Shodan Search Engine
Search Engine for the Internet of Things
Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.641903
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 335
Links
ratio 22.248661511005
SSL Details
SSL Issuer:
Issuer: Cloudflare Inc ECC CA-3
Valid From: 2022-05-16 00:00:00
Expiration Date: 2023-05-16 23:59:59
SSL Organization:
Signature d0aad0fb1aaf58d88fdfd40eecd876279b8cb847
Algorithm: ecdsa-with-SHA256
Found 73 Top Alternative to Shodan.io

 Censys.io
Censys.io
Censys | Industry-Leading Cloud and Internet Asset Discovery Solutions
Attack Surface Management and Data Solutions to help your organization discover potential threats, understand cloud-based assets, and help you move fearlessly forward.
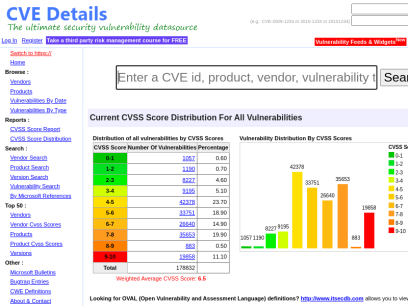
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.
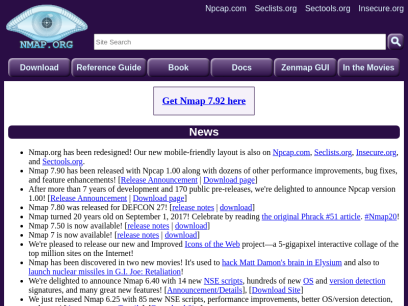
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.

 Kali.org
Kali.org
Kali Linux | Penetration Testing and Ethical Hacking Linux Distribution
Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking and network security assessments.

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.

 Insecam.org
Insecam.org
Insecam - World biggest online cameras directory
Insecam.com - the world biggest directory of online cameras. Watch live street, traffic, parking, office, road, beach, earth online webcams. .

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Wordpress.com
Wordpress.com
WordPress.com: Fast, Secure Managed WordPress Hosting
Create a free website or build a blog with ease on WordPress.com. Dozens of free, customizable, mobile-ready designs and themes. Free hosting and support.

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Asciinema.org
Asciinema.org
asciinema - Record and share your terminal sessions, the simple way
core/ca-certificates-utils 20210603-1 [instal.. │ Last Modified : Mon, 08 Ju core/coreutils 8.32-1 [installed] │ Out Of Date : No core/cracklib 2.9.7-2 [installed] │ core/crda 4.14-4 │ core/cronie 1.5.7-2 │ core/cryptsetup 2.4.0-1 [installed] │ core/curl 7.78.0-1 [installed] │ core/dash 0.5.11.4-1 │ core/db 5.3.28-5 [installed] │ core/dbus 1.12.20-1 [installed] │ core/dbus-docs 1.12.20-1...

 Dnsdumpster.com
Dnsdumpster.com
DNSdumpster.com - dns recon and research, find and lookup dns records
Find dns records in order to identify the Internet footprint of an organization. Recon that enables deeper security assessments and discovery of the attack surface.
 Eccouncil.org
Eccouncil.org
Certified Ethical Hacker | InfoSec Cyber Security Certification | EC-Council
EC-Council is a global leader in InfoSec Cyber Security certification programs like Certified Ethical Hacker and Computer Hacking Forensic Investigator.

 Sans.org
Sans.org
Cyber Security Training | SANS Courses, Certifications & Research
SANS Institute is the most trusted resource for cybersecurity training, certifications and research. Offering more than 60 courses across all practice areas, SANS trains over 40,000 cybersecurity professionals annually.

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.

 Tunnelsup.com
Tunnelsup.com
TunnelsUp - Tools and Information for Network Engineers
Tools, calculator, and helpful information for network engineering, web developers, and IT professionals.
 Hackertarget.com
Hackertarget.com
28 Online Vulnerability Scanners & Network Tools | HackerTarget.com
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.

