aldeid
Pentesting   •    Web Exploitation   •    Cryptography   •    Forensics   •    Reversing   •    Binary Exploitation   •    CTF   •    Threat Hunting TryHackMe > Unbaked Pie Sun, 6 Jun 2021 11:34:00 +0000 Enumerate a Django application, find a vulnerability, exploit a pickle session cookie, evade a docker environment, find a way to forward ports, brute force an SSH account, this challenge...
Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.16691
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 426
Links
ratio 14.808355764492
SSL Details
SSL Issuer:
Issuer: Cloudflare Inc ECC CA-3
Valid From: 2022-05-17 00:00:00
Expiration Date: 2023-05-17 23:59:59
SSL Organization:
Signature 6e4c061a394bfb179c6e5065ae7dcd5d9a694d7f
Algorithm: ecdsa-with-SHA256
Found 74 Top Alternative to Aldeid.com

 Tryhackme.com
Tryhackme.com
TryHackMe | Cyber Security Training
TryHackMe is a free online platform for learning cyber security, using hands-on exercises and labs, all through your browser!


 Installlion.com
Installlion.com
Simply Install/Uninstall Linux Software - Install Lion
Simply Install/Uninstall Linux Software Clear, easy, instructions on how to install and uninstall software on Ubuntu or Debian.Click a single button to copy instructions to your clipboard and then paste them straight to the command line. If you find your package manager cumbersome and you just want to use apt-get...

 Tripod.com
Tripod.com
Build a Free Website with Web Hosting | Tripod
Build a free website with our easy to use, free website builder. Find web hosting, domain registration, email and more at Tripod.com.

 C-jump.com
C-jump.com
c-jump: computer programming board game
c-jump ski race board game helps children to learn programming languages C++ and Java.

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Hackthissite.org
Hackthissite.org
Hack This Site
HackThisSite.org is a free, safe and legal training ground for hackers to test and expand their ethical hacking skills with challenges, CTFs, and more.

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.

 Unixwiz.net
Unixwiz.net
Steve Friedl's Home Page
System administration, software development, file conversions, and security for the Payroll Service Bureau industry: Evolution (exhaustive experience) iSolved (extensive experience) Kronos (minor experience) Execupay (slight experience) PowerShell cmdlet development (in C#); see my Cmdletters for tips on building these yourself. C, C++, and C# systems software development on the UNIX...

 Darknet.org.uk
Darknet.org.uk
Darknet - Hacking Tools, Hacker News & Cyber Security
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.
 Amitghosh.net
Amitghosh.net
Amit Ghosh
Amit Ghosh is an entrepreneur and avid blogger who loves idea jamming to develop creative solutions for problems.

 Secjuice.com
Secjuice.com
Secjuice | Non-Profit Cyber Goodness
The only non-profit, independent & volunteer based publication in the information security industry. Cybersecurity articles written by hackers.

