Invicti | Web Application Security For Enterprise
Get accurate, automated application security testing that scales like no other solution. Secure 1000s of web assets with less manual effort. Reduce your risk with the only…

Stats
Alexa Rank:
Popular in Country:
Country Alexa Rank:
language: en
Response Time: 0.740969
SSL: Enable
Status: up
Code To Txt Ratio
Word Count 845
Links
ratio 28.260343576095
SSL Details
SSL Issuer:
Issuer: Gandi Standard SSL CA 2
Valid From: 2022-01-12 00:00:00
Expiration Date: 2023-02-03 23:59:59
SSL Organization:
Signature 6be8996c44d188a7d7fb6b7249db1e6b54fe2211
Algorithm: RSA-SHA256
Found 73 Top Alternative to Netsparker.com

 Acunetix.com
Acunetix.com
Acunetix | Web Application Security Scanner
Acunetix is an end-to-end web security scanner that offers a 360 view of an organization’s security. Allowing you to take control of the security of all you web applications, web services, and APIs to ensure long-term protection. Acunetix’s scanning engine is globally known and trusted for its unbeatable speed and precision.

 Portswigger.net
Portswigger.net
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.

 Owasp.org
Owasp.org
OWASP Foundation | Open Source Foundation for Application Security
OWASP Foundation, the Open Source Foundation for Application Security on the main website for The OWASP Foundation. OWASP is a nonprofit foundation that works to improve the security of software.

 Veracode.com
Veracode.com
Confidently secure apps you build and manage with Veracode
This simple and scalable solution enables you to create more secure software so that you can boost your business and reduce risk without hindering innovation.

 Detectify.com
Detectify.com
Attack Surface Management Tool Powered By Ethical Hackers | Detectify
Detectify's external attack surface management tool - assess, prioritize, remediate continuously growing external attack surfaces.
 Hackerone.com
Hackerone.com
HackerOne | #1 Trusted Security Platform and Hacker Program
Reduce your cybersecurity risk/vulnerabilities through bug bounty programs, VDPs, attack resistance management, attack surface management, security assessments, and pentest solutions.


 Rapid7.com
Rapid7.com
Cybersecurity & Compliance Solutions & Services | Rapid7
Supercharge your security impact with Rapid7, delivering shared visibility, analytics, and automation to unite security, IT, and DevOps teams.

 Mitre.org
Mitre.org
The MITRE Corporation
About Corporate Overview Our History Mission and Values Visiting MITRE Leadership Executive Team Board of Trustees Fellows Technical Fellows Visiting Fellows Awards and Recognition Corporate Social Responsibility Building a Foundation for the Future MITRE Staff Cultivates Los Angeles' Science Ecosystem Bringing Real World STEM to Students Building Partnerships and Diversity,...
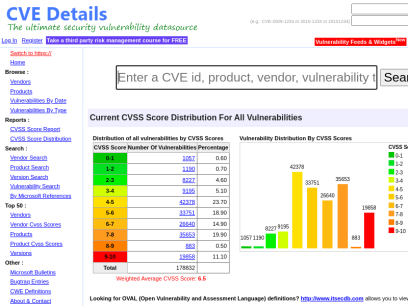
 Cvedetails.com
Cvedetails.com
CVE security vulnerability database. Security vulnerabilities, exploits, references and more
CVEdetails.com is a free CVE security vulnerability database/information source. You can view CVE vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time
 Imperva.com
Imperva.com
Cyber Security Leader | Imperva, Inc.
Imperva provides complete cyber security by protecting what really matters most—your data and applications—whether on-premises or in the cloud.
 Hackertarget.com
Hackertarget.com
28 Online Vulnerability Scanners & Network Tools | HackerTarget.com
Online Vulnerability Scanners to map the attack surface and identify vulnerabilities. 28 trusted open source security scanners and network tools.


