Vulners - Vulnerability DataBase
Vulners - Vulnerability DataBase

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.070997
SSL: Enable
Status: up
Code To Txt Ratio
Word Count
Links 0
ratio 1.3845578146439
SSL Details
SSL Issuer:
Issuer: Sectigo RSA Domain Validation Secure Server CA
Valid From: 2021-06-28 00:00:00
Expiration Date: 2022-07-08 23:59:59
SSL Organization:
Signature 39f497dd5232111c4482b47bc3ea959b0b5512e4
Algorithm: RSA-SHA256
Found 74 Top Alternative to Vulners.com
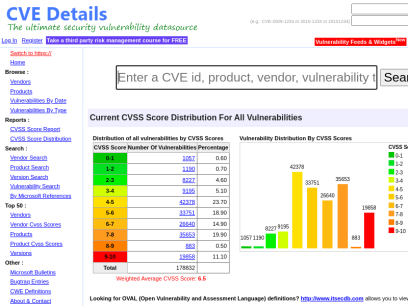
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers

 Onlinehashcrack.com
Onlinehashcrack.com
Online Password Hash Crack - MD5 NTLM Wordpress Joomla WPA PMKID, Office, iTunes, Archive, ..
OnlineHashCrack is a powerful hash cracking and recovery online service for MD5 NTLM Wordpress Joomla SHA1 MySQL OSX WPA, PMKID, Office Docs, Archives, PDF, iTunes and more!

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.

 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!

 Netsparker.com
Netsparker.com
Invicti | Web Application Security For Enterprise
Get accurate, automated application security testing that scales like no other solution. Secure 1000s of web assets with less manual effort. Reduce your risk with the only…

 Vulmon.com
Vulmon.com
Vulmon - Vulnerability Intelligence Search Engine
Vulmon is a vulnerability and exploit search engine with vulnerability intelligence features.
 Hackertarget.com
Hackertarget.com
28 Online Vulnerability Scanners & Network Tools | HackerTarget.com
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.

 Circl.lu
Circl.lu
CIRCL » CIRCL -- Computer Incident Response Center Luxembourg -- CSIRT -- CERT
The Computer Incident Response Center Luxembourg (CIRCL) is a government-driven initiative designed to gather, review, report and respond to computer security threats and incidents. CIRCL is the CERT (Computer Emergency Response Team/Computer Security Incident Response Team) for the private sector, communes and non-governmental entities in Luxembourg.

 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.

 Seclists.org
Seclists.org
SecLists.Org Security Mailing List Archive
Security mailing list archive for the Nmap lists, Bugtraq, Full Disclosure, Security Basics, Pen-test, and dozens more. Search capabilities and RSS feeds with smart excerpts are available
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Kali.org
Kali.org
Kali Linux | Penetration Testing and Ethical Hacking Linux Distribution
Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking and network security assessments.

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.
 0day.today
0day.today
0day.today Agreement - 0day.today Exploit Database : vulnerability : 0day : new exploits : buy and sell private exploit : shellcode by 0day Today Team
0day Today is the ultimate database of exploits and vulnerabilities and a great resource for vulnerability researchers and security professionals. Our aim is to collect exploits from submittals and various mailing lists and concentrate them in one, easy-to-navigate database. This was written solely for educational purposes. Use it...
 Hacking.land
Hacking.land
Hacking Land - Hack, Crack and Pentest
¿Recuerdan cuándo todo se hackeaba con Telnet y una IP? Pues bueno, hoy no...
 Kitploit.com
Kitploit.com
KitPloit - PenTest & Hacking Tools
Leading source of security tools, hacking tools, cybersecurity and network security. Learn about new tools and updates in one place.

 Securityonline.info
Securityonline.info
Penetration Testing • Information Security
Securityonline is a huge security community. It is committed to the sharing of high-quality technical articles and safety reports, focusing on high-quality security and security incidents in the industry.

