Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language:
Response Time:
SSL: Disable
Status: up
Code To Txt Ratio
Word Count
Links
ratio
Found 77 Top Alternative to Ibmcloud.com

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers
 Securityintelligence.com
Securityintelligence.com
Security Intelligence - Cybersecurity Analysis & Insight
The Security Intelligence blog features analysis and insights from hundreds of the brightest minds in the cybersecurity industry.

 Capacitorjs.com
Capacitorjs.com
Capacitor - build cross platform apps with the web
Build iOS, Android, and Progressive Web Apps with HTML, CSS, and JavaScript


 Db-ip.com
Db-ip.com
IP Geolocation API & Free Address Database | DB-IP
From basic IP address to location to detailed cyber threat analysis, the DB-IP Geolocation API and database offer superior accuracy and performance. Learn more about our API and database here when you visit our website and get what you need with our free downloads today.
 Alienvault.com
Alienvault.com
AlienVault is now AT&T Cybersecurity
At AT&T Cybersecurity our mission is to provide phenomenal threat intelligence, collaborative defense & effective security for organizations of all sizes.

 Fortiguard.com
Fortiguard.com
FortiGuard
View by Product Network Intrusion Protection Anti-Recon and Anti-Exploit Secure DNS IP Reputation/Anti-Botnet Indicators of Compromise IP Geolocation Service Cloud Workload Security Service Content and Endpoint Endpoint Detection & Response Anti-Virus Endpoint Vulnerability Device Detection ANN and NDR Sandbox Behavior Engine Application Web Filtering Anti-Spam Application Control Industrial Security Services...
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Abuseipdb.com
Abuseipdb.com
AbuseIPDB - IP address abuse reports - Making the Internet safer, one IP at a time
Check an IP Address, Domain Name, or Subnet e.g. 38.242.237.160, microsoft.com, or 5.188.10.0/24 Check AbuseIPDB making the internet safer, one IP at a time Report abusive IPs engaging in hacking attempts or other malicious behavior and help fellow sysadmins! Report IP Now Check the report history of any IP address...

 Securityaffairs.co
Securityaffairs.co
Security Affairs - Read, think, share … Security is everyone's responsibilitySecurity Affairs
Security Affairs - Every security issue is our affair. Read, think, share … Security is everyone's responsibility

 Coresecurity.com
Coresecurity.com
Core Security | Cyber Threat Prevention & Identity Governance
Contact Us Support All HelpSystems Products FREE TRIALS Contact Us Support All HelpSystems Products FREE TRIALS Cyber Threat Toggle Dropdown Products Core Impact Penetration testing software Cobalt Strike Red team software Event Manager Security information and event management Network Insight Network Traffic Analysis Powertech Antivirus Server-level virus protection Security Auditor...
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.


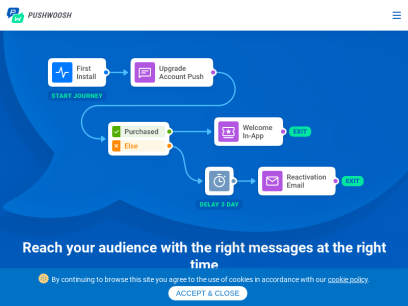
 Pushwoosh.com
Pushwoosh.com
Pushwoosh – №1 push notification and cross-channel marketing service
Boost user engagement and revenue with new digital marketing strategies employing push notifications, in-app messages, and more

 Myip.ms
Myip.ms
My IP Address - Shows IPv4 & IPv6 | Blacklist IP Check - Hosting Info
Shows Your IPv4 & IPv6, OS, Browser, Organisation, Country on Interactive Map. Live Hosting Information on where any website is hosted on the internet and other information about IP address owners. Online Blacklist your IP Check (Real-time DB). Web Bots 2022 List

 Abongo.com
Abongo.com
Webmaster Tools and Investigative Reports
Free Webmaster Tools and Investigative Reports including enhanced DNS, Provider, Whois, World Ping, Tracert and more from thirteen locations around the world.

 Threatpost.com
Threatpost.com
Threatpost | The first stop for security news
Threatpost, is an independent news site which is a leading source of information about IT and business security for hundreds of thousands of professionals worldwide.

 Circl.lu
Circl.lu
CIRCL » CIRCL -- Computer Incident Response Center Luxembourg -- CSIRT -- CERT
The Computer Incident Response Center Luxembourg (CIRCL) is a government-driven initiative designed to gather, review, report and respond to computer security threats and incidents. CIRCL is the CERT (Computer Emergency Response Team/Computer Security Incident Response Team) for the private sector, communes and non-governmental entities in Luxembourg.

 Tracemyip.org
Tracemyip.org
Trace My IP | IP Address Tracker | IP Tracer | Computer Hardware IP Visitor Location
Track and trace website visitors IPs. Trace people and map their device IP location with computer IP address visitor location tracker

 Seclists.org
Seclists.org
SecLists.Org Security Mailing List Archive
Security mailing list archive for the Nmap lists, Bugtraq, Full Disclosure, Security Basics, Pen-test, and dozens more. Search capabilities and RSS feeds with smart excerpts are available

 Snort.org
Snort.org
Snort - Network Intrusion Detection & Prevention System
Snort is an open-source, free and lightweight network intrusion detection system (NIDS) software for Linux and Windows to detect emerging threats.

