Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time:
SSL: Disable
Status: up
Code To Txt Ratio
Word Count
Links
ratio
Found 32 Top Alternative to Cert.org
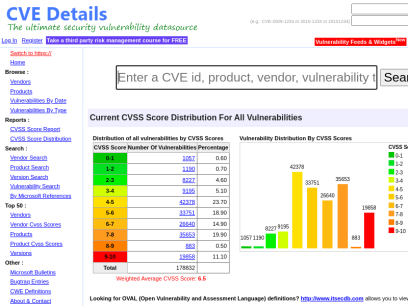
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Fortiguard.com
Fortiguard.com
FortiGuard
View by Product Network Intrusion Protection Anti-Recon and Anti-Exploit Secure DNS IP Reputation/Anti-Botnet Indicators of Compromise IP Geolocation Service Cloud Workload Security Service Content and Endpoint Endpoint Detection & Response Anti-Virus Endpoint Vulnerability Device Detection ANN and NDR Sandbox Behavior Engine Application Web Filtering Anti-Spam Application Control Industrial Security Services...

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Us-cert.gov
Us-cert.gov
Homepage | CISA
As part of its mission, CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Vulmon.com
Vulmon.com
Vulmon - Vulnerability Intelligence Search Engine
Vulmon is a vulnerability and exploit search engine with vulnerability intelligence features.

 Cisa.gov
Cisa.gov
Homepage | CISA
CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.

 Securityaffairs.co
Securityaffairs.co
Security Affairs - Read, think, share … Security is everyone's responsibilitySecurity Affairs
Security Affairs - Every security issue is our affair. Read, think, share … Security is everyone's responsibility

 Security-database.com
Security-database.com
Security Database
Security-Database help your corporation foresee and avoid any security risks that may impact your IT infrastructure and business applications.

 Ixiacom.com
Ixiacom.com
Network Visibility and Network Test Products | Keysight
Use Ixia (Keysight) market-leading network test, visibility, performance monitoring, and security solutions to build and manage more secure, and reliable networks.

 Cmmiinstitute.com
Cmmiinstitute.com
CMMI Institute - Home
What is CMMI? For 25+ years, high-performing organizations have achieved clear, sustainable business results with ISACA®’s CMMI® maturity models. Originally created for the U.S. Department of Defense to assess the quality and capability of their software contractors, ISACA’s CMMI models have expanded beyond software engineering to help organizations around the...

 Snort.org
Snort.org
Snort - Network Intrusion Detection & Prevention System
Snort is an open-source, free and lightweight network intrusion detection system (NIDS) software for Linux and Windows to detect emerging threats.

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...

 Circl.lu
Circl.lu
CIRCL » CIRCL -- Computer Incident Response Center Luxembourg -- CSIRT -- CERT
The Computer Incident Response Center Luxembourg (CIRCL) is a government-driven initiative designed to gather, review, report and respond to computer security threats and incidents. CIRCL is the CERT (Computer Emergency Response Team/Computer Security Incident Response Team) for the private sector, communes and non-governmental entities in Luxembourg.

 Securityweek.com
Securityweek.com
Cybersecurity News, Insights and Analysis | SecurityWeek
SecurityWeek provides cybersecurity news and information to global enterprises, with expert insights and analysis for IT security professionals.

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.

 Threatpost.com
Threatpost.com
Threatpost | The first stop for security news
Threatpost, is an independent news site which is a leading source of information about IT and business security for hundreds of thousands of professionals worldwide.

 Seclists.org
Seclists.org
SecLists.Org Security Mailing List Archive
Security mailing list archive for the Nmap lists, Bugtraq, Full Disclosure, Security Basics, Pen-test, and dozens more. Search capabilities and RSS feeds with smart excerpts are available

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers

 Coresecurity.com
Coresecurity.com
Core Security | Cyber Threat Prevention & Identity Governance
Contact Us Support All HelpSystems Products FREE TRIALS Contact Us Support All HelpSystems Products FREE TRIALS Cyber Threat Toggle Dropdown Products Core Impact Penetration testing software Cobalt Strike Red team software Event Manager Security information and event management Network Insight Network Traffic Analysis Powertech Antivirus Server-level virus protection Security Auditor...

