samsclass.info: Sam Bowne Class Information
Pacific Hackers IhackNFT - Cryptocurrency CTF Fri, July 15, 2022, 9:00 AM - 5:00 PM PDT Hacker Dojo 855 Maude Ave · Mountain View, CA HOPE 2022 July 22-24, 2022 New York City Approved Workshops Violent Python 3 · Friday 22-July-2022, 12:00-15:00 · Workshop B Threat Hunting with Splunk ·...
Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time: 0.55298
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 814
Links
ratio 32.637913741224
SSL Details
SSL Issuer:
Issuer: Cloudflare Inc ECC CA-3
Valid From: 2022-05-17 00:00:00
Expiration Date: 2023-05-17 23:59:59
SSL Organization:
Signature c0ba2860acfe7f283d0731cf66863b14c737970e
Algorithm: ecdsa-with-SHA256
Found 69 Top Alternative to Samsclass.info

 Hashcat.net
Hashcat.net
hashcat - advanced password recovery
World's fastest and most advanced password recovery utility


 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.

 Mypeq.com
Mypeq.com
Pepper - IoT for the future.
PEPPER IS A SECURE, FULL-STACK IOT PLATFORM-AS-A-SERVICE (PAAS) TRUSTED TO BUILD AND DELIVER SCALABLE IOT SOLUTIONS.


 Onlinehashcrack.com
Onlinehashcrack.com
Online Password Hash Crack - MD5 NTLM Wordpress Joomla WPA PMKID, Office, iTunes, Archive, ..
OnlineHashCrack is a powerful hash cracking and recovery online service for MD5 NTLM Wordpress Joomla SHA1 MySQL OSX WPA, PMKID, Office Docs, Archives, PDF, iTunes and more!

 Infoheap.com
Infoheap.com
InfoHeap - Tech tutorials, tips, tools and more
CSS CSS properties CSS selectors Javascript Tutorials AngularJS ReactJS HTML tutorials HTML tags HTML cookbook PHP tutorials PHP regex PHP functions online Python tutorials Python read more

 Wazuh.com
Wazuh.com
Wazuh · The Open Source Security Platform
Wazuh is a free, open source and enterprise-ready security monitoring solution for threat detection, integrity monitoring, incident response and compliance.

 Asecuritysite.com
Asecuritysite.com
Security and So Many Things
Cipher test On-line Cipher test Printed Cipher Test Fun Tests Quick Jump (Cryptography) AES Blockchain/Cryptocurrency Ciphers Codes Cipher Cracking Crypto Pairing Curve 25519 Digital Cert and Trust Discrete Logs (solve) EdDSA, Ed25519 and Ed448 ElGamal Elliptic Curve ECDH ECDSA ECC Encryption (ECIES) Ethereum Factorization Format Preserving Enc Galois fields Hashing...
 Kalilinuxtutorials.com
Kalilinuxtutorials.com
Kali Linux Tutorials - A Single Stop for Kali Linux Tools
Kali Linux tutorials is an independent platform that covers step by tutorials, advanced penetration testing, Ethical Hacking and network security tools.

 Yeahhub.com
Yeahhub.com
Yeah Hub - Kali Linux Tutorials | Tech News | SEO Tips and Tricks
Kali Linux Tutorials | Tech News | SEO Tips and Tricks
 Websistent.com
Websistent.com
Jesin's Blog - Welcome to the Portal of Technology
Tutorials and How-tos on Linux, PHP, Web Design, Virtualization, Windows, Videos on Cisco networking, tools to generate htdigest and htaccess files.

 Securityonline.info
Securityonline.info
Penetration Testing • Information Security
Securityonline is a huge security community. It is committed to the sharing of high-quality technical articles and safety reports, focusing on high-quality security and security incidents in the industry.

 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies
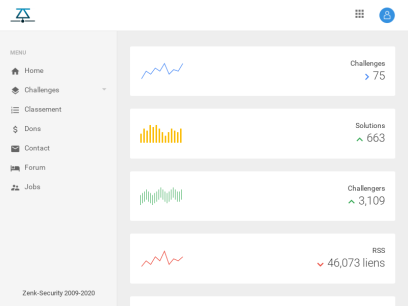
 Zenk-security.com
Zenk-security.com
ZenK-Security :: Communauté de sécurité informatique
Zenk Security est une communauté de hacking et de sécurité informatique francophone basé sur le partage et l'apprentissage.

 Fuzzysecurity.com
Fuzzysecurity.com
FuzzySecurity | Home
Welcome to FuzzySecurity 2.0 bringing you new content in responsive HTML5 and CSS3!! Introduction "Beware of fuzzy security-monsters!!". Hello and welcome everybody, it has been an interesting ride so far and there is much more to come. I would like to take a moment to say a few things and...