 Sysinternals.com
Sysinternals.com
Sysinternals - Windows Sysinternals | Microsoft Docs
Library, learning resources, downloads, support, and community. Evaluate and find out how to install, deploy, and maintain Windows with Sysinternals utilities.
 Tuts4you.com
Tuts4you.com
Tuts 4 You
A community for researchers and reverse engineers interested in the field of Reverse Code Engineering (RCE).
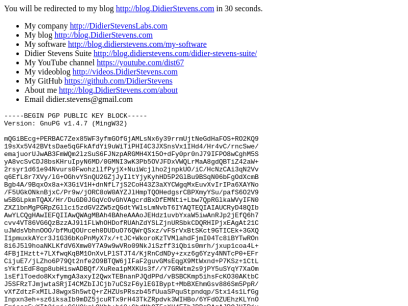
 Didierstevens.com
Didierstevens.com
Didier Stevens
-----BEGIN PGP PUBLIC KEY BLOCK----- Version: GnuPG v1.4.7 (MingW32) mQGiBEcg+PERBAC7Zex85WF3yfmGOfGjAMLsNx6y39rrmUjtNeGdHaFOS+RO2KQ9 19sXx5V42BVtsDae5qGFkAfdYi9uWiTiPHI4C3JXSnsVx1IHd4/Hr4vC/rncSwe/ emajuorUJwAB3FmWQm2lzSuS6FJNzpARGMH4X15O+dFy0pr0nJ79IFPO8wCghM5S yA8vcSvCDJ8bsKHruIpyN6MD/0GMNI3wK3Pb5OVJFDxVWQLrMaA8gdQBTiZ42aW+ 2rsyr1d61e94Nvurs0FwohzllfPyjX+NuiWcjlho2jnpkUO/iC/HcNzCAi3qN2Vv q6EfL8r7XVy/lG+OGhvYSnQU2GZjJyIltYjyKyhHD5P2GlBu9BSqN06bFgOdXcmB Bgb4A/9BqxOx8a+X3GiV1H+dnNfL7jS2CoH43Z3aXYCWgqMxEuvXvIrIPa6XAYNo /F5UGkONknBjxC/Pr9w/jORC8oW0AYZJlHmpTQOHedgsrCBPXmyYSu/pafS6O2V9 w5BGLpkmTQAX/Hr/DuGD0JGqVcOvGhVAgcrdBxDfEMNti+Lbw7QpRGlkaWVyIFN0 ZXZlbnMgPGRpZGllci5zdGV2ZW5zQGdtYWlsLmNvbT6IYAQTEQIAIAUCRyD48QIb AwYLCQgHAwIEFQIIAwQWAgMBAh4BAheAAAoJEHdz1uvbYxaW5iwAnRJp2jEfQ6h7 cvv4VT86VG6QzBzzAJ9l1FLWhOHDofRUAhZdYSLZjnURSbkCDQRHIPjxEAgAt21C uJWdsVbhnOOO/bfMuQOUrceh0DUDuO76QWrQSxz/vFSrVxBtSKct9GTICEk+3GXQ I1pmuxkAYcr3J1G36bKoPnMyX7x/+tJC+WkoroKzTVMlahdFjmI04Tc8iBYTwROn 8i6J5l9hoaNKLKfdV6Xmw0Y7A9w9wVRo09NkJiSzff3iQbis0mrh/jxup1coa4L+ 4FBjIHztt+7LXfwqKqBM1OnXvLPlSTJT4/KjRnCdNDy+zxz6g6Yzy4NNTcP0+EFr CijuE7/jLZho6P79Qt2nfe2O9BTQW6jIFaF2guvGMsEqgX9MtWxnd+P7KSz+1CtL sYkfiEdF8qp8ubHiswADBQf/XuRea1pMXKUs3f//Y7GRWtm2s9jPY5uSYqY7XaOm lsEflToedo8KxfymgA3axyI2QwxTEBnanPJQdPPd/vBSBCKmp5ihsFcKO30AKtbC J5SFRzTJmjwtaSRjI4CMZbIJCjb7uCSzF6ylEGIBypt+MbBXEhmGsv886Sm5PpR/ vXfZdtzFxMILJ8wgxSh5wtQ+rZHZUsPRszb45fUuaSPquStpndqp/Stx14s1LfGg Inpxn3eh+sz6iksaIb9mDZ5jcuRTx9rH43TkZRpdvk3WIHBo/6YFdOZUEhzKLYnO Fmjssq5wXIt2inj+C6H9kgLOYhb+bj8+GbdNhQT5oXH4EIhJBBgRAgAJBQJHIPjx AhsMAAoJEHdz1uvbYxaWAWoAoIH4MxPReBq32E2gmqrzOXXcL6BkAJ9L6FXNh9pH x7z8V6php7uMJQX6UA== =8AJk -----END PGP PUBLIC KEY BLOCK-----

 X86asm.net
X86asm.net
x86asm.net
Focused mainly on x86 architecture, including x86-64 architecture, instruction encodings, reverse code engineering, and system programming in Windows and Linux OS.