 Osintframework.com
Osintframework.com
OSINT Framework
I originally created this framework with an information security point of view. Since then, the response from other fields and disciplines has been incredible. I would love to be able to include any other OSINT resources, especially from fields outside of infosec. Please let me know about anything that might...

 Openbugbounty.org
Openbugbounty.org
Free Bug Bounty Program and Coordinated Vulnerability Disclosure | Open Bug Bounty
Report a vulnerability or start a free bug bounty program via Open Bug Bounty vulnerability disclosure platform.

 Vulnhub.com
Vulnhub.com
Vulnerable By Design ~ VulnHub
VulnHub provides materials allowing anyone to gain practical hands-on experience with digital security, computer applications and network administration tasks.

 Nist.gov
Nist.gov
National Institute of Standards and Technology | NIST
NIST promotes U.S. innovation and industrial competitiveness by advancing measurement science, standards, and technology in ways that enhance economic security and improve our quality of life.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers
 Crackstation.net
Crackstation.net
CrackStation - Online Password Hash Cracking - MD5, SHA1, Linux, Rainbow Tables, etc.
Crackstation is the most effective hash cracking service. We crack: MD5, SHA1, SHA2, WPA, and much more...
 Wonderhowto.com
Wonderhowto.com
Wonder How To » Fresh Hacks For a Changing World
Wonder How To is your guide to free how to videos on the Web. Search, Browse and Discover the best how to videos across the web using the largest how to video index on the web. Watch the best online video instructions, tutorials, & How-Tos for free. Have your own how to videos? Submit them to share with the world.
 Base64decode.org
Base64decode.org
Base64 Decode and Encode - Online
Decode from Base64 format or encode into it with various advanced options. Our site has an easy to use online tool to convert your data.
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.

 Detectify.com
Detectify.com
Attack Surface Management Tool Powered By Ethical Hackers | Detectify
Detectify's external attack surface management tool - assess, prioritize, remediate continuously growing external attack surfaces.
 Kalilinuxtutorials.com
Kalilinuxtutorials.com
Kali Linux Tutorials - A Single Stop for Kali Linux Tools
Kali Linux tutorials is an independent platform that covers step by tutorials, advanced penetration testing, Ethical Hacking and network security tools.

 Netsparker.com
Netsparker.com
Invicti | Web Application Security For Enterprise
Get accurate, automated application security testing that scales like no other solution. Secure 1000s of web assets with less manual effort. Reduce your risk with the only…

 Securityonline.info
Securityonline.info
Penetration Testing • Information Security
Securityonline is a huge security community. It is committed to the sharing of high-quality technical articles and safety reports, focusing on high-quality security and security incidents in the industry.
 Kitploit.com
Kitploit.com
KitPloit - PenTest & Hacking Tools
Leading source of security tools, hacking tools, cybersecurity and network security. Learn about new tools and updates in one place.
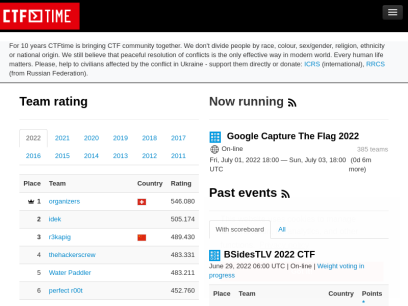
 Ctftime.org
Ctftime.org
CTFtime.org / All about CTF (Capture The Flag)
Capture The Flag, CTF teams, CTF ratings, CTF archive, CTF writeups

 Angryip.org
Angryip.org
Angry IP Scanner - the original IP scanner for Windows, Mac and Linux
The original IP scanner for Windows, Max and Linux. Fast, friendly, extensible, free and open-source. Scans addresses and ports in any range and exports results in many formats.

 Darknet.org.uk
Darknet.org.uk
Darknet - Hacking Tools, Hacker News & Cyber Security
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.

