Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time:
SSL: Disable
Status: up
Code To Txt Ratio
Word Count
Links
ratio
Found 76 Top Alternative to Sans.edu


 Sans.org
Sans.org
Cyber Security Training | SANS Courses, Certifications & Research
SANS Institute is the most trusted resource for cybersecurity training, certifications and research. Offering more than 60 courses across all practice areas, SANS trains over 40,000 cybersecurity professionals annually.

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.

 Paloaltonetworks.com
Paloaltonetworks.com
Global Cybersecurity Leader - Palo Alto Networks
Palo Alto Networks enables your team to prevent successful cyberattacks with an automated approach that delivers consistent security across cloud, network and mobile.

 Abuseipdb.com
Abuseipdb.com
AbuseIPDB - IP address abuse reports - Making the Internet safer, one IP at a time
Check an IP Address, Domain Name, or Subnet e.g. 38.242.237.160, microsoft.com, or 5.188.10.0/24 Check AbuseIPDB making the internet safer, one IP at a time Report abusive IPs engaging in hacking attempts or other malicious behavior and help fellow sysadmins! Report IP Now Check the report history of any IP address...

 Grc.com
Grc.com
Home of Gibson Research Corporation
Steve Gibson's and Gibson Research Corporation's Web homepage.

 Cisa.gov
Cisa.gov
Homepage | CISA
CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.

 Giac.org
Giac.org
Cyber Security Certifications | GIAC Certifications
GIAC Certifications develops and administers premier, professional information security certifications. More than 30 certifications align with SANS training and ensure mastery in critical, specialized InfoSec domains. GIAC certifications provide the highest and most rigorous assurance of cyber security knowledge and skill available to industry, government, and military clients across the world.
 Csoonline.com
Csoonline.com
CSO - CSO Online – IT-Security-News für Profis
News und Insights zur Cybersicherheit im Unternehmen. Alles was CSOs wissen müssen.
 Eccouncil.org
Eccouncil.org
Certified Ethical Hacker | InfoSec Cyber Security Certification | EC-Council
EC-Council is a global leader in InfoSec Cyber Security certification programs like Certified Ethical Hacker and Computer Hacking Forensic Investigator.

 Auditmypc.com
Auditmypc.com
Audit My PC
Free Web tools include firewall test and speed test plus sitemap generator and other online tools for webmasters and home users.

 Speedguide.net
Speedguide.net
SpeedGuide :: Broadband Tweaks, Wireless Networks, Security
SpeedGuide.net - Broadband Tweaks, Tools, Info, News & more "Some of the Best Broadband Speed Tweaks on the Net" We cover Broadband Internet connections, network security, wireless and system performance. A large section of SG focuses on Cable Modems and DSL technology, stressing on improving TCP/IP performance over high speed/latency networks....
 Adminsub.net
Adminsub.net
Free online IPv4 subnet calculator - adminsub.net
Simple and fast internet online subnet masks, ip address subnet, ip subnetting, ipv4 subnet calculator. Enter ip address, network mask and get all info: address, netmask, wildcard, network, hosts and more

 Zeltser.com
Zeltser.com
Lenny Zeltser | Information Security in Business
Advances information security. Grows tech businesses. Fights malware.

 Us-cert.gov
Us-cert.gov
Homepage | CISA
As part of its mission, CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.
 Wireshark.org
Wireshark.org
Wireshark · Go Deep.
Download Get Started Now Learn Knowledge is Power Go Beyond With Wireshark Sponsors About Wireshark About Awards and Accolades Authors Wireshark Sponsors Wireshark is the world’s foremost and widely-used network protocol analyzer. It lets you see what’s happening on your network at a microscopic level and is the de facto...
 Nordicsemi.com
Nordicsemi.com
Nordic Semiconductor | Specialists in Low Power Wireless - nordicsemi.com
Nordic Semiconductor is a fabless semiconductor company specializing in wireless technology for the IoT.