 Bugcrowd.com
Bugcrowd.com
#1 Crowdsourced Cybersecurity Platform | Bugcrowd
Bugcrowd teams with elite security researchers to reduce risk & improve security ROI through our bug bounty, pen testing, & vulnerability disclosure programs.

 Infosecinstitute.com
Infosecinstitute.com
IT & Security Education, Certifications, Awareness & Phishing Simulator - Infosec
Infosec helps IT and security professionals advance their careers with skills development and certifications while empowering all employees with security awareness and privacy training to stay cyber-safe at work and home.
 Tenable.com
Tenable.com
Tenable® - The Cyber Exposure Company
Welcome to the modern era of cyber exposure. Join the movement.
 Ptsecurity.com
Ptsecurity.com
Positive Technologies - vulnerability assessment, compliance management and threat analysis solutions
Positive Technologies - vulnerability assessment, compliance management and threat analysis solutions

 Qualys.com
Qualys.com
Information Security and Compliance | Qualys
Qualys, Inc. helps your business automate the full spectrum of auditing, compliance and protection of your IT systems and web applications.
 Securityidiots.com
Securityidiots.com
Welcome to Security Idiots!!
Security Idiots is a place where some insane idiots try thier hands on with Security.

 Checkmarx.com
Checkmarx.com
Application Security Testing Company | Software Security Testing Solutions | Checkmarx
Checkmarx – As the leader in application security testing, we make security simple and seamless for developers through industry-defining innovation. Get a demo of our top software security solutions & services.

 Netsparker.com.tr
Netsparker.com.tr
Netsparker Türkiye - Web Uygulaması Güvenlik Tarayıcısı
Web siteleriniz ve web servislerinizdeki güvenlik açıklarını otomatik olarak tespit eden, false-positive (hatalı) bulgu raporlamayan, hızlı ve kullanımı kolay web uygulama güvenliği tarayıcıları.

 Cybersecurity-help.cz
Cybersecurity-help.cz
Vulnerability Intelligence by CyberSecurity Help s.r.o.
Actionable vulnerability intelligence for every company.
 Kitploit.com
Kitploit.com
KitPloit - PenTest & Hacking Tools
Leading source of security tools, hacking tools, cybersecurity and network security. Learn about new tools and updates in one place.

 Geekflare.com
Geekflare.com
Geekflare - Technology Articles, Tools and APIs to help you grow.
Geekflare produces high-quality technology & finance articles, makes tools, and APIs to help businesses and people grow.

 Indusface.com
Indusface.com
Web Application Security, WAF, SSL Certificates
Indusface offers web app security, WAF and SSL Certificates to keep your business safe. Securing thousands of application security companies day to day.

 Packetstormsecurity.com
Packetstormsecurity.com
Packet Storm
Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers
 Nmap.org
Nmap.org
Nmap: the Network Mapper - Free Security Scanner
Nmap Free Security Scanner, Port Scanner, & Network Exploration Tool. Download open source software for Linux, Windows, UNIX, FreeBSD, etc.

 Pentestmonkey.net
Pentestmonkey.net
pentestmonkey | Taking the monkey work out of pentesting
mimikatz: Tool To Recover Cleartext Passwords From Lsass December 20, 2011, pentestmonkey I meant to blog about this a while ago, but never got round to it. Here’s a brief post about very cool feature of a tool called mimikatz. I’m very grateful to the tool’s author for bringing it...

 Sans.org
Sans.org
Cyber Security Training | SANS Courses, Certifications & Research
SANS Institute is the most trusted resource for cybersecurity training, certifications and research. Offering more than 60 courses across all practice areas, SANS trains over 40,000 cybersecurity professionals annually.
 Snyk.io
Snyk.io
Snyk | Developer security | Develop fast. Stay secure.
Snyk helps software-driven businesses develop fast and stay secure. Continuously find and fix vulnerabilities for npm, Maven, NuGet, RubyGems, PyPI and more.