 Andreafortuna.org
Andreafortuna.org
Andrea Fortuna | Cybersecurity expert, software developer, experienced digital forensic analyst, musician
Cybersecurity expert, software developer, experienced digital forensic analyst, musician

 Hackercool.com
Hackercool.com
Hackercool Magazine - Ethical Hacking Magazine for hackers
Hacking Magazine with a difference. That's what Hackercool Magazine is. Learn Blackhat hacking. is a cyber security monthly magazine that
 Aldeid.com
Aldeid.com
aldeid
Pentesting   •    Web Exploitation   •    Cryptography   •    Forensics   •    Reversing   •    Binary Exploitation   •    CTF   •    Threat Hunting TryHackMe > Unbaked Pie Sun, 6 Jun 2021 11:34:00 +0000 Enumerate a Django application, find a vulnerability, exploit a pickle session cookie, evade a docker environment, find a way to forward ports, brute force an SSH account, this challenge...
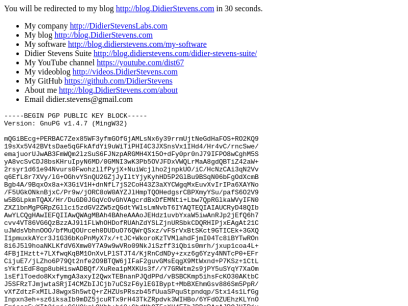
 Didierstevens.com
Didierstevens.com
Didier Stevens
-----BEGIN PGP PUBLIC KEY BLOCK----- Version: GnuPG v1.4.7 (MingW32) mQGiBEcg+PERBAC7Zex85WF3yfmGOfGjAMLsNx6y39rrmUjtNeGdHaFOS+RO2KQ9 19sXx5V42BVtsDae5qGFkAfdYi9uWiTiPHI4C3JXSnsVx1IHd4/Hr4vC/rncSwe/ emajuorUJwAB3FmWQm2lzSuS6FJNzpARGMH4X15O+dFy0pr0nJ79IFPO8wCghM5S yA8vcSvCDJ8bsKHruIpyN6MD/0GMNI3wK3Pb5OVJFDxVWQLrMaA8gdQBTiZ42aW+ 2rsyr1d61e94Nvurs0FwohzllfPyjX+NuiWcjlho2jnpkUO/iC/HcNzCAi3qN2Vv q6EfL8r7XVy/lG+OGhvYSnQU2GZjJyIltYjyKyhHD5P2GlBu9BSqN06bFgOdXcmB Bgb4A/9BqxOx8a+X3GiV1H+dnNfL7jS2CoH43Z3aXYCWgqMxEuvXvIrIPa6XAYNo /F5UGkONknBjxC/Pr9w/jORC8oW0AYZJlHmpTQOHedgsrCBPXmyYSu/pafS6O2V9 w5BGLpkmTQAX/Hr/DuGD0JGqVcOvGhVAgcrdBxDfEMNti+Lbw7QpRGlkaWVyIFN0 ZXZlbnMgPGRpZGllci5zdGV2ZW5zQGdtYWlsLmNvbT6IYAQTEQIAIAUCRyD48QIb AwYLCQgHAwIEFQIIAwQWAgMBAh4BAheAAAoJEHdz1uvbYxaW5iwAnRJp2jEfQ6h7 cvv4VT86VG6QzBzzAJ9l1FLWhOHDofRUAhZdYSLZjnURSbkCDQRHIPjxEAgAt21C uJWdsVbhnOOO/bfMuQOUrceh0DUDuO76QWrQSxz/vFSrVxBtSKct9GTICEk+3GXQ I1pmuxkAYcr3J1G36bKoPnMyX7x/+tJC+WkoroKzTVMlahdFjmI04Tc8iBYTwROn 8i6J5l9hoaNKLKfdV6Xmw0Y7A9w9wVRo09NkJiSzff3iQbis0mrh/jxup1coa4L+ 4FBjIHztt+7LXfwqKqBM1OnXvLPlSTJT4/KjRnCdNDy+zxz6g6Yzy4NNTcP0+EFr CijuE7/jLZho6P79Qt2nfe2O9BTQW6jIFaF2guvGMsEqgX9MtWxnd+P7KSz+1CtL sYkfiEdF8qp8ubHiswADBQf/XuRea1pMXKUs3f//Y7GRWtm2s9jPY5uSYqY7XaOm lsEflToedo8KxfymgA3axyI2QwxTEBnanPJQdPPd/vBSBCKmp5ihsFcKO30AKtbC J5SFRzTJmjwtaSRjI4CMZbIJCjb7uCSzF6ylEGIBypt+MbBXEhmGsv886Sm5PpR/ vXfZdtzFxMILJ8wgxSh5wtQ+rZHZUsPRszb45fUuaSPquStpndqp/Stx14s1LfGg Inpxn3eh+sz6iksaIb9mDZ5jcuRTx9rH43TkZRpdvk3WIHBo/6YFdOZUEhzKLYnO Fmjssq5wXIt2inj+C6H9kgLOYhb+bj8+GbdNhQT5oXH4EIhJBBgRAgAJBQJHIPjx AhsMAAoJEHdz1uvbYxaWAWoAoIH4MxPReBq32E2gmqrzOXXcL6BkAJ9L6FXNh9pH x7z8V6php7uMJQX6UA== =8AJk -----END PGP PUBLIC KEY BLOCK-----
 Techglimpse.com
Techglimpse.com
Techglimpse.com - Linux, WordPress, HTML, CSS Tutorials and Guides
We write How to Tutorials on Linux, HTML, CSS, Android apps and Wordpress. Most frequently faced errors and solutions are discussed.
 Crackstation.net
Crackstation.net
CrackStation - Online Password Hash Cracking - MD5, SHA1, Linux, Rainbow Tables, etc.
Crackstation is the most effective hash cracking service. We crack: MD5, SHA1, SHA2, WPA, and much more...
 Cybrary.it
Cybrary.it
Free Cybersecurity Training and Career Development | Cybrary
Cybersecurity training from Cybrary will take your career to the next level. We have the cybersecurity courses that can help get you there!