 Skullsecurity.org
Skullsecurity.org
SkullSecurity » Adventures In Security
BSidesSF 2022 Writeups: Miscellaneous Challenges (loca, reallyprettymundane) Leave a reply Hey folks, This is my (Ron's / iagox86's) author writeups for the BSides San Francisco 2022 CTF. You can get the full source code for everything on github. Most have either a Dockerfile or instructions on how to run locally....
 Kalilinuxtutorials.com
Kalilinuxtutorials.com
Kali Linux Tutorials - A Single Stop for Kali Linux Tools
Kali Linux tutorials is an independent platform that covers step by tutorials, advanced penetration testing, Ethical Hacking and network security tools.

 Securityonline.info
Securityonline.info
Penetration Testing • Information Security
Securityonline is a huge security community. It is committed to the sharing of high-quality technical articles and safety reports, focusing on high-quality security and security incidents in the industry.

 Fpvfrenzy.com
Fpvfrenzy.com
Best FPV Goggles and Reviews - Drone Goggles - FPV Frenzy
FPV (First-person view) flying is an incredible experience. You can experience what it’s like to fly like a bird, zoom through your own personal roller coaster doing flips, rolls, crazy maneuvers, or if you are more relaxed, you can just soar and enjoy the view – through FPV goggles. So which are the best FPV […]

 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies
 Oscarliang.com
Oscarliang.com
Oscar Liang - FPV Drone Tutorials and Reviews
FPV Drone Tutorials and Reviews, a blog for RC hobbyists to get latest information about quadcopter and multirotor products and technology development, delivered to you by Oscar Liang.
 Kitploit.com
Kitploit.com
KitPloit - PenTest & Hacking Tools
Leading source of security tools, hacking tools, cybersecurity and network security. Learn about new tools and updates in one place.

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.
 Samsclass.info
Samsclass.info
samsclass.info: Sam Bowne Class Information
Pacific Hackers IhackNFT - Cryptocurrency CTF Fri, July 15, 2022, 9:00 AM - 5:00 PM PDT Hacker Dojo 855 Maude Ave · Mountain View, CA HOPE 2022 July 22-24, 2022 New York City Approved Workshops Violent Python 3 · Friday 22-July-2022, 12:00-15:00 · Workshop B Threat Hunting with Splunk ·...
 Asmcommunity.net
Asmcommunity.net
ASM Community
Notice ASM Community is now closed and has been turned into a static archive. Looking for an answer? Browse the forums archive or use Google Search. Want to ask a question? We recommend the following places to ask new questions. Stack Overflow has a large, active and knowledgeable member base....

 N0where.net
N0where.net
CyberPunk Network
Welcome to CyberPunk PLTG Trix. No ELSUR. No ELINT. No censorship. No Ads. No data mining. No tracking. No Spyware.

 Exetools.com
Exetools.com
Aaron's Homepage
How to improve your cracking and programming skills?Welcome to the EXETOOLS, almost the largest archive of cracking stuff in the internet.I have many tools, tutorials and sources, including SoftICE (the best cracking tool on Earth), W32Dasm (a nice decompiler), and Hiew, my favourite hexeditor. In the tutorials section you can find a great collection of +ORC and tKC tutors.

 Freetechsecrets.com
Freetechsecrets.com
Free Tech Secrets ;)
On this site we will try to gather most useful technical manuals and references in most convinient and readable form. Most useful WinAPI programmer's references in most convenient format. Win32 Programmer's Reference (win32.hlp) Win32 Multimedia Programmer's Reference (mmedia.hlp) OLE Programmer's Reference (ole.hlp) Pen API Programmer's Reference (penapi.hlp) Sockets 2 Reference...

 Openinfosecfoundation.org
Openinfosecfoundation.org
OISF | Community Driven, Open Source
The Open Information Security Foundation is a 501(c)3 nonprofit organization created to build community and to support open source security technologies like Suricata, the world-class IDS/IPS network monitoring engine.

 Sensepost.com
Sensepost.com
:: Orange Cyberdefense ::
Services Blog Contact us SensePost an ethical hacking team of Orange Cyberdefense SensePost is now a team within Orange Cyberdefense, and you can find our new home at orangecyberdefense.com [ Services ] [ Blog ] [ Contact Us ] we hack, defend, teach With 20 years of research-lead innovation and...