 Hackthebox.eu
Hackthebox.eu
Hack The Box: Hacking Training For The Best | Individuals & Companies
Where hackers level up! An online cybersecurity training platform allowing IT professionals to advance their ethical hacking skills and be part of a worldwide community. Join today and learn how to hack!
 Xsshunter.com
Xsshunter.com
XSS Hunter
...you may be missing the most critical vulnerabilities! XSS Hunter is a better way to do Cross-site Scripting. Learn more about how XSS Hunter can help you find even blind XSS...

 W3af.org
W3af.org
w3af - Open Source Web Application Security Scanner
w3af is a Web Application Attack and Audit Framework. The project's goal is to create a framework to find and exploit web application vulnerabilities that

 Troyhunt.com
Troyhunt.com
Troy Hunt: Troy Hunt
Hi, I'm Troy Hunt, I write this blog, run "Have I Been Pwned" and am a Microsoft Regional Director and MVP who travels the world speaking at events and training technology professionals
 Cxsecurity.com
Cxsecurity.com
CXSECURITY.COM Free Security List
CXSECURITY (Independent information about security) is a huge collection of information on data communications safety. Its main objective is to inform about errors in various applications.

 Beyondsecurity.com
Beyondsecurity.com
Beyond Security | Automated Vulnerability Security Testing & Compliance
Secure your applications and networks with the industry's only network vulnerability scanner to combine XDR, SAST, DAST and mobile security.
 Eccouncil.org
Eccouncil.org
Certified Ethical Hacker | InfoSec Cyber Security Certification | EC-Council
EC-Council is a global leader in InfoSec Cyber Security certification programs like Certified Ethical Hacker and Computer Hacking Forensic Investigator.

 Blackhat.com
Blackhat.com
Black Hat | Home
Black Hat Webinars Security Research in Real Time June 30, 2022 - Managing Cybersecurity as a Business Risk July 14, 2022 - InfoSec Lessons from the War in Ukraine Sponsor a Webinars View all of our recent Webinars Black Hat Archives Watch Past Presentations View all of our archived videos...
 Sqlmap.org
Sqlmap.org
sqlmap: automatic SQL injection and database takeover tool
Introduction sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. It comes with a powerful detection engine, many niche features for the ultimate penetration tester and a broad range of switches lasting from database...
 Metasploit.com
Metasploit.com
Metasploit | Penetration Testing Software, Pen Testing Security | Metasploit
Find security issues, verify vulnerability mitigations & manage security assessments with Metasploit. Get the world's best penetration testing software now.

 Intigriti.com
Intigriti.com
Intigriti - Bug Bounty & Agile Pentesting Platform
Intigriti offers bug bounty and agile penetration testing solutions powered by Europe's #1 leading network of ethical hackers.

 Webarxsecurity.com
Webarxsecurity.com
Identify Plugin Vulnerabilities In Your WordPress Sites - Patchstack
Protect websites from plugin vulnerabilities with Patchstack. Be first to receive protection from new security vulnerabilities.

 Kali.org
Kali.org
Kali Linux | Penetration Testing and Ethical Hacking Linux Distribution
Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking and network security assessments.
 Crackstation.net
Crackstation.net
CrackStation - Online Password Hash Cracking - MD5, SHA1, Linux, Rainbow Tables, etc.
Crackstation is the most effective hash cracking service. We crack: MD5, SHA1, SHA2, WPA, and much more...
 Cybrary.it
Cybrary.it
Free Cybersecurity Training and Career Development | Cybrary
Cybersecurity training from Cybrary will take your career to the next level. We have the cybersecurity courses that can help get you there!

 Pentester.land
Pentester.land
Pentester Land · Offensive Infosec
The newsletter is dead, long live the newsletter! 12 Jul 2020 • newsletter This is a long due post. Since The 5 Hacking Newsletter has stopped on this blog, I’ve been getting many questions about it. So, even though most readers already know by now, here’s a summary of what...