Technologies Used by cert.org
Dns Records of cert.org
A Record: 147.72.252.242AAAA Record:
CNAME Record:
NS Record: ns2.sei.cmu.edu ns1.sei.cmu.edu
SOA Record: hostmaster.cert.org
MX Record: northridge.red.cert.org brick.red.cert.org
SRV Record:
TXT Record: v=spf1 ip4:147.72.252.0/27 include:spf.protection.office365.us ?all MS=ms99326395 GjlKiHz4O+yqufLrRIiCkmyaNeKDsFtlP0EdfJ5Hd0ERRCB3rBFfT0hjRz5KpuVbK7z1iW6Vh6MtnSK/dHi1Lg== google-site-verification=XOhFzgbzrxnwXF_zY4WWTJSkIyRfIjEI8eaOJCx4WiI
DNSKEY Record:
CAA Record: mailto:[email protected] comodoca.com ;
Whois Detail of cert.org
Domain Name: cert.orgRegistry Domain ID: 635b6cec75e04b3fa5b765d4c35b4ffa-LROR
Registrar WHOIS Server: whois.networksolutions.com
Registrar URL: http://www.networksolutions.com
Updated Date: 2021-12-30T19:30:21Z
Creation Date: 1991-12-31T05:00:00Z
Registry Expiry Date: 2031-12-30T05:00:00Z
Registrar: Network Solutions, LLC
Registrar IANA ID: 2
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.8777228662
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Registry Registrant ID: REDACTED FOR PRIVACY
Registrant Name: REDACTED FOR PRIVACY
Registrant Organization: Software Engineering Institute - CMU
Registrant Street: REDACTED FOR PRIVACY
Registrant City: REDACTED FOR PRIVACY
Registrant State/Province: PA
Registrant Postal Code: REDACTED FOR PRIVACY
Registrant Country: US
Registrant Phone: REDACTED FOR PRIVACY
Registrant Phone Ext: REDACTED FOR PRIVACY
Registrant Fax: REDACTED FOR PRIVACY
Registrant Fax Ext: REDACTED FOR PRIVACY
Registrant Email: Please query the RDDS service of the Registrar of Record identified in this output for information on how to contact the Registrant, Admin, or Tech contact of the queried domain name.
Registry Admin ID: REDACTED FOR PRIVACY
Admin Name: REDACTED FOR PRIVACY
Admin Organization: REDACTED FOR PRIVACY
Admin Street: REDACTED FOR PRIVACY
Admin City: REDACTED FOR PRIVACY
Admin State/Province: REDACTED FOR PRIVACY
Admin Postal Code: REDACTED FOR PRIVACY
Admin Country: REDACTED FOR PRIVACY
Admin Phone: REDACTED FOR PRIVACY
Admin Phone Ext: REDACTED FOR PRIVACY
Admin Fax: REDACTED FOR PRIVACY
Admin Fax Ext: REDACTED FOR PRIVACY
Admin Email: Please query the RDDS service of the Registrar of Record identified in this output for information on how to contact the Registrant, Admin, or Tech contact of the queried domain name.
Registry Tech ID: REDACTED FOR PRIVACY
Tech Name: REDACTED FOR PRIVACY
Tech Organization: REDACTED FOR PRIVACY
Tech Street: REDACTED FOR PRIVACY
Tech City: REDACTED FOR PRIVACY
Tech State/Province: REDACTED FOR PRIVACY
Tech Postal Code: REDACTED FOR PRIVACY
Tech Country: REDACTED FOR PRIVACY
Tech Phone: REDACTED FOR PRIVACY
Tech Phone Ext: REDACTED FOR PRIVACY
Tech Fax: REDACTED FOR PRIVACY
Tech Fax Ext: REDACTED FOR PRIVACY
Tech Email: Please query the RDDS service of the Registrar of Record identified in this output for information on how to contact the Registrant, Admin, or Tech contact of the queried domain name.
Name Server: ns1.sei.cmu.edu
Name Server: ns2.sei.cmu.edu
DNSSEC: unsigned
URL of the ICANN Whois Inaccuracy Complaint Form: https://www.icann.org/wicf/
>>> Last update of WHOIS database: 2022-08-29T02:05:31Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
Terms of Use: Access to Public Interest Registry WHOIS information is provided to assist persons in determining the contents of a domain name registration record in the Public Interest Registry registry database. The data in this record is provided by Public Interest Registry for informational purposes only, and Public Interest Registry does not guarantee its accuracy. This service is intended only for query-based access. You agree that you will use this data only for lawful purposes and that, under no circumstances will you use this data to (a) allow, enable, or otherwise support the transmission by e-mail, telephone, or facsimile of mass unsolicited, commercial advertising or solicitations to entities other than the data recipient's own existing customers; or (b) enable high volume, automated, electronic processes that send queries or data to the systems of Registry Operator, a Registrar, or Donuts except as reasonably necessary to register domain names or modify existing registrations. All rights reserved. Public Interest Registry reserves the right to modify these terms at any time. By submitting this query, you agree to abide by this policy. The Registrar of Record identified in this output may have an RDDS service that can be queried for additional information on how to contact the Registrant, Admin, or Tech contact of the queried domain name.
 104.18.23.245
104.18.23.245
 United States
United States
 Valid SSL
Valid SSL