 Seclists.org
Seclists.org
SecLists.Org Security Mailing List Archive
Security mailing list archive for the Nmap lists, Bugtraq, Full Disclosure, Security Basics, Pen-test, and dozens more. Search capabilities and RSS feeds with smart excerpts are available

 Snort.org
Snort.org
Snort - Network Intrusion Detection & Prevention System
Snort is an open-source, free and lightweight network intrusion detection system (NIDS) software for Linux and Windows to detect emerging threats.
 Sectools.org
Sectools.org
SecTools.Org Top Network Security Tools
Rankings and reviews of computer and network security software, programs, and tools.

 Hex-rays.com
Hex-rays.com
Hex Rays – State-of-the-art binary code analysis solutions
IDA Version 7.7sp1 Enjoy your IDA Pro with many new features and enhancements including: iOS15 and macOS 12 support Clang-based C++ parser Golang improvements UI candy New processors Type system MIPS64 And much more! See what’s new Update now IDA Pro A powerful disassembler and a versatile debugger Buy Learn...
 Pinvoke.net
Pinvoke.net
pinvoke.net: the interop wiki!
Search Module: [All] advapi32 avifil32 aygshell cards cfgmgr32 comctl32 comdlg32 Constants coredll credui crypt32 dbghelp dbghlp dbghlp32 Delegates dhcpsapi difxapi dmcl40 dnsapi dtl dwmapi Enums faultrep fbwflib fltlib fwpuclnt gdi32 gdiplus getuname glossary glu32 glut32 gsapi hhctrl hid hlink httpapi icmp imm32 Interfaces ipaqutil iphlpapi iprop irprops kernel32 mapi32 MinCore...

 Husseinsspace.com
Husseinsspace.com
Apache2 Ubuntu Default Page: It works
Ubuntu's Apache2 default configuration is different from the upstream default configuration, and split into several files optimized for interaction with Ubuntu tools. The configuration system is fully documented in /usr/share/doc/apache2/README.Debian.gz. Refer to this for the full documentation. Documentation for the web server itself can be found by accessing the manual...

 Malware-analyzer.com
Malware-analyzer.com
Malware-Analyzer - Malware Analysis Tools and Resources
Your one stop resource to malware analysis tools!We have compiled a list of malware analysis tools such as: Memory Forensics tools and JavaScript Analysis Tools

 Masmforum.com
Masmforum.com
Masm Forum Website
The MASM32 Website This is the website for the MASM32 SDK. It contains the main download sites around the world, installation technical data, the MASM32 licence and ralated historical data on the Microsoft assembler MASM. The MASM32 Forum Direct link to the MASM32 support forum with extensive technical data in...
 Hexblog.com
Hexblog.com
Hex-Rays Blog – Hex Rays
Page 1 of 32 Igor’s tip of the week #96: Loading additional files Posted on: &nbsp 04 Jul 2022 By: &nbsp Igor Skochinsky Categories:&nbsp News Tags:&nbsp Although most of the time IDA is used to work on single, self-contained file (e.g. an executable, library, or a...
 Hydrasky.com
Hydrasky.com
All things in moderation – We are local security
+ UAC BYPASS VIA DOTNET PROFILER ON WINDOWS 10 Vulnerabilities and Exploits In the previous post, we know how to use Registry Hijacking to bypass UAC on Windows 10. Today, we continue to do that with different technique with … By Stephen Stinson May 20, 2020 + + UAC Bypass Via...
 Intofpv.com
Intofpv.com
IntoFPV Forum | FPV and Multirotor online Community
FPV flying and multirotors Forums. Run by friendly hobbyists who provide information on RC product reviews, tutorials and general support to beginners
 Openrcforums.com
Openrcforums.com
openrcforums - Index page
OPENRC News & Information Topics Posts Last post General Information & Rules General Information & Rules Topics: 76 76 Topics 797 Posts Last post Horus X12S Firmware update by 25wood25 View the latest post Thu Sep 02, 2021 9:13 pm Feedback Have something to say about 9xForums? Whether it...

