Core Security | Cyber Threat Prevention & Identity Governance
Contact Us Support All HelpSystems Products FREE TRIALS Contact Us Support All HelpSystems Products FREE TRIALS Cyber Threat Toggle Dropdown Products Core Impact Penetration testing software Cobalt Strike Red team software Event Manager Security information and event management Network Insight Network Traffic Analysis Powertech Antivirus Server-level virus protection Security Auditor...

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.28323
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 798
Links
ratio 30.895181097027
SSL Details
SSL Issuer:
Issuer: R3
Valid From: 2022-05-22 10:14:41
Expiration Date: 2022-08-20 10:14:40
SSL Organization:
Signature 16ba6bc59c4b9eef46b84f8d363bede187188a58
Algorithm: RSA-SHA256
Found 74 Top Alternative to Coresecurity.com

 Redteamsecure.com
Redteamsecure.com
Offensive Security by RedTeam Security
RedTeam Security uncovers and identifies offensive security risks. We find malicious attacks before they find you. Call our security experts 952-836-2770

 Veracode.com
Veracode.com
Confidently secure apps you build and manage with Veracode
This simple and scalable solution enables you to create more secure software so that you can boost your business and reduce risk without hindering innovation.

 Fortiguard.com
Fortiguard.com
FortiGuard
View by Product Network Intrusion Protection Anti-Recon and Anti-Exploit Secure DNS IP Reputation/Anti-Botnet Indicators of Compromise IP Geolocation Service Cloud Workload Security Service Content and Endpoint Endpoint Detection & Response Anti-Virus Endpoint Vulnerability Device Detection ANN and NDR Sandbox Behavior Engine Application Web Filtering Anti-Spam Application Control Industrial Security Services...
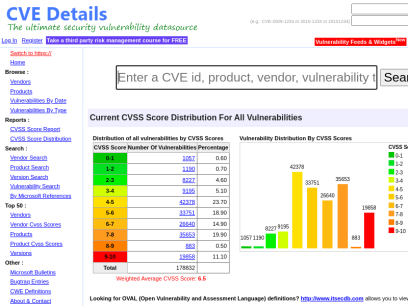
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.

 Itgovernance.co.uk
Itgovernance.co.uk
IT Governance - Governance, Risk Management and Compliance for Information Technology
The one-stop-shop for cyber security and data privacy risk management solutions.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Cyberdegrees.org
Cyberdegrees.org
Explore Cybersecurity Degrees and Careers | CyberDegress.org
Learn about cybersecurity degree options and career paths. Browse our comprehensive directory of online and on-campus cyber degrees across the U.S.

 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Rhinosecuritylabs.com
Rhinosecuritylabs.com
Penetration Testing Company, Network & Web Application Pen Test
Rhino Security Labs is a top penetration testing company specializing in cloud (AWS, GCP, Azure), network pentesting, and webapp pentesting in Seattle.

 Cyberark.com
Cyberark.com
Identity Security and Access Management Leader | CyberArk
Get the most complete Identity Security and Access Management Solutions that enable secure access across any device, anywhere, at just the right time.
 Alpinesecurity.com
Alpinesecurity.com
We Help You Stop Cyberattacks with Cybersecurity Consulting & Training
Medical device and heathcare cybersecurity assessment and testing, penetration testing, cybersecurity certification training, CISO as a Service (CaaS).

 Pentestpartners.com
Pentestpartners.com
Cyber Security Consulting & Testing | Pen Test Partners
Cyber Security Services | CREST, CBEST, ASSURE, STAR, CSIR, & VA | CHECK | Tigerscheme | PCI QSA | ISO27001


 Giac.org
Giac.org
Cyber Security Certifications | GIAC Certifications
GIAC Certifications develops and administers premier, professional information security certifications. More than 30 certifications align with SANS training and ensure mastery in critical, specialized InfoSec domains. GIAC certifications provide the highest and most rigorous assurance of cyber security knowledge and skill available to industry, government, and military clients across the world.
 Metasploit.com
Metasploit.com
Metasploit | Penetration Testing Software, Pen Testing Security | Metasploit
Find security issues, verify vulnerability mitigations & manage security assessments with Metasploit. Get the world's best penetration testing software now.

 Blackhat.com
Blackhat.com
Black Hat | Home
Black Hat Webinars Security Research in Real Time June 30, 2022 - Managing Cybersecurity as a Business Risk July 14, 2022 - InfoSec Lessons from the War in Ukraine Sponsor a Webinars View all of our recent Webinars Black Hat Archives Watch Past Presentations View all of our archived videos...

