularly with holding and using a concrete domain name.
%
% Full text available at:
% http://www.nic.cz/page/306/intended-use-of-supplied-data-and-information/
%
% See also a search service at http://www.nic.cz/whois/
%
%
% Whoisd Server Version: 3.12.2
% Timestamp: Tue Jun 21 16:02:03 2022
domain: cybersecurity-help.cz
registrant: ZONER-20121126958
nsset: DNS53
registrar: REG-ZONER
registered: 30.07.2015 12:16:53
expire: 30.07.2022
contact: ZONER-20121126958
org: IMENA.UA
name: Vyacheslav Krukovskiy
address: Gaidara st., 50
address: KYIV
address: 01033
address: UA
e-mail: [email protected]
registrar: REG-ZONER
created: 26.11.2012 09:58:04
changed: 04.08.2020 10:47:39
nsset: DNS53
nserver: pid1.srv53.net
nserver: pid2.srv53.org
tech-c: IMENA.UA
registrar: REG-ZONER
created: 27.01.2015 13:37:04
contact: IMENA.UA
org: IMENA.UA
name: Imena.ua Hostmaster
address: 111/113 Velyka Vasylkivska
address: Kyiv
address: 03150
address: UA
registrar: REG-ZONER
created: 26.12.2007 18:21:09
changed: 15.05.2018 21:32:00
 104.18.23.245
104.18.23.245
 United States
United States
 Valid SSL
Valid SSL