 Jazz.net
Jazz.net
Jazz Community Site
IBM's Engineering Lifecycle Management products are supported by the Jazz Community Site, helping you you manage requirements, quality and changes, and improve project planning and tracking.

 Us-cert.gov
Us-cert.gov
Homepage | CISA
As part of its mission, CISA leads the effort to enhance the security, resiliency, and reliability of the Nation's cybersecurity and communications infrastructure.

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.
 Scmagazine.com
Scmagazine.com
SC Media | Homepage
The latest in-depth, unbiased news, analysis and perspective to keep cybersecurity professionals informed, educated and enlightened about the market.

 Esecurityplanet.com
Esecurityplanet.com
eSecurity Planet: Latest Cybersecurity News for IT Professionals
eSecurity Planet provides the latest cybersecurity news, trends, and software reviews for IT leaders. Browse our buyer's guides and analysis now.


 Any.run
Any.run
ANY.RUN - Interactive Online Malware Sandbox
Cloud-based malware analysis service. Take your information security to the next level. Analyze suspicious and malicious activities using our innovative tools.

 Onesignal.com
Onesignal.com
Push Notification Software to Improve Customer Engagement - OneSignal
The world’s leader for customer messaging including mobile push notifications, web push, SMS, email & in-app messaging. Trusted by 1 million+ developers.

 Urlscan.io
Urlscan.io
URL and website scanner - urlscan.io
urlscan.io - Website scanner for suspicious and malicious URLs

 Mybluemix.net
Mybluemix.net
IBM Cloud Docs
Find documentation, API & SDK references, tutorials, FAQs, and more resources for IBM Cloud products and services.

 Dnslytics.com
Dnslytics.com
Online investigation tool - Reverse IP, NS, MX, WHOIS and Search Tools
DNSlytics provides the ultimate online investigation tool. See detailed information about every IP address, domain name and provider. Perform network tests like DNS lookup, email testing and WHOIS lookups.

 Carbonblack.com
Carbonblack.com
VMware Security Solutions
Deliver security that’s built-in & distributed with your control points of users, devices, workloads & network, with fewer tools & silos, & better context.

 Crowdstrike.com
Crowdstrike.com
CrowdStrike: Stop breaches. Drive business.
CrowdStrike is a global cybersecurity leader with an advanced cloud-native platform for protecting endpoints, cloud workloads, identities and data.

 Joshmorony.com
Joshmorony.com
Blog | Josh Morony - Learn how to build mobile apps with web tech
Learn how to build apps with web tech

 Cleantalk.org
Cleantalk.org
Anti-Spam Plugins for WordPress, Joomla, Drupal, and any other websites
Cloud Anti-Spam Service for websites. Protect your website from spam with invisible methods for visitors. No Captcha, no questions, no counting animals, no puzzles, no math. Fight spam!

 Whois.com
Whois.com
Whois.com - Domain Names & Identity for Everyone
Get verified Whois information for any Domain Name, Check Domain Availability for FREE! Register Domain Names at best prices and host your own website.
 Darkreading.com
Darkreading.com
Dark Reading | Security | Protect The Business
Cyber security's comprehensive news site is now an online community for security professionals, outlining cyber threats and the technologies for defending against them.

 Securityweek.com
Securityweek.com
Cybersecurity News, Insights and Analysis | SecurityWeek
SecurityWeek provides cybersecurity news and information to global enterprises, with expert insights and analysis for IT security professionals.

 Anomali.com
Anomali.com
Intelligence-Driven Cybersecurity for the Enterprise - Anomali
Anomali delivers solutions that enable businesses to gain unlimited threat visibility, speed time to detection, and improve security operations productivity.

 Threatminer.org
Threatminer.org
ThreatMiner.org | Data Mining for Threat Intelligence
ThreatMiner is a threat intelligence portal that provides information on indicators of compromise (IOC) such as domains, IP address, malware samples (MD5, SHA1 and SHA256), SSL certificates, WHOIS information and malicious URLs such as phishing and malware links.

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.
 Enappd.com
Enappd.com
Enappd | Ionic, React Native, Firebase, Vue, Flutter App themes, templates and starters
We create awesome Ionic, React Native, flutter, vue and firebase starters to save thousands of dollars of development cost

 Bgpview.io
Bgpview.io
BGPView - BGP Toolkit and BGP ASN Routing Lookup Tool
BGPView allows you to debug and investigate information about IP addresses, ASN, IXs, BGP, ISPs, Prefixes and Domain names.

 Talosintelligence.com
Talosintelligence.com
Cisco Talos Intelligence Group - Comprehensive Threat Intelligence
Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further harm the internet at large.

 Cyware.com
Cyware.com
Threat Intelligence Solution Company | Cyber Security Products | Cyber Security Operations Center | Cyware
Cyber Security Products - Cyware offers innovative, real-time cyber fusion solutions for Strategic and Tactical Threat Intelligence Sharing, Threat Response and Security Automation. Get a Demo Now!