 Pentestlab.blog
Pentestlab.blog
Penetration Testing Lab – Offensive Techniques & Methodologies
Offensive Techniques & Methodologies

 Cobalt.io
Cobalt.io
Pentest as a Service | Cobalt
Cobalt is modernizing traditional pentesting. We leverage global talent and a SaaS platform to deliver a better pentest via Pentest as a Service (PtaaS).

 Helpnetsecurity.com
Helpnetsecurity.com
Help Net Security - Information Security News
Information security news with a focus on enterprise security. Discover what matters in the world of cybersecurity today.

 0day.today
0day.today
0day.today Agreement - 0day.today Exploit Database : vulnerability : 0day : new exploits : buy and sell private exploit : shellcode by 0day Today Team
0day Today is the ultimate database of exploits and vulnerabilities and a great resource for vulnerability researchers and security professionals. Our aim is to collect exploits from submittals and various mailing lists and concentrate them in one, easy-to-navigate database. This was written solely for educational purposes. Use it...

 Pcisecuritystandards.org
Pcisecuritystandards.org
Official PCI Security Standards Council Site - Verify PCI Compliance, Download Data Security and Credit Card Security Standards
If you are a merchant of any size accepting credit cards, you must be in compliance with PCI Security Council standards. This site provides: credit card data security standards documents, PCIcompliant software and hardware, qualified security assessors, technical support, merchant guides and more.
 Securityintelligence.com
Securityintelligence.com
Security Intelligence - Cybersecurity Analysis & Insight
The Security Intelligence blog features analysis and insights from hundreds of the brightest minds in the cybersecurity industry.
 Darkreading.com
Darkreading.com
Dark Reading | Security | Protect The Business
Cyber security's comprehensive news site is now an online community for security professionals, outlining cyber threats and the technologies for defending against them.

 Securityweek.com
Securityweek.com
Cybersecurity News, Insights and Analysis | SecurityWeek
SecurityWeek provides cybersecurity news and information to global enterprises, with expert insights and analysis for IT security professionals.

 Sans.org
Sans.org
Cyber Security Training | SANS Courses, Certifications & Research
SANS Institute is the most trusted resource for cybersecurity training, certifications and research. Offering more than 60 courses across all practice areas, SANS trains over 40,000 cybersecurity professionals annually.

 Concise-courses.com
Concise-courses.com
Resource For Hacker Tools & Growth / SEO Hacking Tools
Site Dedicated To Intrepid SEO Explorers

 Beyondtrust.com
Beyondtrust.com
Privileged Access Management, Cyber Security, and Remote Access (formerly Bomgar) | BeyondTrust
Unwanted remote access, stolen credentials, and misused privileges threaten every organization. BeyondTrust offers the industry’s broadest set of privileged access management capabilities to defend against cyber attacks. Our Privileged Access Management platform provides visibility and control over all privileged accounts, users, and access. Trusted by more than 20,000 companies and counting.

 Controlscan.com
Controlscan.com
VikingCloud - Cybersecurity Intelligence
Viking Cloud offers cloud-native predictive algorithms and innovative technologies help keep your organization safe. The Business Solutions division of Sysnet Global Solutions.

 Thycotic.com
Thycotic.com
Privileged Access Management (PAM) Solutions | Software
One of the most full-featured privileged access management (PAM) solutions available is easy to use, well adopted and affordable. Free trial.
 Sailpoint.com
Sailpoint.com
SailPoint | Identity Security for the Cloud Enterprise
Securing modern enterprises has moved beyond human capacity. Discover the core of Identity Security.

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.
 Imperva.com
Imperva.com
Cyber Security Leader | Imperva, Inc.
Imperva provides complete cyber security by protecting what really matters most—your data and applications—whether on-premises or in the cloud.

 Securitymetrics.com
Securitymetrics.com
PCI Compliance | HIPAA Security Assessment | SecurityMetrics
Protect your network and your customers with PCI and HIPAA compliance assessments from SecurityMetrics. We offer a full line of data security solutions.

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.

 Seclists.org
Seclists.org
SecLists.Org Security Mailing List Archive
Security mailing list archive for the Nmap lists, Bugtraq, Full Disclosure, Security Basics, Pen-test, and dozens more. Search capabilities and RSS feeds with smart excerpts are available
 Sectools.org
Sectools.org
SecTools.Org Top Network Security Tools
Rankings and reviews of computer and network security software, programs, and tools.

 Esecurityplanet.com
Esecurityplanet.com
eSecurity Planet: Latest Cybersecurity News for IT Professionals
eSecurity Planet provides the latest cybersecurity news, trends, and software reviews for IT leaders. Browse our buyer's guides and analysis now.
 Eccouncil.org
Eccouncil.org
Certified Ethical Hacker | InfoSec Cyber Security Certification | EC-Council
EC-Council is a global leader in InfoSec Cyber Security certification programs like Certified Ethical Hacker and Computer Hacking Forensic Investigator.