 Trustedsec.com
Trustedsec.com
TrustedSec | Cybersecurity
Cybersecurity consultants with expertise in penetration testing, social engineering and enterprise risk management - Learn how TrustedSec can help protect your company.
 Kwikset.com
Kwikset.com
Door Locks, Door Hardware, Smart Locks & Smartkey Technology | Kwikset
Kwikset is a secure door lock industry leader & innovator in home safety with keyless entry and re-keying technology for residential and commercial door hardware
 Metasploit.com
Metasploit.com
Metasploit | Penetration Testing Software, Pen Testing Security | Metasploit
Find security issues, verify vulnerability mitigations & manage security assessments with Metasploit. Get the world's best penetration testing software now.
 Blackmoreops.com
Blackmoreops.com
Linux, InfoSec, Hacking - blackMORE Ops
blackMORE Ops is the leading source for Kali Linux, InfoSec, Hacking, Network and Cyber Security, How to, Guides and Tutorials with technical details.

 Hacking-tutorial.com
Hacking-tutorial.com
Ethical Hacking Tutorials, Tips and Tricks - Free Tutorials, Tools, How to's
Ethical Hacking Tutorial, Tips and Trick. Free hacking knowledge, learn how to hack



 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.
 Sectools.org
Sectools.org
SecTools.Org Top Network Security Tools
Rankings and reviews of computer and network security software, programs, and tools.
 Wireshark.org
Wireshark.org
Wireshark · Go Deep.
Download Get Started Now Learn Knowledge is Power Go Beyond With Wireshark Sponsors About Wireshark About Awards and Accolades Authors Wireshark Sponsors Wireshark is the world’s foremost and widely-used network protocol analyzer. It lets you see what’s happening on your network at a microscopic level and is the de facto...

 Hex-rays.com
Hex-rays.com
Hex Rays – State-of-the-art binary code analysis solutions
IDA Version 7.7sp1 Enjoy your IDA Pro with many new features and enhancements including: iOS15 and macOS 12 support Clang-based C++ parser Golang improvements UI candy New processors Type system MIPS64 And much more! See what’s new Update now IDA Pro A powerful disassembler and a versatile debugger Buy Learn...

 Datascience.com.co
Datascience.com.co
Data Science
Personal Blog About Machine Learning, Data Science, Computer Vision and Python.

 Drchaos.com
Drchaos.com
Home | Cyber | Dr. Chaos
Discussions, Concepts & Technologies for the world of Cyber & Infosec. Join the discussion and keep up to date with our 'Dark Security and Total Chaos' blog!

 0x00sec.org
0x00sec.org
0x00sec - The Home of the Hacker
The Home of the Hacker - Malware, Reverse Engineering, and Computer Science.
 Genymotion.com
Genymotion.com
Genymotion – Android Emulator for app testing Cross-platform Android Emulator for manual and automated app testing
Android as a Service Android Virtual Devices for all your development & testing needs Empower your Android teams with Virtual Devices that truly scale Cloud versions All products COMPATIBILITY ✓ With all testing framework based on ADB Appium, Espresso, Robotium, etc. ✓ With popular Continuous Integration solutions CircleCI, Bitrise, Terraform,...

 Kali.org
Kali.org
Kali Linux | Penetration Testing and Ethical Hacking Linux Distribution
Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking and network security assessments.

 Miloserdov.org
Miloserdov.org
Ethical hacking and penetration testing - InfoSec, IT, Kali Linux, BlackArch
The complete guide to Wine: from installation to advanced usage Table of contents 1. Why Wine 2. Features and limitations of Wine 3. 64-bit or 32-bit Wine? 4. How to install Wine 4.1 Installing Wine on Debian, Kali Linux, Linux Mint, Ubuntu, and their derivatives 4.2 Installing Wine on Arch Linux 5. How...