 Seclists.org
Seclists.org
SecLists.Org Security Mailing List Archive
Security mailing list archive for the Nmap lists, Bugtraq, Full Disclosure, Security Basics, Pen-test, and dozens more. Search capabilities and RSS feeds with smart excerpts are available

 My-addr.com
My-addr.com
Online Free Network tools lookup:IP,Domains,Emails,Trace,Ping,DNS, etc.
Online Free Network tools lookup:IP,Domains,Emails,Trace,Ping,DNS, etc.

 Papercut.com
Papercut.com
PaperCut: Print management software
Print management software that’s helping hundreds of millions of people around the globe to minimize waste while having a secure and easy printing experience.
 Pearsonitcertification.com
Pearsonitcertification.com
Pearson IT Certification: Videos, flash cards, simulations, books, eBooks, and practice tests for Cisco, CompTIA, and Microsoft exams
Prepare for your certification with innovative learning products, question of the day alerts, blogs, interviews, and video podcasts from industry experts.
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.
 Krebsonsecurity.com
Krebsonsecurity.com
Krebs on Security – In-depth security news and investigation
In-depth security news and investigation

 Checkpoint.com
Checkpoint.com
Leader in Cyber Security Solutions | Check Point Software
Check Point Infinity architecture delivers consolidated Gen V cyber security across networks, cloud, and mobile environments.

 Fortiguard.com
Fortiguard.com
FortiGuard
View by Product Network Intrusion Protection Anti-Recon and Anti-Exploit Secure DNS IP Reputation/Anti-Botnet Indicators of Compromise IP Geolocation Service Cloud Workload Security Service Content and Endpoint Endpoint Detection & Response Anti-Virus Endpoint Vulnerability Device Detection ANN and NDR Sandbox Behavior Engine Application Web Filtering Anti-Spam Application Control Industrial Security Services...

 Cisecurity.org
Cisecurity.org
CIS Center for Internet Security
CIS is a forward-thinking nonprofit that harnesses the power of a global IT community to safeguard public and private organizations against cyber threats.
 Scmagazine.com
Scmagazine.com
SC Media | Homepage
The latest in-depth, unbiased news, analysis and perspective to keep cybersecurity professionals informed, educated and enlightened about the market.
 Symantec.com
Symantec.com
Symantec Enterprise Cloud
To meet today's Cyber Security challenges, enterprises need an integrated cyber defense platform that integrates industry-leading solutions and solves for the most pressing C-level challenges like evolving threats, privacy & compliance, and digital transformation.
 Isaca.org
Isaca.org
Advancing IT, Audit, Governance, Risk, Privacy & Cybersecurity | ISACA
ISACA is a global association that provides IT professionals with knowledge, credentials, training and community in audit, governance, risk, privacy and cybersecurity.

 Sonicwall.com
Sonicwall.com
Next-Gen Firewalls & Cybersecurity Solutions - SonicWall
Defend SMBs, enterprises and governments from advanced cyber attacks with SonicWall's award-winning firewalls and cyber security solutions.

 Ietf.org
Ietf.org
IETF | Internet Engineering Task Force
Welcome to the IETF IETF Hackathon in Philadelphia Help define and improve new Internet technologies by working on running code in Philadelphia on 23-24 July. Learn more about how anyone can participate Upcoming events IETF 114 Philadelphia IETF 114 starts Saturday 23 July and runs through Friday afternoon, 29 July....

 Watchguard.com
Watchguard.com
WatchGuard Technologies | Network Security, Secure Wi-Fi, MFA, and Endpoint Security Solutions
Award-winning solutions that are easy to deploy and manage, making enterprise-grade security accessible to any organization regardless of size or expertise.

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.
 Iana.org
Iana.org
Internet Assigned Numbers Authority
Domain Names Root Zone Registry .INT Registry .ARPA Registry IDN Repository Number Resources Abuse Information Protocols Protocol Registries Time Zone Database About Us Presentations Reports Performance Reviews Excellence Contact Us The IANA functions coordinate the Internet’s globally unique identifiers, and are provided by Public Technical Identifiers, an affiliate of ICANN....