 Ixiacom.com
Ixiacom.com
Network Visibility and Network Test Products | Keysight
Use Ixia (Keysight) market-leading network test, visibility, performance monitoring, and security solutions to build and manage more secure, and reliable networks.
 Csoonline.com
Csoonline.com
CSO - CSO Online – IT-Security-News für Profis
News und Insights zur Cybersicherheit im Unternehmen. Alles was CSOs wissen müssen.
Technologies Used by coresecurity.com
Dns Records of coresecurity.com
A Record: 23.185.0.1AAAA Record: 2620:12a:8000::1 2620:12a:8001::1
CNAME Record:
NS Record: ns-860.awsdns-43.net ns-1999.awsdns-57.co.uk ns-170.awsdns-21.com ns-1522.awsdns-62.org
SOA Record: awsdns-hostmaster.amazon.com
MX Record: awsseg01.helpsystems.com awsseg02.helpsystems.com
SRV Record:
TXT Record: v=spf1 ip4:181.119.128.201 ip4:208.42.93.45 ip4:181.119.128.200/32 ip4:208.88.166.157/32 ip4:212.54.152.16 include:spf.protection.outlook.com include:u2621334.wl085.sendgrid.net include:mail.zendesk.com include:_spf.salesforce.com include:spf-sigstr1.sigstr.com include:aspmx.pardot.com ~all MS=ms79554710
DNSKEY Record:
CAA Record:
Whois Detail of coresecurity.com
Domain Name: coresecurity.comRegistry Domain ID: 84967836_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.registrar.amazon.com
Registrar URL: https://registrar.amazon.com
Updated Date: 2022-02-22T02:56:27.520Z
Creation Date: 2002-03-28T15:41:25Z
Registrar Registration Expiration Date: 2023-03-28T14:41:25Z
Registrar: Amazon Registrar, Inc.
Registrar IANA ID: 468
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +1.2067406200
Reseller:
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Domain Status: renewPeriod https://icann.org/epp#renewPeriod
Registry Registrant ID:
Registrant Name: On behalf of coresecurity.com owner
Registrant Organization: Whois Privacy Service
Registrant Street: P.O. Box 81226
Registrant City: Seattle
Registrant State/Province: WA
Registrant Postal Code: 98108-1226
Registrant Country: US
Registrant Phone: +1.2065771368
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID:
Admin Name: On behalf of coresecurity.com administrative contact
Admin Organization: Whois Privacy Service
Admin Street: P.O. Box 81226
Admin City: Seattle
Admin State/Province: WA
Admin Postal Code: 98108-1226
Admin Country: US
Admin Phone: +1.2065771368
Admin Phone Ext:
Admin Fax:
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID:
Tech Name: On behalf of coresecurity.com technical contact
Tech Organization: Whois Privacy Service
Tech Street: P.O. Box 81226
Tech City: Seattle
Tech State/Province: WA
Tech Postal Code: 98108-1226
Tech Country: US
Tech Phone: +1.2065771368
Tech Phone Ext:
Tech Fax:
Tech Fax Ext:
Tech Email: [email protected]
Name Server: ns-1522.awsdns-62.org
Name Server: ns-170.awsdns-21.com
Name Server: ns-1999.awsdns-57.co.uk
Name Server: ns-860.awsdns-43.net
DNSSEC: unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-02-22T02:56:27.734Z <<<
For more information on Whois status codes, please visit https://www.icann.org/resources/pages/epp
By submitting a query to the Amazon Registrar, Inc. WHOIS database, you agree to abide by the following terms. The data in Amazon Registrar, Inc.'s WHOIS database is provided by Amazon Registrar, Inc. for the sole purpose of assisting you in obtaining information about domain name accuracy. You agree to use this data only for lawful purposes and further agree not to use this data for any unlawful purpose or to: (1) enable, allow, or otherwise support the transmission by email, telephone, or facsimile of commercial advertising or unsolicited bulk email, or (2) enable high volume, automated, electronic processes to collect or compile this data for any purpose, including mining this data for your own personal or commercial purposes. Amazon Registrar, Inc. reserves the right to restrict or terminate your access to the data if you fail to abide by these terms of use. Amazon Registrar, Inc. reserves the right to modify these terms at any time.
Visit Amazon Registrar, Inc. at https://registrar.amazon.com
Contact information available here: https://docs.aws.amazon.com/Route53/latest/DeveloperGuide/domain-contact-support.html
© 2022, Amazon.com, Inc., or its affiliates
 40.113.224.207
40.113.224.207
 United States
United States
 InValid
SSL
InValid
SSL