 Darknet.org.uk
Darknet.org.uk
Darknet - Hacking Tools, Hacker News & Cyber Security
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.
 Cobaltstrike.com
Cobaltstrike.com
Cobalt Strike | Adversary Simulation and Red Team Operations
Cobalt Strike in an adversary simulation tool that can emulate the tactics and techniques of a quiet long-term embedded threat actor in an IT network using Beacon, a post-exploitation agent and covert channels.

 Cyberpratibha.com
Cyberpratibha.com
Cyber Pratibha | Enhance Cyber Skills
One Step Towards, Secure Cyber Word It's your turn to help to secure cyber space by enhancing your technical skills including Expertise in Linux, Wireless Security, Advanced in Kali Linux, Ethical Hacking and more Start Your Journy Work as volunteer Online Classes One to one, One to many classes make you | Cyber Pratibha

 Pentestingshop.com
Pentestingshop.com
Pentestingshop
Pentesting for everyone Our webshop supplies all the stuff u need to do a pentest yourself. Including tutorials with the products. Webshop Tutorials Pentesting Supplies Categories WiFi Supplies Shop USB Gadgets Shop OUR LATEST View Signup for newsletter Lorem ipsum dolor sit amet, consectetuer adipiscing elit, sed diam nonummy nibh...
Technologies Used by samsclass.info
Dns Records of samsclass.info
A Record: 104.21.17.27 172.67.219.198AAAA Record: 2606:4700:3036::ac43:dbc6 2606:4700:3034::6815:111b
CNAME Record:
NS Record: tom.ns.cloudflare.com coco.ns.cloudflare.com
SOA Record: dns.cloudflare.com
MX Record: mail.mailinator.com
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of samsclass.info
Domain Name: samsclass.infoRegistry Domain ID: d5633947-lrms
Registrar WHOIS Server: whois.ionos.com
Registrar URL: http://ionos.com
Updated Date: 2017-01-23T22:20:56.000Z
Creation Date: 2004-01-23T14:49:50.000Z
Registrar Registration Expiration Date: 2023-01-23T14:49:50.022Z
Registrar: IONOS SE
Registrar IANA ID: 83
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.8774612631
Reseller:
Domain Status: clientTransferProhibited https://www.icann.org/epp#clientTransferProhibited
Domain Status: autoRenewPeriod https://www.icann.org/epp#autoRenewPeriod
Registry Registrant ID: REDACTED FOR PRIVACY
Registrant Name: REDACTED FOR PRIVACY
Registrant Organization:
Registrant Street: REDACTED FOR PRIVACY
Registrant City: REDACTED FOR PRIVACY
Registrant State/Province: CA
Registrant Postal Code: REDACTED FOR PRIVACY
Registrant Country: US
Registrant Phone: REDACTED FOR PRIVACY
Registrant Phone Ext:
Registrant Fax: REDACTED FOR PRIVACY
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID: REDACTED FOR PRIVACY
Admin Name: REDACTED FOR PRIVACY
Admin Organization: REDACTED FOR PRIVACY
Admin Street: REDACTED FOR PRIVACY
Admin City: REDACTED FOR PRIVACY
Admin State/Province: REDACTED FOR PRIVACY
Admin Postal Code: REDACTED FOR PRIVACY
Admin Country: REDACTED FOR PRIVACY
Admin Phone: REDACTED FOR PRIVACY
Admin Phone Ext: REDACTED FOR PRIVACY
Admin Fax: REDACTED FOR PRIVACY
Admin Fax Ext: REDACTED FOR PRIVACY
Admin Email: [email protected]
Registry Tech ID: REDACTED FOR PRIVACY
Tech Name: REDACTED FOR PRIVACY
Tech Organization: REDACTED FOR PRIVACY
Tech Street: REDACTED FOR PRIVACY
Tech City: REDACTED FOR PRIVACY
Tech State/Province: REDACTED FOR PRIVACY
Tech Postal Code: REDACTED FOR PRIVACY
Tech Country: REDACTED FOR PRIVACY
Tech Phone: REDACTED FOR PRIVACY
Tech Phone Ext: REDACTED FOR PRIVACY
Tech Fax: REDACTED FOR PRIVACY
Tech Fax Ext: REDACTED FOR PRIVACY
Tech Email: [email protected]
Nameserver: tom.ns.cloudflare.com
Nameserver: coco.ns.cloudflare.com
DNSSEC: Unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-06-16T19:28:10Z <<<
For more information on Whois status codes, please visit https://icann.org/epp

 192.124.249.5
192.124.249.5
 United States
United States
 Valid SSL
Valid SSL