 Suricata-ids.org
Suricata-ids.org
Home - Suricata
Community Driven. Always Alert. Suricata is the leading independent open source threat detection engine. By combining intrusion detection (IDS), intrusion prevention (IPS), network security monitoring (NSM) and PCAP processing, Suricata can quickly identify, stop, and assess even the most sophisticated attacks. Check out our NEW on-demand training course! Features Features...

 Propwashed.com
Propwashed.com
The Ultimate FPV Quadcopter Resource | Propwashed.com
We love drone racing and FPV quadcopters. Weekly articles on how to build, fly, and repair racing drones.
 Kali.tools
Kali.tools
Инструменты Kali Linux - Список инструментов для тестирования на проникновение и их описание
Сбор информации acccheck ace-voip Amap AQUATONE arp-scan Automater badKarma bing-ip2hosts braa Bro Bypass firewalls by abusing DNS history CaseFile CATPHISH CDPSnarf cisco-torch CloudFail Cookie Cadger copy-router-config DMitry dnmap dnsenum dnsmap DNSRecon dnstracer dnstwist dnswalk DotDotPwn Dublin Traceroute enum4linux enumIAX exploitdb EyeWitness Faraday FinalRecon Fierce Firewalk flashlight fragroute fragrouter Ghost Phisher...
 Fpv-flightclub.com
Fpv-flightclub.com
Home 3 - FPV FlightClub
Your Headquarters for FPV Drone Racing Information and Products Welcome to FlightClub, where you’ll find everything you need to enjoy the fast-growing hobby of FPV drone racing (First Person View). FPV racing gives you an on-board view from a drone that can fly at speeds of over 100 miles per...

 Andreafortuna.org
Andreafortuna.org
Andrea Fortuna | Cybersecurity expert, software developer, experienced digital forensic analyst, musician
Cybersecurity expert, software developer, experienced digital forensic analyst, musician