 Trendmicro.com
Trendmicro.com
#1 bei Cloud-Sicherheit & Endpunkt-Cybersicherheit | Trend Micro (DE)
Trend Micro ist der weltweit führende Anbieter von Plattformlösungen für Cloud-Sicherheit, XDR und Cybersicherheit – für Unternehmen, Rechenzentren, Cloud-Umgebungen, Netzwerke und Endpunkte.
 Cybrary.it
Cybrary.it
Free Cybersecurity Training and Career Development | Cybrary
Cybersecurity training from Cybrary will take your career to the next level. We have the cybersecurity courses that can help get you there!
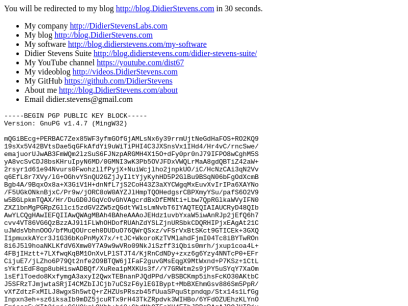
 Didierstevens.com
Didierstevens.com
Didier Stevens
-----BEGIN PGP PUBLIC KEY BLOCK----- Version: GnuPG v1.4.7 (MingW32) mQGiBEcg+PERBAC7Zex85WF3yfmGOfGjAMLsNx6y39rrmUjtNeGdHaFOS+RO2KQ9 19sXx5V42BVtsDae5qGFkAfdYi9uWiTiPHI4C3JXSnsVx1IHd4/Hr4vC/rncSwe/ emajuorUJwAB3FmWQm2lzSuS6FJNzpARGMH4X15O+dFy0pr0nJ79IFPO8wCghM5S yA8vcSvCDJ8bsKHruIpyN6MD/0GMNI3wK3Pb5OVJFDxVWQLrMaA8gdQBTiZ42aW+ 2rsyr1d61e94Nvurs0FwohzllfPyjX+NuiWcjlho2jnpkUO/iC/HcNzCAi3qN2Vv q6EfL8r7XVy/lG+OGhvYSnQU2GZjJyIltYjyKyhHD5P2GlBu9BSqN06bFgOdXcmB Bgb4A/9BqxOx8a+X3GiV1H+dnNfL7jS2CoH43Z3aXYCWgqMxEuvXvIrIPa6XAYNo /F5UGkONknBjxC/Pr9w/jORC8oW0AYZJlHmpTQOHedgsrCBPXmyYSu/pafS6O2V9 w5BGLpkmTQAX/Hr/DuGD0JGqVcOvGhVAgcrdBxDfEMNti+Lbw7QpRGlkaWVyIFN0 ZXZlbnMgPGRpZGllci5zdGV2ZW5zQGdtYWlsLmNvbT6IYAQTEQIAIAUCRyD48QIb AwYLCQgHAwIEFQIIAwQWAgMBAh4BAheAAAoJEHdz1uvbYxaW5iwAnRJp2jEfQ6h7 cvv4VT86VG6QzBzzAJ9l1FLWhOHDofRUAhZdYSLZjnURSbkCDQRHIPjxEAgAt21C uJWdsVbhnOOO/bfMuQOUrceh0DUDuO76QWrQSxz/vFSrVxBtSKct9GTICEk+3GXQ I1pmuxkAYcr3J1G36bKoPnMyX7x/+tJC+WkoroKzTVMlahdFjmI04Tc8iBYTwROn 8i6J5l9hoaNKLKfdV6Xmw0Y7A9w9wVRo09NkJiSzff3iQbis0mrh/jxup1coa4L+ 4FBjIHztt+7LXfwqKqBM1OnXvLPlSTJT4/KjRnCdNDy+zxz6g6Yzy4NNTcP0+EFr CijuE7/jLZho6P79Qt2nfe2O9BTQW6jIFaF2guvGMsEqgX9MtWxnd+P7KSz+1CtL sYkfiEdF8qp8ubHiswADBQf/XuRea1pMXKUs3f//Y7GRWtm2s9jPY5uSYqY7XaOm lsEflToedo8KxfymgA3axyI2QwxTEBnanPJQdPPd/vBSBCKmp5ihsFcKO30AKtbC J5SFRzTJmjwtaSRjI4CMZbIJCjb7uCSzF6ylEGIBypt+MbBXEhmGsv886Sm5PpR/ vXfZdtzFxMILJ8wgxSh5wtQ+rZHZUsPRszb45fUuaSPquStpndqp/Stx14s1LfGg Inpxn3eh+sz6iksaIb9mDZ5jcuRTx9rH43TkZRpdvk3WIHBo/6YFdOZUEhzKLYnO Fmjssq5wXIt2inj+C6H9kgLOYhb+bj8+GbdNhQT5oXH4EIhJBBgRAgAJBQJHIPjx AhsMAAoJEHdz1uvbYxaWAWoAoIH4MxPReBq32E2gmqrzOXXcL6BkAJ9L6FXNh9pH x7z8V6php7uMJQX6UA== =8AJk -----END PGP PUBLIC KEY BLOCK-----