 Any.run
Any.run
ANY.RUN - Interactive Online Malware Sandbox
Cloud-based malware analysis service. Take your information security to the next level. Analyze suspicious and malicious activities using our innovative tools.

 Binaryedge.io
Binaryedge.io
BinaryEdge
We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning.

 Pentester.land
Pentester.land
Pentester Land · Offensive Infosec
The newsletter is dead, long live the newsletter! 12 Jul 2020 • newsletter This is a long due post. Since The 5 Hacking Newsletter has stopped on this blog, I’ve been getting many questions about it. So, even though most readers already know by now, here’s a summary of what...

 Kaliboys.com
Kaliboys.com
جامع ترین منبع آموزشی کامپیوتر و زیرشاخه های آن - وب سایت کالی بویز
کالی بویز جامع ترین منبع آموزشی کامپیوتر و زیر شاخه های آن مانند شبکه ، برنامه نویسی ، امنیت و ... که از شما یک مهندس تمام عیار می سازد.

 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies


 Md5decrypt.net
Md5decrypt.net
Md5 Decryption & Encryption Gratuite - Plus de 15.000.000.000 hashs
Decryption Md5 : Le Md5 (Message Digest 5) est une fonction cryptographique qui permet de "hasher" (encrypter) une séquence numérique en un hash md5 de 128 bits, soit 32 caractères, et ce peu importe la longueur de la séquence originale. Ce système cryptographique est irréversible, il n'est pas possible d'obtenir...

 Veracode.com
Veracode.com
Confidently secure apps you build and manage with Veracode
This simple and scalable solution enables you to create more secure software so that you can boost your business and reduce risk without hindering innovation.
 Wireshark.org
Wireshark.org
Wireshark · Go Deep.
Download Get Started Now Learn Knowledge is Power Go Beyond With Wireshark Sponsors About Wireshark About Awards and Accolades Authors Wireshark Sponsors Wireshark is the world’s foremost and widely-used network protocol analyzer. It lets you see what’s happening on your network at a microscopic level and is the de facto...
 Debian.org
Debian.org
Debian -- The Universal Operating System
The Community Debian is a Community of People! Mini DebConf Regensburg 2021 DC19 Group Photo Screenshot Calamares Installer Debian is like a Swiss Army Knife People have fun with Debian People Who we are and what we do Our Philosophy Why we do it, and how we do it Get...

 Pentestmonkey.net
Pentestmonkey.net
pentestmonkey | Taking the monkey work out of pentesting
mimikatz: Tool To Recover Cleartext Passwords From Lsass December 20, 2011, pentestmonkey I meant to blog about this a while ago, but never got round to it. Here’s a brief post about very cool feature of a tool called mimikatz. I’m very grateful to the tool’s author for bringing it...
 Cryptii.com
Cryptii.com
Modular conversion, encoding and encryption online — Cryptii
Web app offering modular conversion, encoding and encryption online. Translations are done in the browser without any server interaction. This is an Open Source project, code licensed MIT.
 Cybrary.it
Cybrary.it
Free Cybersecurity Training and Career Development | Cybrary
Cybersecurity training from Cybrary will take your career to the next level. We have the cybersecurity courses that can help get you there!
 Alienvault.com
Alienvault.com
AlienVault is now AT&T Cybersecurity
At AT&T Cybersecurity our mission is to provide phenomenal threat intelligence, collaborative defense & effective security for organizations of all sizes.
 Md5online.org
Md5online.org
MD5 Online | Free and fast MD5 encryption
MD5Online offers a free and fast tool to generate an MD5 hash from a word of your choice
 Blackmoreops.com
Blackmoreops.com
Linux, InfoSec, Hacking - blackMORE Ops
blackMORE Ops is the leading source for Kali Linux, InfoSec, Hacking, Network and Cyber Security, How to, Guides and Tutorials with technical details.