 Tryhackme.com
Tryhackme.com
TryHackMe | Cyber Security Training
TryHackMe is a free online platform for learning cyber security, using hands-on exercises and labs, all through your browser!

 Darknet.org.uk
Darknet.org.uk
Darknet - Hacking Tools, Hacker News & Cyber Security
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing.

 Hacker101.com
Hacker101.com
Home | Hacker101
Hacker101 is a free class for web security. Whether you’re a programmer with an interest in bug bounties or a seasoned security professional, Hacker101 has something to teach you.
 Malcare.com
Malcare.com
Home - Malcare
MalCare will keep your site secure without slowing it down. Get automatic malware scans, one-click malware removal and a real-time firewall for complete

 Vuldb.com
Vuldb.com
Vulnerability Database
Number one vulnerability database documenting and explaining security vulnerabilities, threats, and exploits since 1970.

 Upguard.com
Upguard.com
Third-Party Risk and Attack Surface Management Software | UpGuard
Third-party risk and attack surface management software. UpGuard is the best platform for securing your organization’s sensitive data. Our security ratings engine monitors millions of companies and billions of data points every day.
 Gf.dev
Gf.dev
Tools for Webmasters, Web Engineers, Security Analysts, and SEO Experts - Geekflare Tools
FREE tools to test your website performance, domain security, whois hosting, screenshot, PING, traceroute and more

 Wpsec.com
Wpsec.com
Online WordPress Security Scan for Vulnerabilities | WP Sec
WPSec.com is an online WordPress security scan for detecting and reporting WordPress vulnerabilities.


 Suip.biz
Suip.biz
Welcome!
Online services based on Miloserdov.org IP Ranges Composing Browsable location lists and their IP addresses All IP of locality (region, city) All IP of countries All IP of ISPs All IP of continents All IP of Autonomous System (AS) IP ranges of all Internet Service Providers (ISPs) and organizations Find...
 Base64encode.org
Base64encode.org
Base64 Encode and Decode - Online
Encode to Base64 format or decode from it with various advanced options. Our site has an easy to use online tool to convert your data.
 Alvinalexander.com
Alvinalexander.com
Scala, Java, Unix, MacOS tutorials (page 1) | alvinalexander.com
Free Scala, Java, Unix, MacOS tutorials (page 1)