 Danielmiessler.com
Danielmiessler.com
Daniel Miessler | Security, Technology, and Society
Exploring the intersection of security, technology, and society—and what might be coming next.

 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.
 Ipaddressguide.com
Ipaddressguide.com
Free IP address tools for IPv4 and IPv6 | IPAddressGuide
Free IP address tools for ping, traceroute, reverse DNS lookup, CIDR conversion, Netmask conversion, decimal conversion and IP lookup for IPv4 and IPv6

 Blackhat.com
Blackhat.com
Black Hat | Home
Black Hat Webinars Security Research in Real Time June 30, 2022 - Managing Cybersecurity as a Business Risk July 14, 2022 - InfoSec Lessons from the War in Ukraine Sponsor a Webinars View all of our recent Webinars Black Hat Archives Watch Past Presentations View all of our archived videos...

 F5.com
F5.com
F5 | Multi-Cloud Security and Application Delivery
F5 application services ensure that applications are always secure and perform the way they should—in any environment and on any device.
 Ultratools.com
Ultratools.com
UltraDNS Enterprise-grade DNS with 100% Uptime | Neustar
Neustar UltraDNS delivers 100% uptime SLA, DNSSEC support & DDoS protection to thousands of companies across the globe including Fortune 500 companies.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers

 Securityaffairs.co
Securityaffairs.co
Security Affairs - Read, think, share … Security is everyone's responsibilitySecurity Affairs
Security Affairs - Every security issue is our affair. Read, think, share … Security is everyone's responsibility

 Threatpost.com
Threatpost.com
Threatpost | The first stop for security news
Threatpost, is an independent news site which is a leading source of information about IT and business security for hundreds of thousands of professionals worldwide.
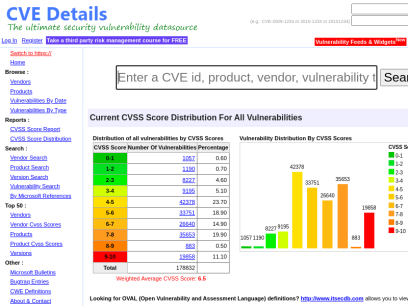
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.

 Qualys.com
Qualys.com
Information Security and Compliance | Qualys
Qualys, Inc. helps your business automate the full spectrum of auditing, compliance and protection of your IT systems and web applications.

 Helpnetsecurity.com
Helpnetsecurity.com
Help Net Security - Information Security News
Information security news with a focus on enterprise security. Discover what matters in the world of cybersecurity today.


 Andreafortuna.org
Andreafortuna.org
Andrea Fortuna | Cybersecurity expert, software developer, experienced digital forensic analyst, musician
Cybersecurity expert, software developer, experienced digital forensic analyst, musician
 Hackertarget.com
Hackertarget.com
28 Online Vulnerability Scanners & Network Tools | HackerTarget.com
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.
 Securityintelligence.com
Securityintelligence.com
Security Intelligence - Cybersecurity Analysis & Insight
The Security Intelligence blog features analysis and insights from hundreds of the brightest minds in the cybersecurity industry.
 Alienvault.com
Alienvault.com
AlienVault is now AT&T Cybersecurity
At AT&T Cybersecurity our mission is to provide phenomenal threat intelligence, collaborative defense & effective security for organizations of all sizes.
 Darkreading.com
Darkreading.com
Dark Reading | Security | Protect The Business
Cyber security's comprehensive news site is now an online community for security professionals, outlining cyber threats and the technologies for defending against them.