 Monaca.io
Monaca.io
Cloud-Powered HTML5 Hybrid Mobile App Development Tools | Monaca
Monaca makes hybrid app development with Cordova a lot easier with its comprehensive cloud-powered mobile app development tools and services.

 Evothings.com
Evothings.com
Evothings | Making mobile apps for IoT easy, fast and fun to build!
Start page Evothings Studio retires Dear dev community, this note should’ve been written some time ago, when the mobile market was far more heterogenous than today, and when there were considerably fewer frameworks serving non-native developers. Evothings Studio is officially no longer supported and has in its commercial form not...

 Vulmon.com
Vulmon.com
Vulmon - Vulnerability Intelligence Search Engine
Vulmon is a vulnerability and exploit search engine with vulnerability intelligence features.
 0day.today
0day.today
0day.today Agreement - 0day.today Exploit Database : vulnerability : 0day : new exploits : buy and sell private exploit : shellcode by 0day Today Team
0day Today is the ultimate database of exploits and vulnerabilities and a great resource for vulnerability researchers and security professionals. Our aim is to collect exploits from submittals and various mailing lists and concentrate them in one, easy-to-navigate database. This was written solely for educational purposes. Use it...
Technologies Used by ibmcloud.com
Dns Records of ibmcloud.com
A Record: 129.42.38.1AAAA Record:
CNAME Record:
NS Record: asia3.akam.net usc3.akam.net usc2.akam.net usw2.akam.net eur5.akam.net ns1-99.akam.net eur2.akam.net ns1-206.akam.net
SOA Record: hostmaster.akamai.com
MX Record: qdms-mail.ibmcloud.com
SRV Record:
TXT Record:
DNSKEY Record:
CAA Record:
Whois Detail of ibmcloud.com
Domain Name: ibmcloud.com
Registry Domain ID: 1550862406_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.corporatedomains.com
Registrar URL: www.cscprotectsbrands.com
Updated Date: 2022-03-28T01:14:35Z
Creation Date: 2009-04-01T03:17:35Z
Registrar Registration Expiration Date: 2023-04-01T07:17:35Z
Registrar: CSC CORPORATE DOMAINS, INC.
Sponsoring Registrar IANA ID: 299
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.8887802723
Domain Status: clientTransferProhibited http://www.icann.org/epp#clientTransferProhibited
Registry Registrant ID:
Registrant Name: IBM DNS Admin
Registrant Organization: International Business Machines Corporation
Registrant Street: New Orchard Road
Registrant City: Armonk
Registrant State/Province: NY
Registrant Postal Code: 10504
Registrant Country: US
Registrant Phone: +1.9147654227
Registrant Phone Ext:
Registrant Fax: +1.914765437
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: IBM Corporation
Admin Organization: International Business Machines (IBM)
Admin Street: New Orchard Road
Admin City: Armonk
Admin State/Province: NY
Admin Postal Code: 10598
Admin Country: US
Admin Phone: +1.9147654227
Admin Phone Ext:
Admin Fax: +1.9147654370
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID:
Tech Name: IBM DNS Technical
Tech Organization: IBM Corporation
Tech Street: New Orchard Road
Tech City: Armonk
Tech State/Province: NY
Tech Postal Code: 10504
Tech Country: US
Tech Phone: +1.9192544441
Tech Phone Ext:
Tech Fax: +1.914765437
Tech Fax Ext:
Tech Email: [email protected]
Name Server: ns1-99.akam.net
Name Server: eur5.akam.net
Name Server: asia3.akam.net
Name Server: ns1-206.akam.net
Name Server: usw2.akam.net
Name Server: usc3.akam.net
Name Server: usc2.akam.net
Name Server: eur2.akam.net
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-03-28T01:14:35Z <<<
For more information on Whois status codes, please visit https://icann.org/epp
Corporation Service Company(c) (CSC) The Trusted Partner of More than 50% of the 100 Best Global Brands.
Contact us to learn more about our enterprise solutions for Global Domain Name Registration and Management, Trademark Research and Watching, Brand, Logo and Auction Monitoring, as well SSL Certificate Services and DNS Hosting.
NOTICE: You are not authorized to access or query our WHOIS database through the use of high-volume, automated, electronic processes or for the purpose or purposes of using the data in any manner that violates these terms of use. The Data in the CSC WHOIS database is provided by CSC for information purposes only, and to assist persons in obtaining information about or related to a domain name registration record. CSC does not guarantee its accuracy. By submitting a WHOIS query, you agree to abide by the following terms of use: you agree that you may use this Data only for lawful purposes and that under no circumstances will you use this Data to: (1) allow, enable, or otherwise support the transmission of mass unsolicited, commercial advertising or solicitations via direct mail, e-mail, telephone, or facsimile; or (2) enable high volume, automated, electronic processes that apply to CSC (or its computer systems). CSC reserves the right to terminate your access to the WHOIS database in its sole discretion for any violations by you of these terms of use. CSC reserves the right to modify these terms at any time.
Register your domain name at http://www.cscglobal.com
 170.226.62.35
170.226.62.35
 United States
United States
 InValid
SSL
InValid
SSL