 Defcon.org
Defcon.org
DEF CON® Hacking Conference Home
The largest hacking and security conference with presentations, workshops, contests, villages and the premier Capture The Flag Contest.
 0day.today
0day.today
0day.today Agreement - 0day.today Exploit Database : vulnerability : 0day : new exploits : buy and sell private exploit : shellcode by 0day Today Team
0day Today is the ultimate database of exploits and vulnerabilities and a great resource for vulnerability researchers and security professionals. Our aim is to collect exploits from submittals and various mailing lists and concentrate them in one, easy-to-navigate database. This was written solely for educational purposes. Use it...
Technologies Used by shodan.io
Dns Records of shodan.io
A Record: 104.18.12.238 104.18.13.238AAAA Record: 2606:4700::6812:cee 2606:4700::6812:dee
CNAME Record:
NS Record: lady.ns.cloudflare.com ed.ns.cloudflare.com
SOA Record: dns.cloudflare.com
MX Record: alt1.aspmx.l.google.com alt2.aspmx.l.google.com aspmx.l.google.com
SRV Record:
TXT Record: v=spf1 ip4:216.117.2.180 ip4:69.72.37.146 include:_spf.google.com -all google-site-verification=BzXlMuKdXSAiX3v-VUo-M_ZZ1VPW3cwptvaIOWWGQ7c MS=87251D03D1B817A70CC370D9FF17FFB7325A0110
DNSKEY Record:
CAA Record:
Whois Detail of shodan.io
Domain Name: shodan.ioRegistry Domain ID: UNDEF-ROID
Registrar WHOIS Server: whois.gandi.net
Registrar URL: http://www.gandi.net
Updated Date: 2022-05-24T01:08:22Z
Creation Date: 2012-08-22T01:02:54Z
Registrar Registration Expiration Date: 2022-08-22T03:02:54Z
Registrar: GANDI SAS
Registrar IANA ID: 81
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +33.170377661
Reseller:
Domain Status: ok http://www.icann.org/epp#ok
Domain Status:
Domain Status:
Domain Status:
Domain Status:
Registry Registrant ID: REDACTED FOR PRIVACY
Registrant Name: REDACTED FOR PRIVACY
Registrant Organization:
Registrant Street: 63-65 boulevard Massena
Registrant City: Paris
Registrant State/Province: Paris
Registrant Postal Code: 75013
Registrant Country: FR
Registrant Phone: +33.170377666
Registrant Phone Ext:
Registrant Fax: +33.143730576
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID: REDACTED FOR PRIVACY
Admin Name: REDACTED FOR PRIVACY
Admin Organization:
Admin Street: 63-65 boulevard Massena
Admin City: Paris
Admin State/Province: Paris
Admin Postal Code: 75013
Admin Country: FR
Admin Phone: +33.170377666
Admin Phone Ext:
Admin Fax: +33.143730576
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID: REDACTED FOR PRIVACY
Tech Name: REDACTED FOR PRIVACY
Tech Organization:
Tech Street: 63-65 boulevard Massena
Tech City: Paris
Tech State/Province: Paris
Tech Postal Code: 75013
Tech Country: FR
Tech Phone: +33.170377666
Tech Phone Ext:
Tech Fax: +33.143730576
Tech Fax Ext:
Tech Email: [email protected]
Name Server: ED.NS.CLOUDFLARE.COM
Name Server: LADY.NS.CLOUDFLARE.COM
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
DNSSEC: signedDelegation
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-06-15T19:56:58Z <<<
For more information on Whois status codes, please visit
https://www.icann.org/epp
Reseller Email:
Reseller URL:
Personal data access and use are governed by French law, any use for the purpose of unsolicited mass commercial advertising as well as any mass or automated inquiries (for any intent other than the registration or modification of a domain name) are strictly forbidden. Copy of whole or part of our database without Gandi's endorsement is strictly forbidden.
A dispute over the ownership of a domain name may be subject to the alternate procedure established by the Registry in question or brought before the courts.
For additional information, please contact us via the following form:
https://www.gandi.net/support/contacter/mail/
 104.26.10.245
104.26.10.245
 United States
United States
 Valid SSL
Valid SSL