 Securityweek.com
Securityweek.com
Cybersecurity News, Insights and Analysis | SecurityWeek
SecurityWeek provides cybersecurity news and information to global enterprises, with expert insights and analysis for IT security professionals.

 Scotthelme.co.uk
Scotthelme.co.uk
Scott Helme
Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on Hacking and Encryption.

 Talosintelligence.com
Talosintelligence.com
Cisco Talos Intelligence Group - Comprehensive Threat Intelligence
Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further harm the internet at large.

 Pi-hole.net
Pi-hole.net
Pi-hole – Network-wide protection
1. Install a supported operating system You can run Pi-hole in a container, or deploy it directly to a supported operating system via our automated installer. Docker install Supported operating systems 2. Install Pi-hole Our intelligent, automated installer asks you a few questions and then sets everything up for you. ...

Technologies Used by sans.edu
Dns Records of sans.edu
A Record: 45.60.103.34 45.60.31.34AAAA Record:
CNAME Record:
NS Record: ns-1058.awsdns-04.org ns-745.awsdns-29.net ns-363.awsdns-45.com ns-1611.awsdns-09.co.uk
SOA Record: awsdns-hostmaster.amazon.com
MX Record: mxb-002c1802.gslb.pphosted.com mxa-002c1802.gslb.pphosted.com
SRV Record:
TXT Record: google-site-verification=dUSOX9p4qG75qf-UfMNmy2Z_aIw_mK-4I5FiWl5Q4co globalsign-domain-verification=b6ff93cac092342acf75ab0ae8bec807 MS=ms72131568 JI6UZuSsLXHEjD7PIBR1rWcPOqRkKRV2VwWAdhXZnLfbjhmfHHOwjMPizS78hfcgbTtjG1TaPTcdVqzgvUbyaw== v=spf1 include:sans.edu._nspf.vali.email include:%{i}._ip.%{h}._ehlo.%{d}._spf.vali.email ip4:205.220.173.71 ip4:205.220.161.71 ~all
DNSKEY Record:
CAA Record: globalsign.com amazon.com sectigo.com letsencrypt.org globalsign.com digicert.com amazon.com mailto:[email protected] sectigo.com
Whois Detail of sans.edu
This Registry database contains ONLY .EDU domains.The data in the EDUCAUSE Whois database is provided
by EDUCAUSE for information purposes in order to
assist in the process of obtaining information about
or related to .edu domain registration records.
The EDUCAUSE Whois database is authoritative for the
.EDU domain.
A Web interface for the .EDU EDUCAUSE Whois Server is
available at: http://whois.educause.edu
By submitting a Whois query, you agree that this information
will not be used to allow, enable, or otherwise support
the transmission of unsolicited commercial advertising or
solicitations via e-mail. The use of electronic processes to
harvest information from this server is generally prohibited
except as reasonably necessary to register or modify .edu
domain names.
-------------------------------------------------------------
Domain Name: SANS.EDU
Registrant:
The Escal Institute for Advanced Technologies, Inc./dba SANS Institute
8120 Woodmont Ave
Suite 310
Bethesda, MD 20814
USA
Administrative Contact:
Domain Admin
The Escal Institute for Advanced Technologies, Inc./dba SANS Institute
8120 Woodmont Ave
Suite 310
Bethesda, MD 20814
USA
+1.13019510102108
[email protected]
Technical Contact:
David Turley
The Escal Institute for Advanced Technologies
11200 Rockville Pike
Suite 200
North Bethesda, MD 20852
USA
+1.3012290777
[email protected]
Name Servers:
NS-363.AWSDNS-45.COM
NS-1058.AWSDNS-04.ORG
NS-1611.AWSDNS-09.CO.UK
NS-745.AWSDNS-29.NET
Domain record activated: 02-Dec-2005
Domain record last updated: 04-Jun-2021
Domain expires: 31-Jul-2024
 151.101.66.49
151.101.66.49
 United States
United States
 Valid SSL
Valid SSL