 Security-database.com
Security-database.com
Security Database
Security-Database help your corporation foresee and avoid any security risks that may impact your IT infrastructure and business applications.

 Fortiguard.com
Fortiguard.com
FortiGuard
View by Product Network Intrusion Protection Anti-Recon and Anti-Exploit Secure DNS IP Reputation/Anti-Botnet Indicators of Compromise IP Geolocation Service Cloud Workload Security Service Content and Endpoint Endpoint Detection & Response Anti-Virus Endpoint Vulnerability Device Detection ANN and NDR Sandbox Behavior Engine Application Web Filtering Anti-Spam Application Control Industrial Security Services...

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.

 Coresecurity.com
Coresecurity.com
Core Security | Cyber Threat Prevention & Identity Governance
Contact Us Support All HelpSystems Products FREE TRIALS Contact Us Support All HelpSystems Products FREE TRIALS Cyber Threat Toggle Dropdown Products Core Impact Penetration testing software Cobalt Strike Red team software Event Manager Security information and event management Network Insight Network Traffic Analysis Powertech Antivirus Server-level virus protection Security Auditor...

 Openvas.org
Openvas.org
OpenVAS - Open Vulnerability Assessment Scanner
Greenbone OpenVAS OpenVAS is a full-featured vulnerability scanner. Its capabilities include unauthenticated and authenticated testing, various high-level and low-level internet and industrial protocols, performance tuning for large-scale scans and a powerful internal programming language to implement any type of vulnerability test. The scanner obtains the tests for detecting vulnerabilities from...

 Qualys.com
Qualys.com
Information Security and Compliance | Qualys
Qualys, Inc. helps your business automate the full spectrum of auditing, compliance and protection of your IT systems and web applications.

 Snort.org
Snort.org
Snort - Network Intrusion Detection & Prevention System
Snort is an open-source, free and lightweight network intrusion detection system (NIDS) software for Linux and Windows to detect emerging threats.
 Rpmfind.net
Rpmfind.net
Rpmfind mirror
This server is located in Lyon, within the Creatis laboratory. Like other rpmfind mirrors, this machine is using a large amount of bandwidth, and credits go to the CISR, Centre Inter-Etablissement pour les Services Reseau, for providing this connectivity.

 Us-cert.gov
Us-cert.gov
Homepage | CISA
As part of its mission, CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.
 Prodefence.org
Prodefence.org
Prodefence - Cyber Security Services | Malware & Pentesting
Cyber security services - Malware analysis - Penetration testing - Data protection

 Lwn.net
Lwn.net
Welcome to LWN.net [LWN.net]
[$] Support for Intel's Linear Address Masking [Kernel] Posted Jul 25, 2022 14:23 UTC (Mon) by corbet A 64-bit pointer can address a lot of memory — far more than just about any application could ever need. As a result, there are bits within that pointer that are not really...

 Threatpost.com
Threatpost.com
Threatpost | The first stop for security news
Threatpost, is an independent news site which is a leading source of information about IT and business security for hundreds of thousands of professionals worldwide.

 Securityaffairs.co
Securityaffairs.co
Security Affairs - Read, think, share … Security is everyone's responsibilitySecurity Affairs
Security Affairs - Every security issue is our affair. Read, think, share … Security is everyone's responsibility

 Any.run
Any.run
ANY.RUN - Interactive Online Malware Sandbox
Cloud-based malware analysis service. Take your information security to the next level. Analyze suspicious and malicious activities using our innovative tools.


 Securitynewspaper.com
Securitynewspaper.com
Information Security News|Cyber Security|Hacking Tutorial
Information Security Newspaper covers cyber security news, data breaches, malware, hacking, vulnerabilities, mobile security & ethical hacking tutorials
 Kalilinuxtutorials.com
Kalilinuxtutorials.com
Kali Linux Tutorials - A Single Stop for Kali Linux Tools
Kali Linux tutorials is an independent platform that covers step by tutorials, advanced penetration testing, Ethical Hacking and network security tools.