 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!
Technologies Used by aldeid.com
Dns Records of aldeid.com
A Record: 104.21.5.202 172.67.133.209AAAA Record: 2606:4700:3033::ac43:85d1 2606:4700:3032::6815:5ca
CNAME Record:
NS Record: brad.ns.cloudflare.com ruth.ns.cloudflare.com
SOA Record: dns.cloudflare.com
MX Record:
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of aldeid.com
Domain Name: aldeid.comRegistry Domain ID: 137655437_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.ovh.com
Registrar URL: https://www.ovh.com
Updated Date: 2021-12-01T23:08:51.0Z
Creation Date: 2004-12-17T19:44:51.0Z
Registrar Registration Expiration Date: 2022-12-17T19:44:51.0Z
Registrar: OVH, SAS
Registrar IANA ID: 433
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +33.972101007
Domain Status: clientDeleteProhibited https://icann.org/epp#clientDeleteProhibited
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Registry Registrant ID:
Registrant Name: REDACTED FOR PRIVACY
Registrant Organization:
Registrant Street: REDACTED FOR PRIVACY
Registrant City: REDACTED FOR PRIVACY
Registrant State/Province:
Registrant Postal Code: REDACTED FOR PRIVACY
Registrant Country: FR
Registrant Phone: REDACTED FOR PRIVACY
Registrant Phone Ext: REDACTED FOR PRIVACY
Registrant Fax: REDACTED FOR PRIVACY
Registrant Fax Ext: REDACTED FOR PRIVACY
Send message to contact by visiting https://www.ovhcloud.com/en/lp/request-ovhcloud-registered-domain/
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: REDACTED FOR PRIVACY
Admin Organization: REDACTED FOR PRIVACY
Admin Street: REDACTED FOR PRIVACY
Admin City: REDACTED FOR PRIVACY
Admin State/Province: REDACTED FOR PRIVACY
Admin Postal Code: REDACTED FOR PRIVACY
Admin Country: REDACTED FOR PRIVACY
Admin Phone: REDACTED FOR PRIVACY
Admin Phone Ext: REDACTED FOR PRIVACY
Admin Fax: REDACTED FOR PRIVACY
Admin Fax Ext: REDACTED FOR PRIVACY
Send message to contact by visiting https://www.ovhcloud.com/en/lp/request-ovhcloud-registered-domain/
Admin Email: [email protected]
Registry Tech ID:
Tech Name: REDACTED FOR PRIVACY
Tech Organization: REDACTED FOR PRIVACY
Tech Street: REDACTED FOR PRIVACY
Tech City: REDACTED FOR PRIVACY
Tech State/Province: REDACTED FOR PRIVACY
Tech Postal Code: REDACTED FOR PRIVACY
Tech Country: REDACTED FOR PRIVACY
Tech Phone: REDACTED FOR PRIVACY
Tech Phone Ext: REDACTED FOR PRIVACY
Tech Fax: REDACTED FOR PRIVACY
Tech Fax Ext: REDACTED FOR PRIVACY
Send message to contact by visiting https://www.ovhcloud.com/en/lp/request-ovhcloud-registered-domain/
Tech Email: [email protected]
Name Server: brad.ns.cloudflare.com
Name Server: ruth.ns.cloudflare.com
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System:
http://wdprs.internic.net/
>>> Last update of WHOIS database: 2021-12-02T00:09:54.0Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
###############################################################################
#
# Welcome to the OVH WHOIS Server.
#
# whois server : whois.ovh.com check server : check.ovh.com
#
# The data in this Whois is at your disposal with the aim of supplying you the
# information only, that is helping you in the obtaining of the information
# about or related to a domain name registration record. OVH Sas make this
# information available "as is", and do not guarantee its accuracy. By using
# Whois, you agree that you will use these data only for legal purposes and
# that, under no circumstances will you use this data to: (1) Allow, enable,
# or otherwise support the transmission of mass unsolicited, commercial
# advertisement or roughly or requests via the individual mail (courier),
# the E-mail (SPAM), by telephone or by fax. (2) Enable high volume, automated,
# electronic processes that apply to OVH Sas (or its computer systems).
# The copy, the compilation, the re-packaging, the dissemination or the
# other use of the Whois base is expressly forbidden without the prior
# written consent of OVH. Domain ownership disputes should be settled using
# ICANN's Uniform Dispute Resolution Policy: http://www.icann.org/udrp/udrp.htm
# We reserve the right to modify these terms at any time. By submitting
# this query, you agree to abide by these terms. OVH Sas reserves the right
# to terminate your access to the OVH Sas Whois database in its sole
# discretion, including without limitation, for excessive querying of
# the Whois database or for failure to otherwise abide by this policy.
#
# L'outil du Whois est à votre disposition dans le but de vous fournir
# l'information seulement, c'est-à-dire vous aider dans l'obtention de
# l'information sur ou lié à un rapport d'enregistrement de nom de domaine.
# OVH Sas rend cette information disponible "comme est," et ne garanti pas
# son exactitude. En utilisant notre outil Whois, vous reconnaissez que vous
# emploierez ces données seulement pour des buts légaux et ne pas utiliser cet
# outil dans les buts suivant: (1) la transmission de publicité non sollicitée,
# commerciale massive ou en gros ou des sollicitations via courrier individuel,
# le courrier électronique (c'est-à-dire SPAM), par téléphone ou par fax. (2)
# l'utilisation d'un grand volume, automatisé des processus électroniques qui
# soulignent ou chargent ce système de base de données Whois vous fournissant
# cette information. La copie de tout ou partie, la compilation, le
# re-emballage, la dissémination ou d'autre utilisation de la base Whois sont
# expressément interdits sans consentement écrit antérieur de OVH. Un désaccord
# sur la possession d'un nom de domaine peut être résolu en suivant la Uniform
# Dispute Resolution Policy de l'ICANN: http://www.icann.org/udrp/udrp.htm
# Nous nous réservons le droit de modifier ces termes à tout moment. En
# soumettant une requête au Whois vous consentez à vous soumettre à ces termes.
# local time : Sunday, 03-Jul-22 02:56:42 UTC
# gmt time : Sunday, 03-Jul-22 02:56:42 GMT
# last modify : Wednesday, 01-Dec-21 23:48:14 UTC
# request from : 38.242.237.160:60242
 172.67.27.10
172.67.27.10
 United States
United States
 Valid SSL
Valid SSL