 Alertlogic.com
Alertlogic.com
Managed Detection and Response (MDR) Company | Alert Logic
Alert Logic’s Managed Detection and Response platform provides 24/7 protection against constantly evolving cyber attacks. Protect your company now!
 Hashes.com
Hashes.com
Decrypt MD5, SHA1, MySQL, NTLM, SHA256, SHA512, Wordpress, Bcrypt hashes for free online
Decrypt and crack your MD5, SHA1, SHA256, MySQL, and NTLM hashes for free online. We also support Bcrypt, SHA512, Wordpress and many more.
Technologies Used by netsparker.com
Dns Records of netsparker.com
A Record: 52.203.139.57 34.195.4.141AAAA Record:
CNAME Record:
NS Record: ns-769.awsdns-32.net ns-339.awsdns-42.com ns-1881.awsdns-43.co.uk ns-1326.awsdns-37.org
SOA Record: awsdns-hostmaster.amazon.com
MX Record: alt2.aspmx.l.google.com alt1.aspmx.l.google.com aspmx.l.google.com aspmx3.googlemail.com aspmx2.googlemail.com
SRV Record:
TXT Record: docusign=b132bca0-5cfc-4f0b-bad8-802c81700142 MS=ms26051574 v=spf1 include:servers.mcsv.net include:spf.mtasv.net include:mail.zendesk.com include:_spf.google.com -all pardot869541=6d134c9a42d6fba5862f4aa795b394b5af9e4c6057395cc3a5f9c3971f669f21 google-site-verification=Dw9u5XqK_-PsDkPoCV6oGdtlJn5wUYSrcvLthWg_FnM
DNSKEY Record:
CAA Record:
Whois Detail of netsparker.com
Domain Name: netsparker.comRegistry Domain ID: 1567481541_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.gandi.net
Registrar URL: http://www.gandi.net
Updated Date: 2021-11-15T06:41:50Z
Creation Date: 2009-08-31T12:51:49Z
Registrar Registration Expiration Date: 2023-08-31T14:51:49Z
Registrar: GANDI SAS
Registrar IANA ID: 81
Registrar Abuse Contact Email: [email protected]
Registrar Abuse Contact Phone: +33.170377661
Reseller:
Domain Status: clientTransferProhibited http://www.icann.org/epp#clientTransferProhibited
Domain Status:
Domain Status:
Domain Status:
Domain Status:
Registry Registrant ID: REDACTED FOR PRIVACY
Registrant Name: REDACTED FOR PRIVACY
Registrant Organization: Netsparker Ltd.
Registrant Street: REDACTED FOR PRIVACY
Registrant City: REDACTED FOR PRIVACY
Registrant State/Province:
Registrant Postal Code: REDACTED FOR PRIVACY
Registrant Country: GB
Registrant Phone: REDACTED FOR PRIVACY
Registrant Phone Ext:
Registrant Fax: REDACTED FOR PRIVACY
Registrant Fax Ext:
Registrant Email: [email protected]
Registry Admin ID: REDACTED FOR PRIVACY
Admin Name: REDACTED FOR PRIVACY
Admin Organization: REDACTED FOR PRIVACY
Admin Street: REDACTED FOR PRIVACY
Admin City: REDACTED FOR PRIVACY
Admin State/Province: REDACTED FOR PRIVACY
Admin Postal Code: REDACTED FOR PRIVACY
Admin Country: REDACTED FOR PRIVACY
Admin Phone: REDACTED FOR PRIVACY
Admin Phone Ext:
Admin Fax: REDACTED FOR PRIVACY
Admin Fax Ext:
Admin Email: [email protected]
Registry Tech ID: REDACTED FOR PRIVACY
Tech Name: REDACTED FOR PRIVACY
Tech Organization: REDACTED FOR PRIVACY
Tech Street: REDACTED FOR PRIVACY
Tech City: REDACTED FOR PRIVACY
Tech State/Province: REDACTED FOR PRIVACY
Tech Postal Code: REDACTED FOR PRIVACY
Tech Country: REDACTED FOR PRIVACY
Tech Phone: REDACTED FOR PRIVACY
Tech Phone Ext:
Tech Fax: REDACTED FOR PRIVACY
Tech Fax Ext:
Tech Email: [email protected]
Name Server: NS-1881.AWSDNS-43.CO.UK
Name Server: NS-769.AWSDNS-32.NET
Name Server: NS-339.AWSDNS-42.COM
Name Server: NS-1326.AWSDNS-37.ORG
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
Name Server:
DNSSEC: Unsigned
URL of the ICANN WHOIS Data Problem Reporting System: http://wdprs.internic.net/
>>> Last update of WHOIS database: 2022-06-21T05:44:48Z <<<
For more information on Whois status codes, please visit
https://www.icann.org/epp
Reseller Email:
Reseller URL:
Personal data access and use are governed by French law, any use for the purpose of unsolicited mass commercial advertising as well as any mass or automated inquiries (for any intent other than the registration or modification of a domain name) are strictly forbidden. Copy of whole or part of our database without Gandi's endorsement is strictly forbidden.
A dispute over the ownership of a domain name may be subject to the alternate procedure established by the Registry in question or brought before the courts.
For additional information, please contact us via the following form:
https://www.gandi.net/support/contacter/mail/
 3.209.17.81
3.209.17.81
 United States
United States
 Valid SSL
Valid SSL