 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies


 Pentester.land
Pentester.land
Pentester Land · Offensive Infosec
The newsletter is dead, long live the newsletter! 12 Jul 2020 • newsletter This is a long due post. Since The 5 Hacking Newsletter has stopped on this blog, I’ve been getting many questions about it. So, even though most readers already know by now, here’s a summary of what...

 Talosintelligence.com
Talosintelligence.com
Cisco Talos Intelligence Group - Comprehensive Threat Intelligence
Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further harm the internet at large.

 Cisa.gov
Cisa.gov
Homepage | CISA
CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.

 Pentesttools.net
Pentesttools.net
PentestTools - Penetration Testing Tools.
Latest Penetration Testing Tools. Cyber Security and Technology News. High Quality Penetration Testing Videos.
 Hacking.reviews
Hacking.reviews
Hacking Reviews
Leading source of Hacking News, Information Security, Cyber Security, and Network Security.

 Hashes.com
Hashes.com
Decrypt MD5, SHA1, MySQL, NTLM, SHA256, SHA512, Wordpress, Bcrypt hashes for free online
Decrypt and crack your MD5, SHA1, SHA256, MySQL, and NTLM hashes for free online. We also support Bcrypt, SHA512, Wordpress and many more.
Technologies Used by vulners.com
Dns Records of vulners.com
A Record: 185.104.208.93AAAA Record:
CNAME Record:
NS Record: ernest.ns.cloudflare.com audrey.ns.cloudflare.com
SOA Record: dns.cloudflare.com
MX Record: vulners-com.mail.protection.outlook.com
SRV Record:
TXT Record: MS=ms35443267 v=spf1 include:mail.zendesk.com include:_spf.yandex.net include:spf.protection.outlook.com ip4:23.111.95.52 ip4:23.111.95.60 ~all
DNSKEY Record:
CAA Record:
Whois Detail of vulners.com
Domain Name: VULNERS.COMRegistry Domain ID: 1944193906_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.nic.ru
Registrar URL: http://www.nic.ru
Updated Date: 2022-06-18T06:45:29Z
Creation Date: 2015-07-03T07:13:21Z
Registrar Registration Expiration Date: 2022-07-02T21:00:00Z
Registrar: Regional Network Information Center, JSC dba RU-CENTER
Registrar IANA ID: 463
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +7.4959944601
Registry Registrant ID:
Registrant Name: Privacy protection service - whoisproxy.ru
Registrant Organization: Privacy protection service - whoisproxy.ru
Registrant Street: PO box 99, whoisproxy.ru
Registrant City: Moscow
Registrant State/Province: Moscow
Registrant Postal Code: 123308
Registrant Country: RU
Registrant Phone: +7.4957856536
Registrant Phone Ext:
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: Privacy protection service - whoisproxy.ru
Admin Organization: Privacy protection service - whoisproxy.ru
Admin Street: PO box 99, whoisproxy.ru
Admin City: Moscow
Admin State/Province: Moscow
Admin Postal Code: 123308
Admin Country: RU
Admin Phone: +7.4957856536
Admin Phone Ext:
Admin Email: [email protected]
Registry Tech ID:
Tech Name: Privacy protection service - whoisproxy.ru
Tech Organization: Privacy protection service - whoisproxy.ru
Tech Street: PO box 99, whoisproxy.ru
Tech City: Moscow
Tech State/Province: Moscow
Tech Postal Code: 123308
Tech Country: RU
Tech Phone: +7.4957856536
Tech Phone Ext:
Tech Email: [email protected]
Name Server: audrey.ns.cloudflare.com
Name Server: ernest.ns.cloudflare.com
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
For more information on Whois status codes, please visit: https://icann.org/epp
>>> Last update of WHOIS database: 2022.06.21T18:54:28Z <<<
 192.124.249.13
192.124.249.13
 United States
United States
 Valid SSL
Valid SSL